Cyber Risk Quantification: How to Report Risks to Your CFO
Cyber risk quantification supports business decision-making by converting risks into dollar values so that leaders can compare security investments with other financial priorities using three primary methods:
- Estimating expected annual loss
- Applying structured risk frameworks like FAIR
- Conducting probability-impact analysis
By estimating the likelihood of incidents, the potential impact on revenue, legal costs, and supply-chain disruption, the method produces an annualized loss figure that can be entered directly into budgeting and strategic planning models.
For chief financial officers, quantified risk delivers defensible numbers that help to satisfy regulatory reporting requirements, like the SEC’s 2023 disclosure rules. Loss estimates reveal how a breach could depress stock prices, raise insurance premiums, or cause customer churn, informing capital allocation and insurance purchasing decisions.
The visibility also meets investor expectations for transparent risk communication, strengthening confidence in the organization’s financial stability. Turning cyber risk into dollars gives decision makers the evidence needed to prioritize resources, justify spending, and protect overall enterprise value.
Frameworks like FAIR guide analysts to calculate a probable loss amount, while the NIST risk management framework provides a structured assessment process. FAIR analyses are typically run in specialized risk-quant tools, then summarized for executive reporting. Translating technical data into monetary terms creates a common language for IT, finance, and executive teams, reducing ambiguity and enabling clearer trade-off analysis.
