How to Perform an Effective IT Risk Assessment
Cyber attacks are attempted every 40 seconds and ransomware attacks increase at a rate of 400% year over year, so it’s no wonder your organization has to take security seriously. But do you feel confident that you’ve allocated an appropriate amount of resources towards your security program?
Do you know which information assets and systems are most vulnerable? And have you calculated the potential financial costs you’d incur if key systems were to go down? In our modern, highly volatile risk environment, these are critical questions for every organization to answer. Getting the answers will require your organization to become proficient in conducting an IT risk assessment – sometimes called an information security risk assessment or InfoSec risk assessment.
For many teams, this is the first step toward building a repeatable IT security risk management practice and a structured cyber risk analysis that ties technical InfoSec risk to concrete business decisions. As programs mature, enterprise security risk management software helps teams connect those IT findings to enterprise-level risk ownership, reporting, and consistent treatment decisions across departments. This approach also supports consistent cyber security risk analysis inputs and more reliable cyber security risk analytics as your program matures.
What is an IT risk assessment?

IT security risk assessments focus on identifying the threats facing your information systems, networks, and data and assessing the potential consequences you’d face should these adverse events occur.
Put simply, what is security risk in this context? It’s the combination of:
- the value and sensitivity of your information assets,
- the likelihood that a threat will exploit a weakness, and
- the impact on your business if that happens.
A what is information security risk assessment explanation usually boils down to this: you systematically identify those threats, vulnerabilities, and potential impacts, then decide which risks you’ll mitigate, accept, transfer, or avoid. In other words, cyber security and security risk analysis is the discipline of connecting threats and vulnerabilities to likelihood, impact, and business decisions — not just listing problems.
To protect your organization, conduct risk assessments on a regular basis (e.g., annually), and whenever major changes occur within your organization, like when:
- There is an acquisition, merger, or re-organization
- A leader decides to implement new technology to handle a key business process
- Employees suddenly move from working in an office to working remotely
Not only is IT risk assessment important for protecting your organization and right-sizing your security investment, but it may also be mandatory. Some information security frameworks, like ISO 27001 and CMMC, require risk assessments to be conducted in specific ways and documented on paper in order for your organization to be considered “compliant.”
In regulated industries, legislation introduced the concept of security risk analysis explicitly into law. For example, healthcare privacy and security regulations and various data protection laws around the world now require organizations to perform formal information security risk assessments on a recurring basis and maintain an auditable trail of those activities. For many teams, this is where cyber risk assessments become repeatable: you standardize your cybersecurity risk assessment process so the same inputs produce comparable results over time. Done well, it turns assessing IT risks and how they are managed into something you can explain to leadership without drowning them in technical detail.
IT risk assessments (or IT cybersecurity risk assessments) are a crucial part of any successful security program. Risk assessments allow you to see how your organization’s risks and vulnerabilities are changing over time, so decision-makers can put appropriate measures and safeguards in place to respond to risks appropriately. Learn more in the 2024 IT Risk and Compliance Benchmark Report.
Is your compliance program effective for the current regulatory landscape? Find out what are the key elements you need with our free guide.
Why conduct an IT risk assessment?

For some businesses, especially small companies, it might seem like a big enough job just to put a team in place to develop and manage information security plans without the added work of proactively looking for flaws in your security system. But in reality, an IT risk assessment is something you can’t afford to skip over. Information security risk assessments serve many purposes, some of which include:
Cost justification
An IT risk assessment gives you a concrete list of vulnerabilities you can take to upper-level management and leadership to illustrate the need for additional resources and a budget to shore up your information security processes and tools.
It can be difficult for leadership to see why you need to invest more money into information security practices that, from their point of view, are working just fine. Showing them the results of an information security risk assessment is a way to drive home that the risks to your sensitive information are always changing and evolving, so your infosec practices need to evolve with them.
