Getting Started with IT Risk Management Frameworks: from NIST RMF to FAIR
When developing an IT risk management program, it can be hard to know where to start. So what is IT risk management exactly? At its core, IT risk management is the ongoing process of identifying, assessing, prioritizing, and treating risks that could affect your technology, data, and digital services. It connects cybersecurity and operational risk to business outcomes, helping leaders decide which risks to accept, mitigate, transfer, or avoid. In other words, a risk management framework can act as your compliance risk framework, giving you a consistent way to document decisions, map controls, and prove due diligence to auditors. There are a lot of questions you might ask yourself, like:
- Which risk management frameworks should you use?
- Are you a single practitioner or do you have a team?
- Do you want a qualitative or quantitative framework?
How you answer each of these questions is important, as it will help you select a framework that is right for your organization’s current needs.
So, where do you get started? This article outlines how different risk management frameworks work, what types of teams they’re made for, and other key differentiators between them.
What is a risk management framework (RMF)?

No organization can eliminate risk, but it can be effectively and efficiently managed and prioritized. A risk management framework provides organizations with guidelines for effectively defining, mitigating, and managing risks to maintain business resiliency and avoid reputational and financial losses. In practice, this is what IT risk management looks like: you choose a framework, use it to structure how you identify and rate technology-related risks, and then decide which controls, tools, and processes you’ll use to keep those risks within your tolerance.
Common types of enterprise risk include:
- Financial risk
- Operational risk
- Strategic risk
- Compliance risk
- Economic risk
- Legal risk
- Natural disasters
- Security risk
It’s also important to define an information security policy as part of your process for choosing a risk management framework. Often, you’ll find that specific frameworks are named within risk management policies as well as standard risk procedures which offer an explanation of how risk management committees work, how the framework works, and the duration at which risks are evaluated. Having specific IT risk management frameworks named within your policy will also keep your legal team happy. Related: Cybersecurity Best Practices
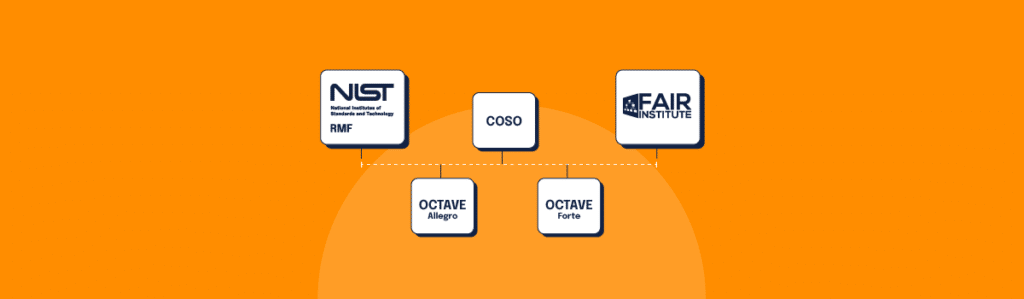
The 5 most common IT risk management frameworks
Each of these frameworks answers the same fundamental question – what is IT risk management for our organization, and how will we do it consistently? The right choice depends on your size, resources, and whether you prefer a qualitative or quantitative approach.
1. NIST Risk Management Framework (RMF)

Best for: Large organizations with dedicated risk management teams
Developed by the National Institute of Standards and Technology, NIST RMF is the IT risk management framework that gets the most traction. With its well-defined steps and process, it’s a good fit for big organizations — especially those with a risk management team or committee — as it does require dedicated resources to implement and manage.
Qualitative in nature, NIST RMF is also very specific to cybersecurity — particularly cybersecurity risk. It also aligns well with another NIST framework, NIST SP 800-53, which is a framework for those working with the federal government. Related: Guide to NIST 800-53
The NIST RMF framework provides seven steps to get started:
- Prepare: Essential activities to prepare the organization to manage security and privacy risks
- Categorize: Categorize the system and information processed, stored, and transmitted based on an impact analysis
- Select: Select the set of NIST SP 800-53 controls to protect the system based on risk assessment(s)
- Implement: Implement the controls and document how controls are deployed
- Assess: Assess to determine if the controls are in place, operating as intended, and producing the desired results
- Authorize: Senior official makes a risk-based decision to authorize the system (to operate)
- Monitor: Continuously monitor control implementation and risks to the system
2. OCTAVE Allegro

