What Is DevSecOps? 5 Key Components for Secure Delivery
You’ve probably heard the term DevSecOps thrown around a lot in recent years, and for good reasons. The software industry is more competitive than ever and paired with a shift in consumer expectations, today’s development organizations often race against the clock to get the next innovative app to the market. Security is often sacrificed in the pursuit of speed.
Unfortunately, many organizations have learned the hard way that the price of neglecting security to get to market quickly is too high.
Does the recent Solarwinds episode ring a bell? In this attack, the major info-tech firm Solarwinds became the victim of hackers who breached security controls and added malicious code to their systems. The attack went unnoticed for months, allowing the threat actors to spy on Solarwinds’ clients and access their sensitive data.
From stiff regulatory fines and civil damages to severe reputational hits from publicized breaches, releasing software with security flaws is a bad business practice. Security has to be embedded firmly within the software development process, and that’s what DevSecOps is all about. In this article, you will learn about the DevSecOps methodology, the key concepts behind the methodology, and how to introduce it into your organization.
DevSecOps definition and meaning
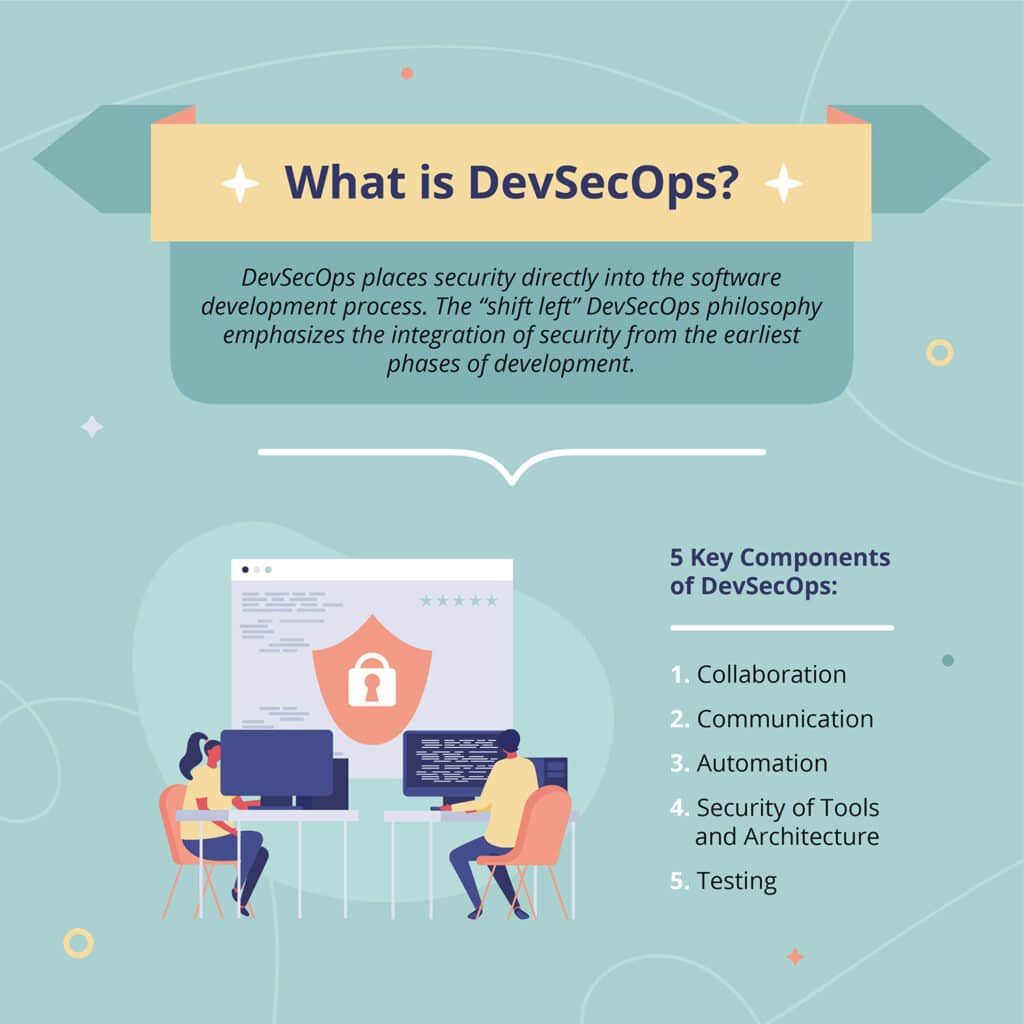
DevSecOps is a software development approach that integrates security (Sec) into development (Dev) and operations (Ops) so that security is built into every stage of the software delivery lifecycle instead of being bolted on at the end. In practical terms, the DevSecOps approach means automating security checks, giving developers security tools in their daily workflows, and treating security as a shared responsibility across development, operations, and security teams.