Productivity
If you are consistently performing risk assessments, you will always know where your information security team should dedicate their time, and you will be able to use that time more effectively. Instead of always reacting to a problem after it has caused a security event, you’ll spend that time fixing vulnerabilities in your security practices and processes so you can avoid the issue in the first place. IT risk assessments also show you which risks require more time and attention, and which risks you can afford to divert fewer resources to.
Breaking barriers
Information security should ideally involve two groups: senior management and IT staff. Senior management should dictate the appropriate level of security, while IT should implement the plan to help achieve that level of security. Risk assessments bring these two groups together. They give IT staff a tool to open up conversations with management about infosec risks the organization faces and how the company can achieve the highest level of security possible.
Communication
Above all else, risk assessments improve information security by facilitating communication and collaboration throughout an organization.
First, to properly assess risk within a business, the IT security staff will need to have conversations with all departments to understand,
- The operations of each department
- How employees are using different systems
- How information flows between different systems
This gives the security team a chance to learn about other peoples’ positions, challenges, and contributions to the information security of the business as a whole.
Second, risk assessments provide IT and compliance teams a chance to communicate the importance of information security to people throughout the entire organization and to help each employee understand how they can contribute to security and compliance objectives.
Changes in many different parts of a business can open it up to different risks, so it’s important for the people responsible for information security to understand if and when the business’s processes or objectives change.
As we said earlier, the more people and information sources you can include, the better the output will be. But it’s important to know that any company can perform an information security risk assessment and find areas for improvement, even if you don’t have extensive IT or compliance teams.

How is an IT risk assessment done?

You can perform two broad categories of IT cybersecurity risk assessments or IT security reviews, but the most effective approach is to incorporate aspects of both of them.
- Quantitative risk assessments, or assessments that focus on numbers and percentages, can help you determine the financial impacts of each risk.
- Qualitative risk assessments help you assess the human and productivity aspects of a risk.
Together, these approaches form a practical cybersecurity risk analysis that standardizes your cyber attack risk assessment and cyber threat risk assessment scenarios, strengthens data security risk management, supports employee risk assessment cybersecurity reviews, and improves cyber security risk analysis consistency and cyber security risk analytics reporting across teams.
Both of these categories have value, and both of them will allow you to communicate risk with different types of people. For example, your legal and financial teams will likely be most interested in the numbers, while your operations teams, such as sales and customer service, will be more concerned about how a security event would affect their operations and efficiency.
Following these steps will help you conduct a basic information security risk assessment and give you the tools you need to begin building a consistent process for identifying key business risks. Below are the core cybersecurity risk assessment steps most teams follow, even when frameworks and tooling differ.
1. Identify and catalog your information assets
The first step in a risk assessment is to make sure that you have a comprehensive list of your informational assets. It’s important to remember that different roles and different departments will have different perspectives on what the most important assets are, so you should get input from more than one source here. The most important information asset for salespeople might be your company’s CRM. At the same time, IT likely sees the servers they maintain as a higher priority, while HR’s most important information asset is confidential employee information.
Once you have identified all of your information assets and key stakeholders within all departments, you’ll need to classify these data assets based on their sensitivity level as well as the strategic importance of the asset to the organization. To get accurate and complete information, you’ll need to talk to the administrators of all major systems across all departments.
Below is a sample data classification framework. For more information on how to classify data, please refer to this article from Sirius Edge.

Once you have your data classified, you can zero in on the most sensitive data and see how it is being handled.
2. Identify threats
Effective cyber risk identification starts with understanding the full range of threats to data security. Hackers are usually top of mind, but threats to your business’s information security come in many different forms. A cyber security threat assessment should cover external attackers, insider risks, third parties, misconfiguration, and operational failure — not just “hackers. A solid cyber security threat and risk assessment starts by naming your realistic threat sources (external attackers, insiders, vendors, misconfiguration, and outages) before you worry about scoring. You can see from this list of this list of 2019 data breaches that while hackers exploiting weaknesses in a business’ firewalls or website security programs has been very common, a lot of different threat types contributed to data breaches in 2019. You need to take into account many different threat types when compiling a list of all the unique threats your business faces.