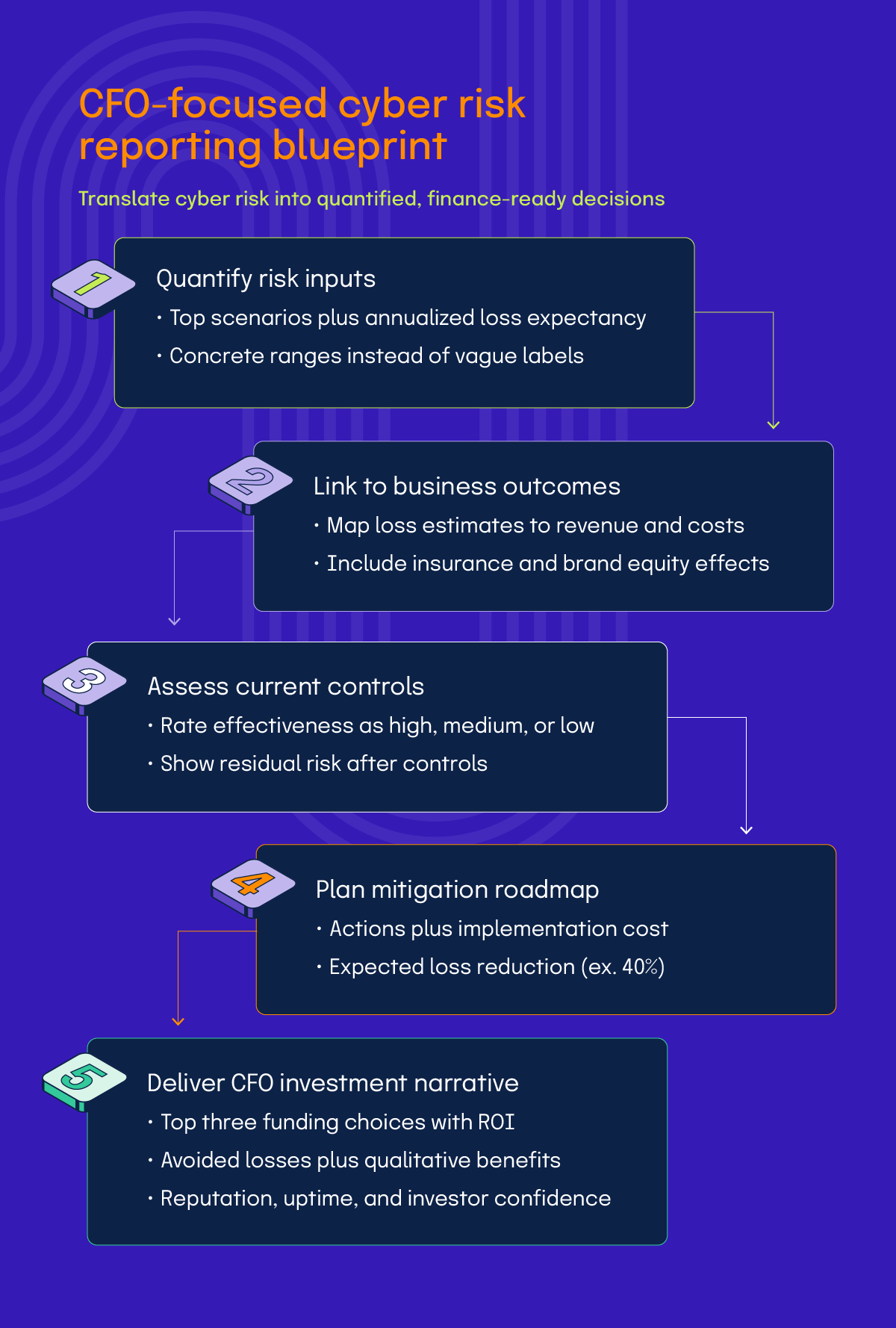
Use the following five-step blueprint to turn technical risk data into a CFO-ready story.
Which methods are used to quantify cyber risks?
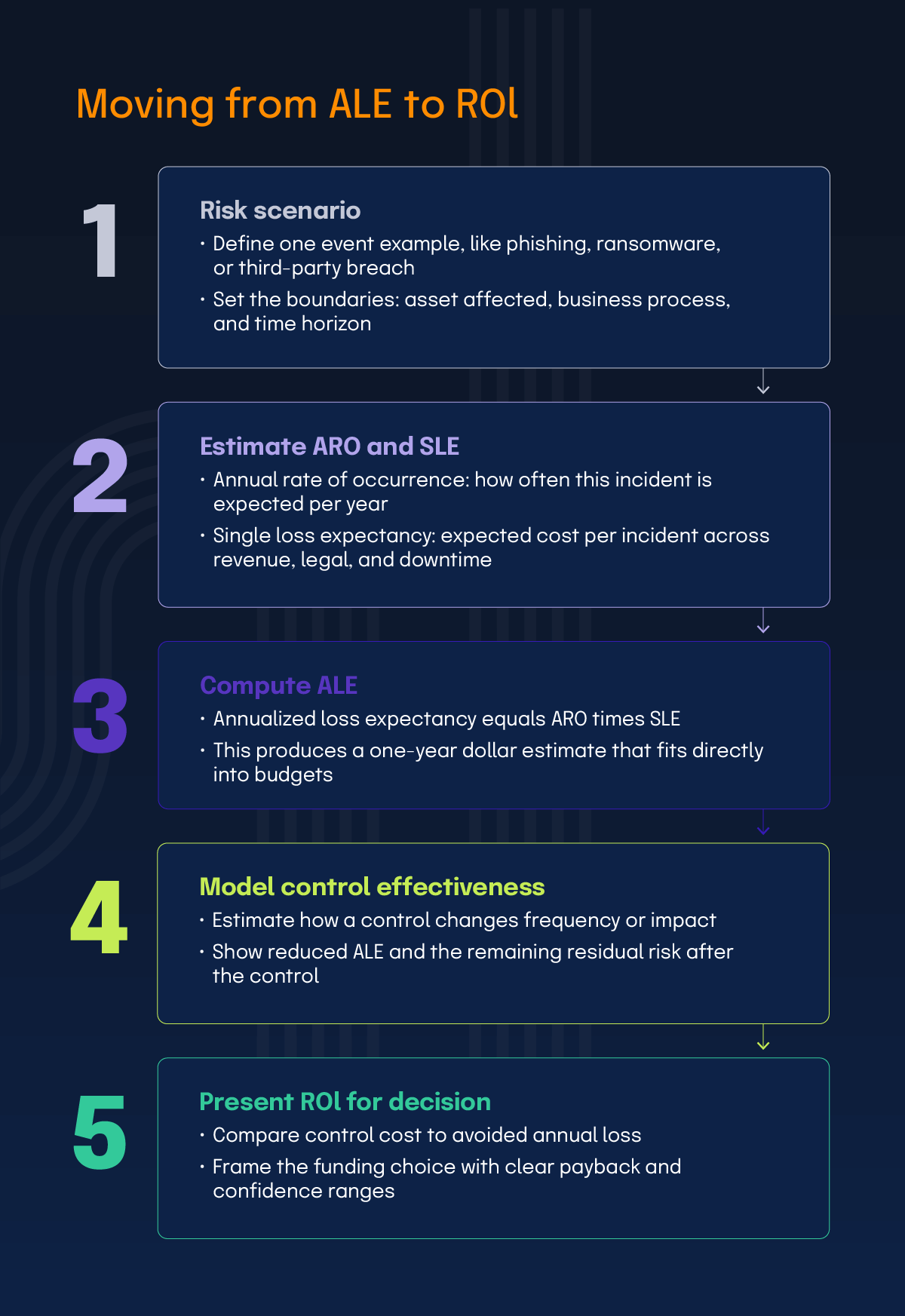
The most common way is by estimating expected annual loss, which translates risks into a dollar amount by calculating Annualized Loss Expectancy (ALE). ALE equals the Annual Rate of Occurrence (ARO) multiplied by the Single Loss Expectancy (SLE). In practice, teams often express ARO and SLE as ranges to reflect uncertainty and produce a defensible loss range. These calculations provide a solid basis for budgeting.
The FAIR model evaluates risk frequency and loss magnitude. Its core components are:
Loss Event Frequency (LEM): How often will this bad thing happen?
Loss Magnitude (LM): How much will it cost when it happens?
When presenting FAIR results to CFOs, focus on these common decision-ready outputs:
ALE: A risk management metric that calculates the expected financial loss from a specific risk over one year by multiplying the cost of a single incident by how often it’s expected to occur annually. For example, “based on our analysis, we expect to lose $2.3M annually from phishing attacks.”
Risk distribution analysis: The process of evaluating the likelihood and potential impact of various loss scenarios related to security threats. For example, “90% of the time, our annual losses from this risk will be under $5M. However, there’s a 10% chance we could see losses exceeding $15M. The worst-case scenario (1% probability) could reach $50M.”
Comparison data: Industry benchmarks like IBM’s 2025 Cost of a Data Breach Report estimate that the average breach cost is $4.44M overall, rising to $6.2M for firms with revenues between $500M and $1B. These figures help ground risk estimates in reality and support more informed budgeting decisions.
Control effectiveness monitoring: The process of estimating the effectiveness of controls on reducing risk impact or probability. For example, “implementing multi-factor authentication reduces our phishing ALE from $2.3M to $800K. The $200K annual cost of this control provides an 8:1 return on investment.”
Where reliable benchmark data exists, these outputs can be compared to industry peers and used to illustrate financial impact. For example, a statement like “industry peers in our sector average $1.8M-$4.1M in similar losses” helps CFOs to make quick decisions based on comparisons.
Probability-impact analysis scores each risk by its likelihood and the severity of its consequences. Organizations typically use a numeric scale for both dimensions, combine them into a risk score, and prioritize remediation efforts. This approach makes technical risk understandable to non-technical stakeholders and ensures mitigation resources target the most damaging scenarios. By linking quantitative outputs to compliance programs, companies can demonstrate risk posture to regulators and investors, reinforcing accountability and strategic planning.