Best for: Smaller organizations with a single practitioner who is new to risk management
First released in September 1999 by the Software Engineering Institute at Carnegie Mellon University, OCTAVE Allegro is another commonly used IT risk management framework. OCTAVE stands for Operationally Critical Threat, Asset, and Vulnerability Evaluation.
It offers a very lightweight risk management process, and OCTAVE Allegro is a great risk management framework if your organization has a single practitioner who is new to risk management. Unfortunately, OCTAVE Allegro doesn’t scale for a team-oriented approach so it won’t be a great fit for organizations with entire risk management teams or committees.
If you can fill out a series of ten forms and circulate them for peer review, then OCTAVE Allegro may be a great fit for your IT risk management program. It also has examples, including threat trees, which walk you through different hypothetical situations to understand risk.
Smaller organizations (or organizations with a single practitioner assigned to do risk management) would find OCTAVE Allegro to be a great fit, especially if they want to get their program up and running in just one day. One downside is that it only looks at one point in time, and the framework doesn’t address ongoing governance.
3. OCTAVE FORTE

Best for: Organizations with a risk management team or committee looking for continuous governance of risk
OCTAVE FORTE, or Operationally Critical Threat, Asset, and Vulnerability Evaluation for the Enterprise, is a cybersecurity-aligned IT risk management framework. It’s scalable and often overseen by a large team or risk management committee. On this list, it’s the first enterprise risk management framework we’ve included, and it’s also qualitative in nature. Whereas OCTAVE Allegro is a good fit for a single practitioner, Octave FORTE is a better fit for a team or committee.
What is more unique to OCTAVE FORTE is that its documentation encourages continuous process, addressing continuous governance of risk. Other frameworks may simply outline the process once, giving the impression that once you’ve set up your controls, you’re done. But, the continuous nature of OCTAVE FORTE should be observed with other frameworks as well, as risks change and adapt over time — especially as threat actors grow more and more intelligent.
OCTAVE FORTE addresses business risks and cybersecurity risks, and it’s good if you want to have a risk management committee. It’s a broader framework than OCTAVE Allegro because it gets into enterprise risk management, not just cybersecurity risk management. It allows businesses to better align and understand overall risk, helping risk practitioners eliminate siloed risk management frameworks. This allows the executives to not have competing frameworks so they can better understand the broader risk landscape.
The 10-step OCTAVE FORTE process
Consisting of a 10-step process, FORTE is somewhat inspired by other standards created by the Committee of Sponsoring Organizations (COSO), the International Standards Organization (ISO), and the National Institute of Standards and Technology (NIST).
These 10 steps help an organization achieve the following:
- Understand its assets, capabilities, and risks
- Form risk appetite statement(s) to document risk tolerance
- Create response plans to manage risks
- Form processes to monitor whether risk is being managed effectively
- Develop a plan to improve the organization’s ERM program
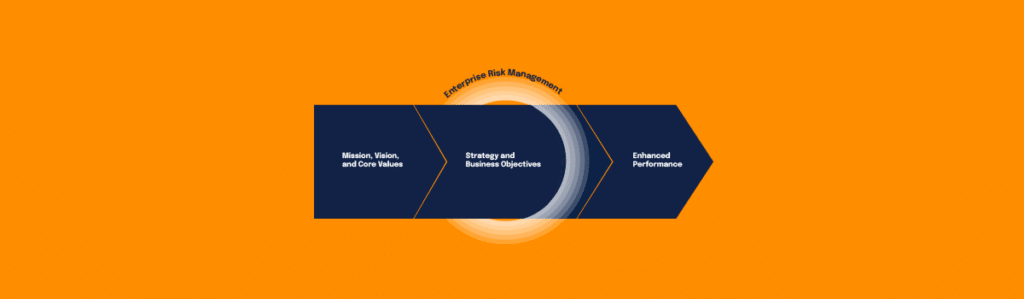
4. COSO enterprise risk management
Best for: Organizations with a team of practitioners or a risk committee
COSO debuted in 1992, but the enterprise risk management framework came out in 2004. Many teams use COSO as a business risk management framework because it ties risk directly to strategy, performance, and governance — not just IT controls. If you’re comparing IT-focused frameworks to broader enterprise approaches, a corporate risk management framework can help you connect technology risk to organization-wide objectives, reporting, and governance. COSO has been endorsed by the Federal Reserve and the Federal Deposit Insurance Corporation, and is one of the most common Enterprise Risk Management frameworks cited by publicly traded companies as the 2004 standard addresses Section 404 of Sarbanes Oxley (SOX). In terms of complexity, it’s comparable to NIST RMF, and it’s necessary to have a team of practitioners or a risk committee to manage the framework.
COSO specifically defines ERM as “the culture, capabilities, and practices, integrated with strategy-setting and its performance, that organizations rely on to manage risk in creating, preserving, and realizing value.” The 2017 ERM provides guidance on what to do to incorporate risk assessment, objective setting, corporate governance, risk tolerance, risk appetite, and risk response into business strategies.
This helps organizations proactively respond to institutional investors who want to focus on strategic long-term value creation. Unfortunately, COSO does not succinctly help internal auditors know how to link risk assessments to value creation or preservation and does not provide prescriptive guidance on how to measure risks.
5. FAIR risk management