For example, you also have to take into account not just malicious human interference, but also accidental human interference, such as employees accidentally deleting information or clicking on a malware link. Depending on the quality of your hardware and your information systems, you might also need to account for the risk of system failure.
Finally, things such as natural disasters and power failures can wreak as much havoc as humans can, so you need to account for any of those kinds of threats as well. After you’ve completed this step, you should have a thorough list of the threats to your assets.
New risks prompted by COVID-19
Now that the novel coronavirus has forced most organizations into a remote-only operating model, organizations are left more vulnerable. Employees are working outside of corporate firewalls. Malicious cybercriminals could take advantage of public concern surrounding the novel coronavirus by conducting phishing attacks and disinformation campaigns.
Phishing attacks often use a combination of email and bogus websites to trick victims into revealing sensitive information. Disinformation campaigns can spread discord, manipulate public conversation, influence policy development, or disrupt markets.
During this time, your IT security team should remind employees to take precautions, reiterate key concepts covered in your security training, ensure that all monitoring systems are operating correctly, and be ready to respond to any security incidents promptly.
3. Identify vulnerabilities
A vulnerability is a weakness in your system or processes that might lead to a breach of information security. For example, if your company stores customers’ credit card data but isn’t encrypting it or testing that encryption process to ensure it’s working properly, that’s a significant vulnerability. Allowing weak passwords, failing to install the most recent security patches on software, and failing to restrict user access to sensitive information are behaviors that will leave your business’s sensitive information vulnerable to attack.
Another vulnerability you may face during the coronavirus health crisis is the lack of staff. Security controls are at risk of not being performed as IT security staff are working remotely or worse, sick themselves.
You can find vulnerabilities through audits, penetration testing, security analyses, automated vulnerability scanning tools, or the NIST vulnerability database.
It’s also important to consider potential physical vulnerabilities. For example, suppose your employees work with hard copies of sensitive information or use company electronics outside of the office. In that case, this can lead to the misuse of information, just like vulnerabilities in your software and electronic systems.
4. Analyze internal controls
After identifying the vulnerabilities in your systems and processes, the next step is to implement controls to minimize or eliminate the vulnerabilities and threats. This could be either control to eliminate the vulnerability itself or control to address threats that can’t be totally eliminated.
Controls can be technical, such as computer software, encryption, or tools for detecting hackers or other intrusions, or non-technical, such as security policies or physical controls. Controls can also be broken down into preventive or detective controls, meaning that they either prevent incidents or detect when an incident is occurring and alert you.
Creating effective controls requires experience and skills. Suppose your firm does not have security and compliance subject matter experts on staff. In that case, it is crucial to seek out assistance from professional services firms that have deep expertise in addressing IT security issues.
5. Determine the likelihood that an incident will occur
Using all the information you have gathered – your assets, the threats those assets face, and the controls you have in place to address those threats – you can now categorize how likely each of the vulnerabilities you found might actually be exploited. Many organizations use the categories of high, medium, and low to indicate how likely a risk is to occur.
So, if, for example, a core application you use to run your business is out-of-date and there’s no process for regularly checking for updates and installing them, the likelihood of an incident involving that system would probably be considered high.
On the other hand, if you handle a large volume of personal health information, have automated systems for encrypting and anonymizing it, and regularly test and check the effectiveness of those systems, the likelihood of an incident could be considered low. You will need to use your knowledge of the vulnerabilities and the implementation of the controls within your organization to make this determination.
6. Assess the impact a threat would have
This step is known as impact analysis, and it should be completed for each vulnerability and threat you have identified, no matter the likelihood of one happening. Your impact analysis should include three things:
- The mission of the system, including the processes implemented by the system
- The criticality of the system is determined by its value and the value of the data to the organization
- The sensitivity of the system and its data
If possible, you should consider both the quantitative and qualitative impacts of an incident to get the full picture. Depending on the three factors above, you can determine whether a threat would have a high, medium, or low impact on your organization. Taken together with how likely an incident is to occur, this impact analysis will help you to prioritize these risks in the next step.
