Guide
Cyber Safe Harbor Laws in the US: Everything You Need to Know

Introduction
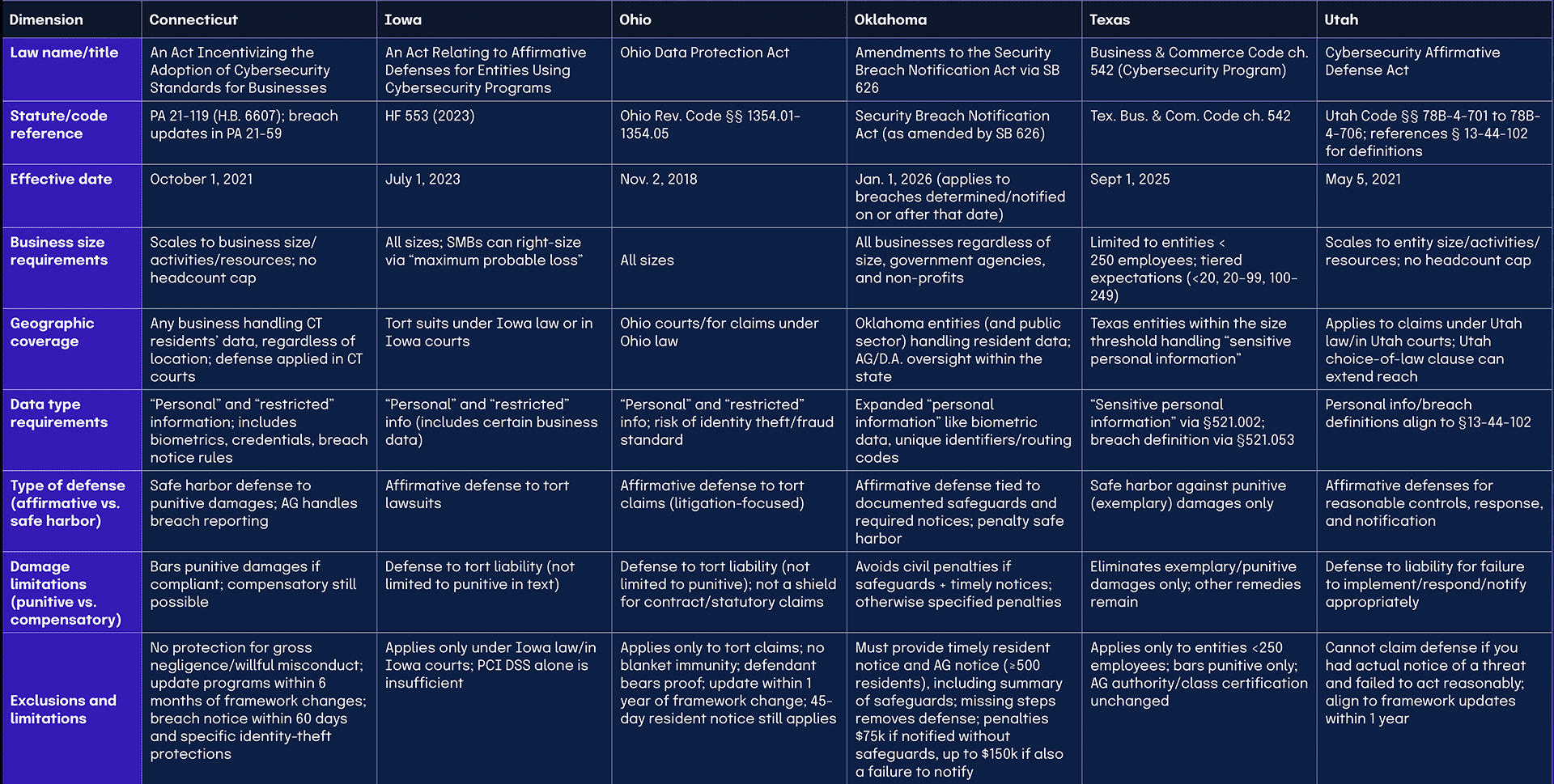
Cyber safe harbor laws in the United States are legislative measures designed to encourage businesses to adopt cybersecurity practices by offering legal protection against some types of claims following a data breach. These laws typically provide an affirmative defense against tort claims alleging that a failure to implement reasonable cybersecurity controls led to a breach, if the company can demonstrate compliance with specific requirements.

Common elements across these statutes include requirements for written cybersecurity programs that reasonably conform to established frameworks such as the NIST Cybersecurity Framework, FedRAMP, CIS Critical Security Controls, and the ISO 27000 family. The programs generally need to contain administrative, technical, and physical safeguards and be of appropriate scale and scope relative to the organization’s size, complexity, and available resources. While these provisions are typically standalone statutes rather than embedded within broader data-privacy laws, they often reference compliance with existing regulatory frameworks like HIPAA, the Gramm-Leach-Bliley Act, FISMA, and HITECH.