Best for: Organizations looking to take a quantitative approach to risk management
The only quantitative IT risk management framework included in this list is the FAIR Risk Management framework. FAIR, or Factors Analysis of Information Risk Management, allows practitioners to define risk in terms of monetary cost.
FAIR can get complicated with its definitions; it requires a cost for everything, from productivity to telecommunications, staff salaries, and more. However, the nice part about FAIR is that risks can be defined by their values. Controls also have costs, so it becomes easier to understand the monetary impact of a control for a certain risk.
There are experienced practitioners who work with FAIR and understand how to price out the costs of everything within an organization. The benefits of quantitative risk management are that you’re able to provide the board with actual numbers and costs, which allows for better decisions on how to manage risks on their part.
However, FAIR is quite complicated to implement and often doesn’t work for organizations unless they can invest enough resources.
Fret less with risk management frameworks
Using a risk framework helps you stand up your risk management program, but it also helps you make sure to cover all of your bases. When you’re starting out, getting to know the cybersecurity and compliance landscape can be confusing. But with frameworks, you’re able to put structure in place and have a place to start without building everything from scratch.
Not only does using an IT risk management framework help you start your program, but it also gives you peace of mind knowing you’re adhering to standards set by someone outside your organization. Non-partial third parties developed these frameworks based on years of IT risk management expertise so you can know where to start.
Hyperproof helps compliance professionals adhere to 60+ different frameworks, including ISO 27001, NIST, CMMC, FedRAMP, and many more. The platform also makes it easy to collaborate across teams and help you automate time-consuming repetitive tasks.
If you’re ready to take the next step and implement an IT risk management framework, Hyperproof can help. Hyperproof helps compliance professionals adhere to 60+ different frameworks, including ISO 27001, NIST, CMMC, FedRAMP, and many more. With Hyperproof, you can streamline collaboration across teams, automate repetitive tasks, and ensure adherence to the relevant standards.
Getting started with IT risk management can be overwhelming, but don’t let it stop you from taking the next step. Choose a framework, leverage the right tools, and ensure the security and resilience of your organization.
At the end of the day, IT risk management is about using a structured framework to keep technology-related risks at an acceptable level while your business grows. Whether you start with NIST RMF, OCTAVE, COSO, or FAIR, the goal is the same: make clearer, more defensible decisions about which risks you’re taking on and how you’ll control them over time.
Learn more about how a global IT services company is using Hyperproof to get time back and improve its risk management maturity.
See Hyperproof in Action
Related Resources
Ready to see
Hyperproof in action?