7. Prioritize the risks to your information security
Prioritizing your security risks will help you determine which ones warrant immediate action, where you should invest your time and resources, and which risks you can address at a later time.
For this step, it might help to utilize a simple risk matrix that helps you use the information you already have about each vulnerability/threat pair you’ve identified and plot it on the matrix. Risks that are both likely to happen and would have severe consequences would be mapped as a high priority, while risks that are unlikely to happen and would have marginal consequences would be mapped as the lowest priority, with everything else falling somewhere in between.
You can make your risk matrix as simple or as complex as is helpful to you. If you’re a large organization with a lot of risks competing with each other for time and attention, a more in-depth 5×5 risk matrix will likely be helpful; smaller organizations with fewer risks to prioritize can probably utilize a simple 3×3 matrix and still get the same benefit.
Risk models for information security
At this time, there are several different frameworks for risk quantification. Here are a few popular frameworks to date for risk quantification:
FAIR Model: The FAIR (Factor Analysis of Information Risk) cyber risk framework is touted as the premier “Value at Risk (VaR) framework for cybersecurity and operational risk”. The FAIR quantitative risk analysis model defines risk management as “the combination of personnel, policies, processes, and technologies that enable an organization to achieve and maintain an acceptable level of loss exposure cost-effectively.” You can learn more about how to implement the FAIR model by reading The FAIR book.
NIST SP 800-30: Originally published in 2002 and updated in 2012, NIST Special Publication 800-30 or NIST Risk Management Framework is built alongside the gold-standard NIST CSF as a means to view an organization’s security threats through a risk-based lens.
World Economic Forum Cyber Risk Framework and Maturity Model: This model was published in 2015 in collaboration with Deloitte, and bears some similarities to the NIST RMF in that it relies on subjective judgments. The model looks at risk through a lens known as “value-at-risk” and asks the stakeholders to evaluate three components: 1) existing vulnerabilities and defense maturity of an organization, 2) value of the assets, and 3) profile of an attacker.
8. Design controls
Once you’ve established priorities for all risks you’ve found and detailed, then you can begin to make a plan for mitigating the most pressing risks. To determine what controls you need to develop to mitigate or eliminate the risks effectively, you should involve the people who will be responsible for executing those controls.
Senior management and IT should also be heavily involved to ensure that the controls will address risks and align with your organization’s overall risk treatment plan and end goals. You’ll also need to develop a plan to implement all new controls. You may also need to consult with professional services firms with IT and security expertise to develop a new set of controls. In this plan, be sure to include the resources you would need to train pertinent employees.
For further guidance on how to design effective controls to mitigate risks, check out this article The Four Signs of an Effective Compliance Program
9. Document the results
The final step in your risk assessment is to develop a report that documents all of the results of your assessment in a way that easily supports the recommended budget and policy changes. Many teams use that report to compare their approach with what cyber security risk assessment companies recommend for repeatable risk ownership, control mapping, and evidence tracking. These cyber risk assessment reports become the basis for budget conversations, audit evidence, and tracking remediation progress quarter over quarter.
Risk assessment reports can be highly detailed and complex, or they can contain a simple outline of the risks and recommended controls. Ultimately, what your report looks like depends on who your audience is, how deep their understanding of information security is, and what you think will be the most helpful in showing potential risks. A risk assessment aims to document your organizational risks and create a plan to address those risks to avoid encountering a risk without preparation.