Only a limited number of states have enacted cyber safe-harbor legislation, with significant variation in their approaches and coverage.
Reference table for US cyber safe harbor laws
|
Dimension |
Connecticut |
Iowa |
Ohio |
Oklahoma |
Texas |
Utah |
|
Law name/title |
An Act Incentivizing the Adoption of Cybersecurity Standards for Businesses |
An Act Relating to Affirmative Defenses for Entities Using Cybersecurity Programs |
Ohio Data Protection Act |
Amendments to the Security Breach Notification Act via SB 626 |
Business & Commerce Code ch. 542 (Cybersecurity Program) |
Cybersecurity Affirmative Defense Act |
|
Statute/code reference |
PA 21-119 (H.B. 6607); breach updates in PA 21-59 |
HF 553 (2023) |
Ohio Rev. Code §§ 1354.01–1354.05 |
Security Breach Notification Act (as amended by SB 626) |
Tex. Bus. & Com. Code ch. 542 |
Utah Code §§ 78B-4-701 to 78B-4-706; references § 13-44-102 for definitions |
|
Effective date |
Oct. 1, 2021 |
July 1, 2023 |
Nov. 2, 2018 |
Jan. 1, 2026 (applies to breaches determined/notified on or after that date) |
Sept 1, 2025 |
May 5, 2021 |
|
Business size requirements |
Scales to business size/activities/resources; no headcount cap |
All sizes; SMBs can right-size via “maximum probable loss” |
All sizes |
All businesses regardless of size, government agencies, and non-profits |
Limited to entities < 250 employees; tiered expectations (<20, 20–99, 100–249) |
Scales to entity size/activities/resources; no headcount cap |
|
Geographic coverage |
Any business handling CT residents’ data, regardless of location; defense applied in CT courts |
Tort suits under Iowa law or in Iowa courts |
Ohio courts/for claims under Ohio law |
Oklahoma entities (and public sector) handling resident data; AG/D.A. oversight within the state |
Texas entities within the size threshold handling “sensitive personal information” |
Applies to claims under Utah law/in Utah courts; Utah choice-of-law clause can extend reach |
|
Data type requirements |
“Personal” and “restricted” information; includes biometrics, credentials, breach notice rules |
“Personal” and “restricted” info (includes certain business data) |
“Personal” and “restricted” info; risk of identity theft/fraud standard |
Expanded “personal information” like biometric data, unique identifiers/routing codes |
“Sensitive personal information” via §521.002; breach definition via §521.053 |
Personal info/breach definitions align to §13-44-102 |
|
Type of defense (affirmative vs. safe harbor) |
Safe harbor defense to punitive damages; AG handles breach reporting |
Affirmative defense to tort lawsuits |
Affirmative defense to tort claims (litigation-focused) |
Affirmative defense tied to documented safeguards and required notices; penalty safe harbor |
Safe harbor against punitive (exemplary) damages only |
Affirmative defenses for reasonable controls, response, and notification |
|
Damage limitations (punitive vs. compensatory) |
Bars punitive damages if compliant; compensatory still possible |
Defense to tort liability (not limited to punitive in text) |
Defense to tort liability (not limited to punitive); not a shield for contract/statutory claims |
Avoids civil penalties if safeguards + timely notices; otherwise specified penalties |
Eliminates exemplary/punitive damages only; other remedies remain |
Defense to liability for failure to implement/respond/notify appropriately |
|
Exclusions and limitations |
No protection for gross negligence/willful misconduct; update programs within 6 months of framework changes; breach notice within 60 days and specific identity-theft protections |
Applies only under Iowa law/in Iowa courts; PCI DSS alone is insufficient |
Applies only to tort claims; no blanket immunity; defendant bears proof; update within 1 year of framework change; 45-day resident notice still applies |
Must provide timely resident notice and AG notice (≥500 residents), including summary of safeguards; missing steps removes defense; penalties $75k if notified without safeguards, up to $150k if also a failure to notify |
Applies only to entities <250 employees; bars punitive only; AG authority/class certification unchanged |
Cannot claim defense if you had actual notice of a threat and failed to act reasonably; align to framework updates within 1 year |
Connecticut’s Cyber Safe Harbor Law
Basic law identification
What is the official name and citation of Connecticut’s cyber safe harbor law?

Connecticut’s cyber safe harbor law is formally titled An Act Incentivizing the Adoption of Cybersecurity Standards for Businesses (Public Act No. 21-119, H.B. 6607). It was signed on July 6, 2021, by Governor Ned Lamont and became effective on October 1, 2021. The law works in tandem with Public Act No. 21-59, which updated breach notification requirements.
