The U.S. Government Is Moving to Zero Trust Cybersecurity. So Should You.
Earlier this year, the Biden Administration announced ambitious plans to improve cybersecurity across the federal government — and, by extension, those government contractors providing IT services. Now we’re starting to see more specific proposals for that cybersecurity vision, and IT service providers should start rolling up their sleeves.
Those proposals were unveiled in early September when the Administration circulated a draft strategy memo for public comment. In that memo are five cybersecurity goals that the Administration wants to achieve within three years, with specific recommendations for identity management, data encryption, IT asset management, and more.
The exact details of those goals might be fine-tuned in the coming months, but government contractors, and especially cloud-based Software as a Service (SaaS) providers, should have no illusions here. The federal government will overhaul how it manages cybersecurity, and IT providers will need to integrate those big objectives into their plans and routine operations — sooner rather than later.
So let’s review what those objectives are and how IT providers in the private sector can anticipate what’s to come.

What the administration wants to do
The Administration’s proposed strategy lists five goals it wants federal agencies to achieve by Oct. 1, 2024:
- Identity management. An agency’s employees should use Single Sign-On (SSO) to access the applications they use at work, with multi-factor authentication to reduce the risk of phishing attacks.
- Devices. The entire federal government should have a complete inventory of every device it operates and authorizes for government use, and can detect and respond to incidents on those devices.
- Networks. Agencies should encrypt all DNS requests and HTTP traffic within their environment and begin segmenting networks around their applications.
- Applications. Agencies should treat all applications as internet-connected, routinely subject their applications to rigorous testing, and welcome external vulnerability reports.
- Data. All agencies should use “thorough data categorization” to better understand the sensitivity and security risks of the data they possess, take advantage of cloud security services to monitor access to their sensitive data, and implement enterprise-wide logging and information sharing.
All of this is in pursuit of the Administration’s “Zero Trust” strategy for cybersecurity. Zero trust architecture is a relatively new idea in cybersecurity that moves away from the traditional approach of securing the network perimeter. Instead, security focuses on users, assets, and resources; and authenticates them all the time — applying “zero trust” to users and assets, even once they’re inside the perimeter.
So, for example, federal agencies will need to adopt SSO for all applications employees use, including cloud-based services. They will also need to enforce multi-factor authentication at the application level; adopt new password policies dropping the use of special characters and check passwords against lists of known breached passwords, and end mandatory password-change periods. The goal is to achieve all that by Oct. 1, 2024.
Zero Trust Security Model: What You Need to Know
To be clear, the Biden Administration is not proposing to require all these security measures for the private sector within the next three years. Instead, these are the security goals that the Administration wants to achieve for the federal government itself.
But since the Administration also wants to embrace the use of SaaS providers, this means that on a practical level, SaaS providers bidding on government contracts will need to be able to meet these goals too. The U.S. federal government is an enormous purchaser of technology and software services. What it wants, it gets.

Using the NIST Cybersecurity Framework as a guide
For IT service providers that want to be prepared to compete in this Zero Trust security world, the good news is that the Biden Administration has already said that security standards and frameworks provided by NIST, the National Institute of Standards and Technology, will be the foundation for specific processes and controls that organizations should put in place.
Foremost, CISOs should use the NIST Cybersecurity Framework (CSF) as their guide for implementing policies, procedures, and controls that bring them into accordance with what the Biden Administration wants to achieve. NIST also publishes other guidance to help executives understand the principles behind Zero Trust Architecture, but the CSF spells out the control function, sub-categories, and specific control activities you can use.
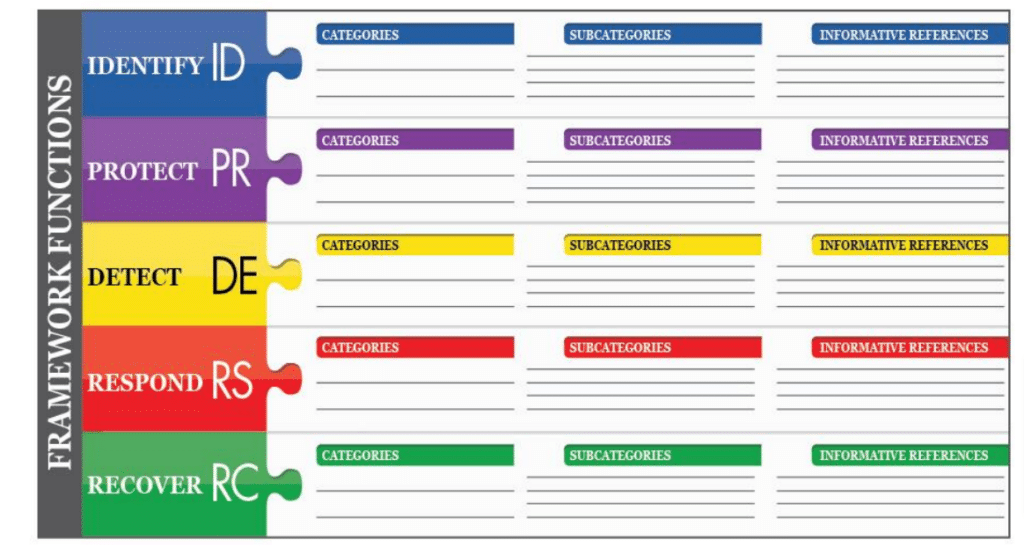
For example, the framework has a “protect” function, and one category of controls in that function is “identity management, authentication, and access control.” From there, the CSF defines relevant sub-categories, including the very first, PR.AC-1: “Identities and credentials are issued, managed, verified, revoked, and audited for authorized devices, users, and processes.” The CSF then connects that control sub-category to specific control activities in COBIT and ISO frameworks, as well as NIST’s own SP 800-53 control catalog of security and privacy controls.
So by using the CSF in a systematic, disciplined way, you can develop a clear picture of the remediation steps you’ll need to take. And you’ll be able to document your work along the way. That is exactly what external auditors and other stakeholders (including federal agencies seeking SaaS providers) will want to see.
To do all this, you will need a way to map NIST requirements to your current controls (or the lack thereof). Moreover, you’ll need a way to map the NIST requirements to controls specified by other frameworks — ISO 27001, PCI DSS, SOC 2, CSA CCM, and more — that you might have already implemented, so you can understand where those frameworks overlap and where one existing control might satisfy several regulatory compliance obligations.
Use the right tools for control mapping
As always, the mechanics of all this control mapping, remediation, and documentation will be challenging. To use spreadsheets is a fool’s errand; you’ll lose track of important evidence, overlook tasks, and never achieve the security posture you want. Use a governance, risk, and compliance tool (GRC) that can automate as much of the work as possible and allow you to rely on a single repository of data for reporting and analytics that can keep you and your board informed of what’s been done — and what should be done next.
For many IT investments, one challenge is to justify the expense of the project to the board. That may not be the case here, since embracing Zero Trust Architecture will both make your business more attractive to government customers and improve the organization’s security posture. You’re killing two birds with one stone.
What will really matter to your board is assurance on how you’ll make this transition to stronger cybersecurity: how you can demonstrate a disciplined path forward, one that can meet compliance standards and generate an audit trail for anyone who asks.
With the right technology, that allows you to take full advantage of the NIST Cybersecurity Framework, you can provide that assurance to the board. You can also bring your business into closer alignment with the Biden Administration’s objectives for cybersecurity in government operations — objectives that are getting closer day by day.
See Hyperproof in Action
Related Resources
Ready to see
Hyperproof in action?