Many organizations formalize this into an information security assessment report that can be shared with executives, auditors, and regulators. A typical information security assessment report will:
- Summarize your scope and methodology
- Describe the key information assets and systems reviewed
- Outline the main threats, vulnerabilities, and assessed risk levels
- Highlight high-priority risks with recommended treatments and timelines
- Provide an appendix or risk register for detailed, technical findings
- Include one cyber security risk assessment example: Example scenario: “Ransomware encrypts the finance file server (Likelihood: Medium / Impact: High). Controls: immutable backups + MFA on admin accounts + EDR on servers. Timeline: backups in 14 days, MFA in 30 days, EDR tuning in 45 days. Owner: IT Security Manager.”
Whether you call it an IT risk assessment report or an information security assessment report, the goal is the same: give decision-makers a clear, concise picture of your InfoSec risk landscape and how you plan to address it.
Creating this report for senior management is the final step in this process and is crucial for communicating what they need to understand about information security risks. If you’re ready to go beyond the basics, you can follow a structured cybersecurity risk assessment that connects your IT risks to concrete mitigation plans and executive-ready reporting.
IT risk assessment template
To make it easier for you to document the results of your risk assessment, we’ve created an IT risk assessment template. You can reuse the same template when you perform an IT security review or follow-up IT cybersecurity risk assessments later in the year, so your findings stay consistent and comparable over time.
Use the template to produce a consistent cyber risk assessment report format each cycle, so trends and improvements are obvious even to non-technical stakeholders.
IT risk assessments don’t need to be complicated

Teams that invest in automated scheduling tools compliance risk reduction can ensure recurring risk reviews, control testing, and evidence updates happen on time without relying on manual reminders.
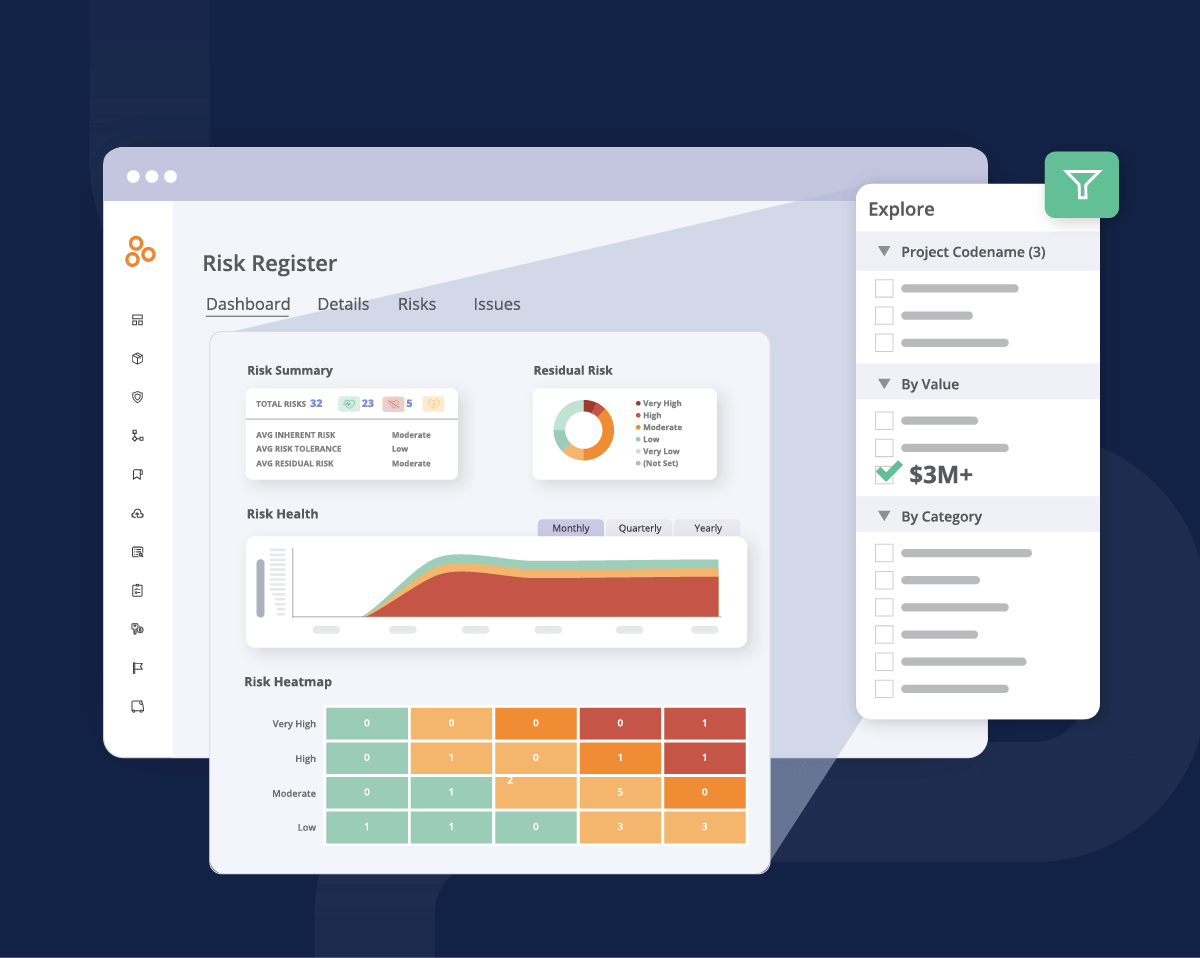
Purpose-built risk register software makes it easy for risk owners to document everything that should go into a risk register, make updates to risks on the fly, visualize changes to risks, and communicate risk information to leadership teams.
Hyperproof offers a secure, intuitive risk register for everyone in your organization. As a modern compliance risk platform, Hyperproof brings risks, controls, and evidence into one shared workspace so teams can see exposure, ownership, and remediation progress at a glance. With the application, risk owners from all functions and business units can document their risks and risk treatment plans. You can link risk to control and gauge how much a specific risk has been mitigated by an existing control versus the residual risk that remains. With this clarity, your risk management, security assurance, and compliance teams can focus their energy on the risks you truly need to worry about.