The simplest way to understand DevSecOps is to start with the spelling of the word, where “security” is placed between “development” and “operations.” The “shift-left” DevSecOps philosophy emphasizes integrating security from the earliest phases of development – in other words, baking security into the code, not patching it later.
Many view DevSecOps as the next level of DevOps, where traditional department silos dissolve, security takes a seat at the table during design, and a new culture of shared responsibility for security emerges. This shared ownership model attempts to unify historically siloed camps – developers and IT security professionals – around a common goal of optimized innovation and speed to market without sacrificing security and compliance. DevSecOps attempts to strike a balance between agility and safety by embedding security processes and practices into developers’ daily workflow. Similar to DevOps, DevSecOps is fueled by automation at every turn.
Additional resource: Getting familiar with DevOps practices
DevSecOps principles – what the DevSecOps approach solves
Traditionally, development and security teams existed at odds, with developers favoring innovation and speed while security teams stressed security and compliance. The DevSecOps approach was created to remove this friction by giving both sides a common, automated workflow where security checks happen early and often. Developers viewed security as a bureaucratic hindrance to progress, rolling their eyes as security teams conducted last-minute checks before product release. Security was always last in the room, which means that security flaws are often discovered far too late within the production environment. When that happens, developers must halt work on all new features and retroactively apply security fixes, costing extra time and money.
As Keatron Evans, Infosec Skills Author and consultant at the Infosec Institute, explains, “Looking at most DevOps organizations, security is something thought about most commonly at the very end, and even in best case scenarios in the middle of the development process, and at that point it’s already too late”.
There must be a better way, right?
With DevSecOps, development, operations, testing, and security teams collaborate and combine resources to catch security issues earlier in the development process. Development isn’t stalled, and the end result is a safer, higher-quality application created in a faster, more efficient workflow.
If you’re an IT security professional, DevSecOps is the ticket to your rightful place at the table. No longer viewed as a burdensome impediment, your team’s input will be valued from the beginning of development, and your organization will look to you as a leader in the security integration movement.
And if you’re a developer, you should share the excitement for DevSecOps. Security isn’t going anywhere, and in the end, treating it as a last-minute bolt-on is only slowing down your progress. Security is a critical component of software quality today and one your customers will thank you for.
The core principle of DevSecOps
The core principle of DevSecOps is that security is everyone’s job. Instead of security teams acting as a final gate, developers, operations, and security professionals collaborate from day one, using automation and shared tooling so that security checks happen continuously as code is written, tested, and deployed.
5 key components of DevSecOps
Together, these five elements form a practical DevSecOps approach that teams can use to move from theory to day-to-day practice.
1. Collaboration
Collaboration starts with creating a shared-responsibility mindset regarding security across the organization, backed by the endorsement of executive leadership. Collaboration is cemented around a common goal of developing and releasing the highest-quality product as fast as possible while meeting all security and compliance requirements.
Security teams do their part, starting by familiarizing themselves with DevOps practices and integrating them into security. Examples of this would be delivering security capabilities in small, frequent installments and automating security tasks whenever possible. Developers, in turn, should learn about security best practices, requirements, threat awareness, and tools.