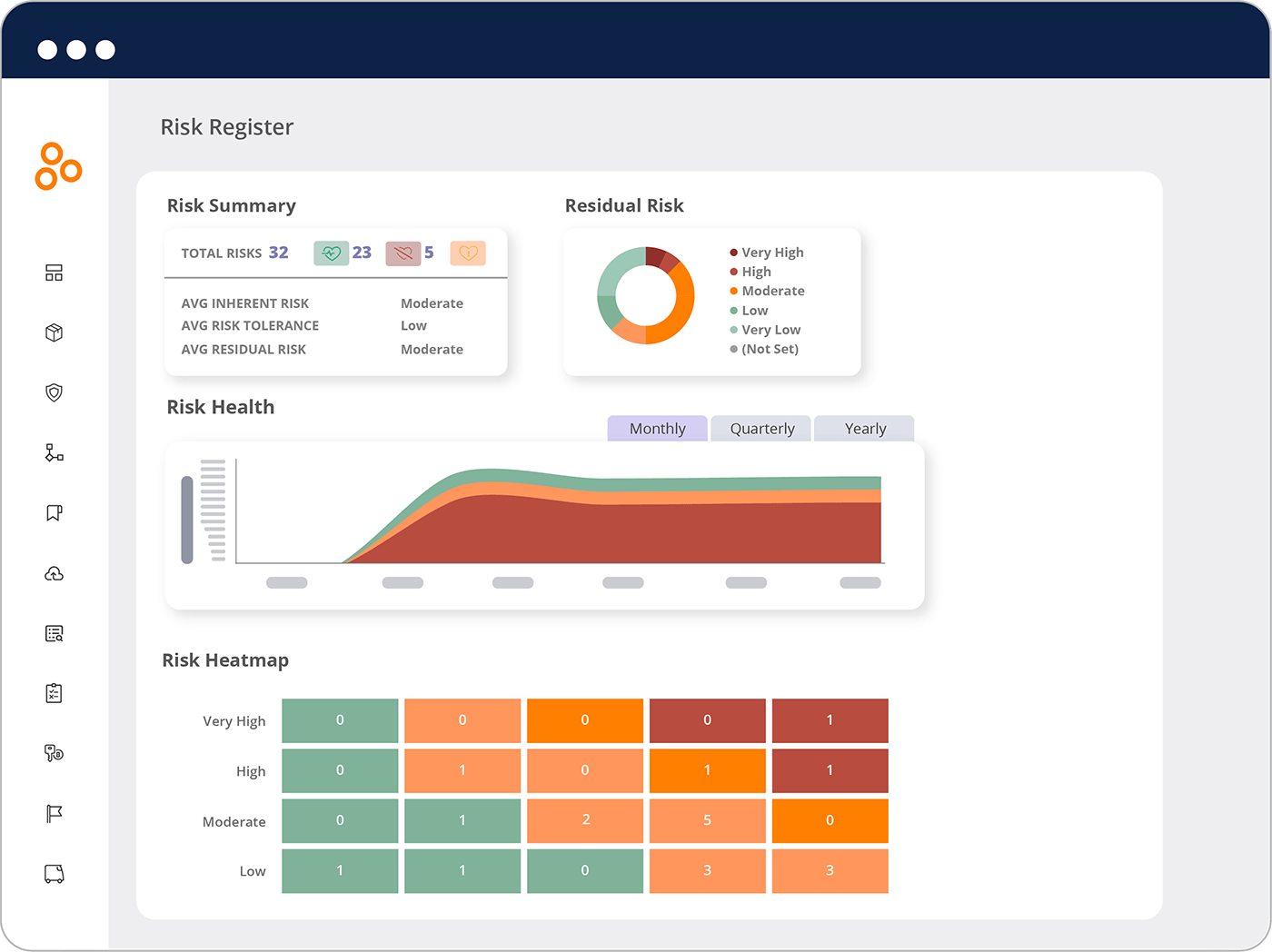
Hyperproof helps teams keep their risk analysis work organized by providing a clear place to record their risk assessments and link them to specific controls, owners, and evidence. Once a risk is documented, Hyperproof allows users to create remediation tasks, set due dates, and track progress in real-time, so everyone can see what has been fixed and what still needs attention. This organized approach helps ensure nothing falls through the cracks and provides stakeholders with clear visibility into how risks are being managed.