With Hyperproof’s dashboard, you can see how your risks change over time, identify which risks and controls to pay attention to at a given moment, and effectively communicate the potential exposure for achieving strategic operations, reporting, and compliance objectives to your executives.
If you can successfully bring together the parties necessary for a thorough risk assessment and account for all of the risks to your data, you’ll be taking a huge step toward earning your customers’ trust and protecting the sensitive data you’re entrusted with.
IT risk assessment & InfoSec risk: quick FAQs
What is information security risk assessment?
An information security risk assessment (also called an IT risk assessment or InfoSec risk assessment) is a structured process where you identify your critical information assets, the threats and vulnerabilities that could affect them, and the potential impact on your business. You then prioritize those risks and decide which controls or treatments to implement.
What is security risk in IT?
In IT, security risk is the potential for loss or damage when a threat exploits a vulnerability in your systems, processes, or people. It’s usually expressed as a combination of likelihood (how probable an event is) and impact (how bad it would be if it happened).
How often should we do IT cybersecurity risk assessments or an IT security review?
Best practice is to perform a formal IT cybersecurity risk assessment at least annually and whenever you make major changes (new systems, mergers, new data flows, big regulatory changes). Lighter-weight IT security reviews can happen more frequently – quarterly or even monthly – for high-risk areas.
Do we always need a formal information security assessment report?
Not every small assessment needs a 50-page document, but for annual or framework-driven assessments (ISO 27001, SOC 2®, etc.), an information security assessment report or risk register is essential. It becomes your evidence for auditors and your single source of truth for tracking InfoSec risk over time.
Safeguard your organization’s sensitive data and earn your customers’ trust with Hyperproof. Request a demo today and discover the power of their dashboard. Track risk changes over time, prioritize key risks, and effectively communicate potential exposure to executives. Don’t miss this opportunity to enhance your strategic, operational, reporting, and compliance objectives.
See Hyperproof in Action
Related Resources
Ready to see
Hyperproof in action?