2. Communication
The communications gap between developers and security pros must be bridged. Security pros must articulate the need for controls and the benefits of compliance in developers’ terms. For example, discussing security risks in terms of project delays and unplanned extra work for developers will drive the importance of addressing those risks home.
Developers should clearly understand their security-related responsibilities so they can fully embrace their role as contributing partners in a more secure and compliant organization. These responsibilities include being aware of potential security risks and writing code with security best practices in mind. Developers should also be prepared to conduct vulnerability testing throughout development, fixing flaws as they are discovered.
3. Automation
Automation may be the most critical component of a successful DevSecOps initiative. It allows security measures to become embedded within the development process and ensures that security doesn’t become a burden for development teams. Automated security testing and analysis can be integrated throughout CI/CD pipelines, delivering safe software without slowing innovation and development workflows. Now both developers and security teams are happy–a huge step in validating your DevSecOps program and keeping everyone on board.
Automation also enables valuable security controls like “break the build.” This security failsafe mechanism is based on an automated risk scoring system that alerts someone when risk exceeds a predetermined threshold. At this point, all building processes freeze until developers remedy the security issue. Once the security issue is fixed, developers may finish the build and deliver the application.
4. Security of tools and architecture
Secure software starts with safe DevOps environments. Protecting tools, access, and architecture is critical in any DevOps system. Security teams should take the lead to select and check all system security tools’ configurations to ensure proper function before these systems are approved for widespread use.
Identification and access management should be taken seriously. Security teams should control access to DevOps architecture and data, protecting credentialed usage throughout the development pipeline. Multi-factor authentication (MFA), least-privileged access, and just-in-time temporary access to high-level privileges are all tactics you can leverage to control access. Further, CI/CD pipelines should be segregated to limit lateral movement, and all unnecessary accounts with access to DevOps tools should be eliminated.
With DevSecOps, security and compliance controls are baked into the infrastructure to cover all environments, including the cloud. All workstations and servers undergo regular security monitoring, vulnerability scanning, and patching. Automated tools are used to scan all code, ensuring there are no secrets when checking into repositories. Also, all new VMs and containers automatically receive properly configured controls to help withstand automatic rebuilds. Centralized storage systems house DevOps tools and secrets, all protected with encryption and multi-factor authentication (MFA).
5. Testing
Historically, security tests run as the last step before product release. Ideally, testing should occur throughout the entire development process. Keatron Evans explains, “Traditionally, apps test upon completion, but it would be much more effective if developers tested on an automated, ongoing basis. Instead of testing a completely built app, developers should be able to do basic OWASP top-ten testing throughout the development process, as this would solve half the cybersecurity problems out there”.
To keep security on pace with development, the infusion of automated testing is critical. Automation can help with simple processes like scanning code for secrets before code is checked into repositories, ensuring passwords aren’t recorded in event logs, and scouring apps for malicious code.
Effective testing regimens include a combination of static application security testing (SAST), dynamic application security testing (DAST), and less frequent but equally essential techniques like penetration testing, Red Teaming, and Threat Modeling. These latter approaches can be valuable as they approach code from a hacker’s perspective without disrupting the production environment. Many organizations now incentivize thorough testing with “bug bounty” programs, rewarding the reporting of potential security issues.
DevSecOps assesses testing mechanisms by monitoring key metrics to gauge improvements in risk reduction and the overall effectiveness of security practices across the development process. Developers receive self-assessment scorecards, keeping them honest and accountable with a variety of relevant questions. For instance, are attack surfaces being reduced? Is credential misuse getting detected? Our penetration tests showing fewer code vulnerabilities? What is the percent of code commits containing secrets?