How are regulatory and compliance considerations incorporated into cyber risk reporting?
Regulatory and compliance considerations are a part of cyber risk reporting by defining material incidents, meeting legal disclosure timelines, and embedding cyber risks within the enterprise risk management (ERM) framework. Materiality determines whether a cyber event must be disclosed, typically when it could affect financial results, operations, or a reasonable investor’s decisions. Under the SEC’s 2023 disclosure rule, public companies must file a Form 8-K for material incidents within four business days of determining that the incident is material, supporting timely investor notification and reducing regulatory exposure.
Compliance reporting requires documenting the scope of the breach, response actions, and mitigation plans. Industry-specific mandates like HIPAA compel healthcare entities to notify affected individuals and regulators without unreasonable delay. Clear internal protocols help produce accurate and consistent disclosures, building a record of due diligence that can reduce legal exposure.
Integrating cyber risk into ERM creates a holistic view of all risks, linking digital vulnerabilities with financial, operational, and supply-chain risks. This alignment helps demonstrate to regulators that the organization maintains comprehensive oversight and allocates resources based on a unified risk hierarchy. Regular updates to ERM policies, informed by lessons learned from prior incidents, keep the organization compliant with evolving regulations and ready for audit scrutiny, while fostering a culture of risk awareness across the enterprise.
How can you improve your reporting of cyber risks to CFOs?
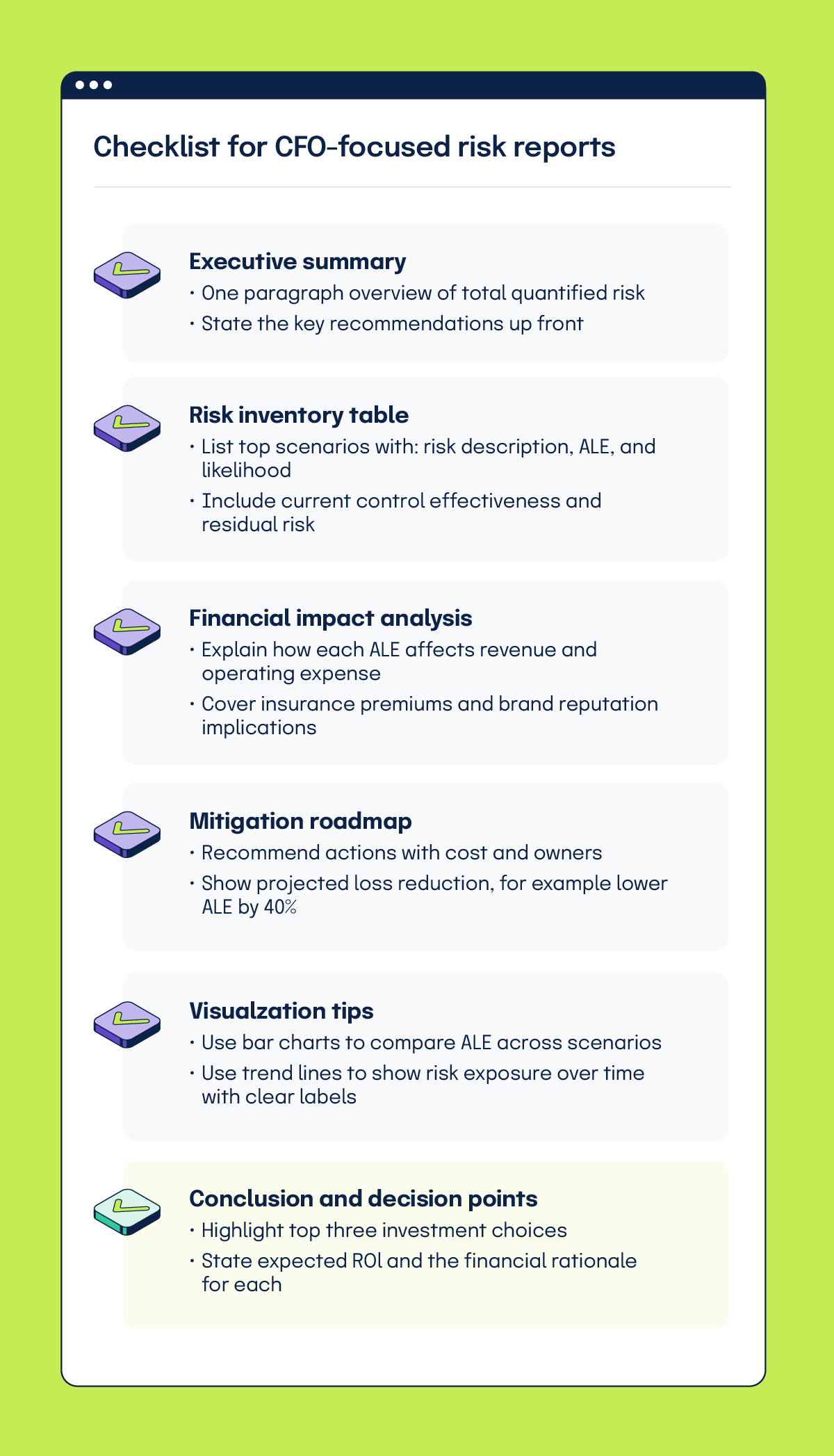
Improve your reporting by using quantitative data, tying risks directly to business outcomes, and demonstrating the return on investment of security measures. Replace vague qualitative terms like “high” risk with concrete estimates. Show an Annualized Loss Expectancy for each identified risk to give finance a solid basis for budgeting.CFOs prefer examples that include hard numbers, like how a data breach could affect revenue, or how a control that safeguards critical assets adds value. Highlight how compliance achievements can unlock contracts with risk-averse partners, turning security into a revenue-protecting function. For example, organizations that systematically document risk assessments and track remediation see a faster turnaround on security-related sales proposals.