How to introduce DevSecOps to your organization
Transitioning to a DevSecOps methodology will take time. To ensure buy-in across your organization, we recommend taking an incremental approach. Here are some key tips to remember when introducing a DevSecOps initiative:
- Institute an organization-wide, security-centric culture emphasizing that security is now a shared responsibility
- Find ways to integrate automated security testing early and often throughout the development process
- Lead with security awareness training programs to educate developers on security threats, secure coding requirements, and tools
- Expose developers to current hacking techniques, teaching them to think and attack code like hackers
- Have security teams deliver a robust dose of penetration testing, Red Team exercises, and threat modeling to aggressively test code
- Monitor security issues in shared tracking systems for maximum visibility across all departments
- Provide relevant metrics to demonstrate improvement over time and the value of your DevSecOps program
- Recognize that it will take time for developers to fully shift their mindset and habits. Continue to emphasize security concepts and raise awareness during daily activities
Additional Resource: How Security Assurance Teams Can Use DevOps Principles to Become More Productive and Happier
Achieve DevSecOps certification and training
Considering the relative newness and evolving importance of DevSecOps, it may be worthwhile to invest in training that explains the DevSecOps meaning, principles, and hands-on practices. If DevSecOps is a completely fresh idea for your organization, having members from Development and Operations teams get trained together can be integral to the future success of a DevSecOps program
Through DevSecOps training, organizations can learn everything from DevSecOps principles and the culture that needs to be fostered around it, to developing frameworks and key security automations that should be built. There is a plethora of DevSecOps training and certification programs, no matter how far along your organization is in the adoption of DevSecOps. It is important to take the time to research which training might be right for you.
Check out these courses from The Linux Foundation and Practical DevSecOps.
Aside from the obvious benefits of investing time and resources into DevSecOps training, completing a DevSecOps program can help to create visibility and instill trust across your organization. As mentioned above, to be successful, DevSecOps requires buy-in from multiple departments. With this in mind, obtaining training and certification will help to show your entire organization that DevSecOps is worth developing.
Hire a Certified DevSecOps Professional (CDP) | DevSecOps engineer
If DevSecOps is important to your organization, hiring a Certified DevSecOps Professional (CDP) or DevSecOps Engineer should be a priority. A dedicated CDP or engineer can help to create, implement, and manage a DevSecOps program. On top of this, the professional will be able to identify any gaps or potential weaknesses in your organization’s current DevSecOps program and then create solutions to fix any issues. While the upfront investment in a new employee might be hefty, in the long run, hiring a dedicated DevSecOps person could help to protect your organization from numerous security incidents.
DevSecOps FAQs
What is the meaning of DevSecOps?
DevSecOps means integrating security practices and tools into every stage of the software development and operations lifecycle so that security becomes a built-in, continuous process instead of a final, one-time check.
What is the core principle of DevSecOps?
The core principle of DevSecOps is shared responsibility for security: developers, operations, and security teams all own security outcomes and use automation to embed security into their everyday workflows.
How does the DevSecOps approach differ from traditional DevOps?
Traditional DevOps focuses on speed and collaboration between development and operations, often leaving security as a separate, downstream step. The DevSecOps approach adds security into that same loop, using automated testing, secure coding practices, and continuous monitoring to keep releases fast *and* secure.
Final thoughts
DevSecOps will grow in importance as businesses continue to leverage cloud services and customers in all industries become more sensitive to the security posture of their vendors.
Keatron Evans addresses these current trends while providing perhaps the most substantial justification for embracing DevSecOps: “DevSecOps is so important today because 95% of Fortune 500 companies are 50% or more in the cloud. And how do we access the cloud? Through applications. DevSecOps is how we secure applications. If your organization is going to compete securely now and in the future, you will need to implement DevSecOps.”
Thankfully, security has finally found its place in development, and with the arrival of DevSecOps, today’s developers and security teams can have it all. Innovation doesn’t need to be sacrificed for security, and security needn’t suffer in the pursuit of performance and speed. The time for developers and security professionals to unite together to deliver secure, quality, high-performance, and compliant software has arrived. The time for DevSecOps is now.
See Hyperproof in Action
Related Resources
Ready to see
Hyperproof in action?