Quantify the ROI of security projects by comparing costs with avoided losses. Demonstrate how a security upgrade can prevent a substantial breach, saving money and reducing downtime. Include intangible benefits like preserved brand reputation that supports investor confidence. Supplement quantitative results with qualitative evidence of effectiveness, which could include noted improvements after training initiatives, for example. Presenting these points as a clear financial narrative positions cybersecurity as an asset, rather than a cost center.
A strong CFO-focused risk report includes: a one-paragraph executive summary, top quantified scenarios with ranges, mapped business impacts, current vs. residual risk after controls, and a mitigation roadmap with cost and expected reduction.
How does quantified risk reporting build trust with stakeholders?
Quantified reporting builds trust with stakeholders by delivering concrete numbers that translate cyber risk into clear financial impact, showing how risks could affect the organization’s bottom line. When investors, customers, board members, and analysts see projected losses or potential revenue impacts, they gain a clear picture of risk and confidence that leadership is accountable.
Stakeholders expect transparent data that meets regulatory demands, like the SEC’s disclosure rules. Providing detailed figures and mitigation plans demonstrates accountability and satisfies compliance requirements. Regular updates reinforce that their interests are protected, which helps maintain confidence.
Boards and analysts need the same data framed in business terms. Translating technical risks into financial outcomes helps them assess strategic implications and allocate resources. Simple visual aids, like annualized loss trend charts, highlight urgency without overwhelming the audience.
Actionable recommendations turn numbers into next steps. Suggesting a targeted security upgrade after identifying a high-probability risk, or allocating funds for training to avoid an estimated loss, shows a clear cost-benefit analysis. Outlining timelines and responsible teams makes the guidance practical and reinforces that the analysis drives real risk reduction. By consistently linking risk data to business outcomes, organizations create a reliable narrative that stakeholders can trust for informed decision-making.
Key takeaways
With Hyperproof, teams can centralize risk assessments, link them to controls and evidence, and give finance leaders a consistent, decision-ready view of cyber risk.
See Hyperproof in Action
Related Resources
Ready to see
Hyperproof in action?