Who enforces Connecticut’s cyber safe harbor law?
The law is applied in two ways: Connecticut courts apply the safe harbor defense during litigation, and the Office of the Attorney General oversees breach reporting and investigates violations. Businesses must demonstrate compliance with recognized frameworks to qualify for protection under these standards.
Where can businesses find the full text?
The statutes are published by the Connecticut General Assembly:
Law scope and applicability
Which organizations and data are in scope under Connecticut’s law?
The law applies broadly to any business that handles the personal or confidential information of Connecticut residents, regardless of its location. A Connecticut retailer storing loyalty card data and a California hospital processing patient records both fall under the definition of a covered entity.
What data is covered?
The law protects personal information like SSNs, taxpayer IDs, passport numbers, biometric data, and login credentials. It also introduces restricted information, defined as non-public data that can identify an individual if breached and left unencrypted.
What breaches are included?
Safe harbor protections apply in tort cases alleging a failure to implement reasonable safeguards that resulted in a data breach. The defense applies only to punitive damages, not compensatory damages.
Qualification requirements
What does a qualifying cybersecurity program include in Connecticut?
To qualify, companies must maintain a written cybersecurity program with administrative, technical, and physical safeguards. Programs must be scaled to match the business size, the sensitivity of the data, and the available resources.
Which frameworks qualify under Connecticut’s law?
Connecticut recognizes compliance with the following frameworks and standards:
Sector-specific regulations are also recognized:
What breach reporting rules apply?
Businesses must notify affected residents and the Attorney General within 60 days of discovering the breach. They must also provide at least 24 months of free identity theft protection when identifiers like SSNs are compromised. For login credential breaches, businesses cannot send notice to the compromised email account unless delivery can be verified.
Sector-specific applications
How does Connecticut’s cyber safe harbor law apply to financial services?
Financial institutions regulated by GLBA qualify if their security programs conform to GLBA standards. This means that banks and insurers can align their existing compliance programs with Connecticut requirements, rather than duplicating efforts.
How does the law affect small and medium businesses?
The law is explicitly scalable. Small and medium businesses can qualify by demonstrating proportional safeguards. This matters because small companies make up 50 to 75% of ransomware victims, according to the Department of Homeland Security’s commentary as a part of legislative discussions during the creation of this law.
Legal protections and limitations
What protections does Connecticut’s cyber safe harbor law provide?

The safe harbor protects businesses from punitive damages in data breach lawsuits if they can prove compliance with an approved framework. This is significant, as punitive damages often exceed compensatory damages and pose an existential risk to businesses.
What limits or exclusions apply under Connecticut’s law?
The law does not protect against claims involving gross negligence or willful misconduct. Businesses must also update programs within six months of framework amendments to maintain protection. Courts may scrutinize whether the framework used adequately addresses all forms of personal and restricted information.
Implementation and compliance
What steps should businesses take to qualify for Connecticut’s cyber safe harbor law?
- Select and adopt a recognized cybersecurity framework
- Develop a written cybersecurity program
- Implement safeguards across people, processes, and technology
- Scale controls based on business size and risk
- Document audits, policies, and risk assessments as evidence
- Update programs within six months of framework changes
- Meet breach reporting obligations, including the 60-day deadline and identity theft protections
How can Hyperproof help businesses meet Connecticut’s cyber safe harbor law requirements?
This implementation plan is designed to help your company meet the requirements of Connecticut’s cyber safe harbor law.
1. Select a recognized cybersecurity framework
Choose from our extensive library of compliance frameworks, including Connecticut-recognized frameworks like:
2. Develop a written cybersecurity program
Store and manage your organization’s cybersecurity policies in our integrated policy management system. This helps with managing the policy lifecycle, including approvals, ensuring you always have a copy of the most current and approved policy document ready.
3. Implement controls
Select and implement controls across people, process, and technology. Use our control objects to describe how your organization complies with your selected cybersecurity framework or frameworks.
4. Scale controls based on business size and risk
Use our Risk Register to identify, assess, and prioritize the risks that are specific to your company and your industry. Link these risks to your controls, and use our program health monitoring to establish a real-time view of how your controls mitigate risks.
5. Document audits, policies, and risk assessments
Maintain evidence of ongoing compliance by collecting and storing proof in Hyperproof. This can include using Hypersyncs for continuous evidence collection and the use of automated control testing to validate that controls are functioning properly. This helps to reduce the burden of preparing for external audits.
6. Update programs within six months of framework changes
Use tasks to remind stakeholders to check for framework changes or subscribe to framework update notifications from standards bodies. When a new revision is posted, use Hyperproof’s program updates to conduct a gap analysis between your current framework implementation and the new version. Modify your existing controls and procedures as needed within six months.
Iowa’s Cyber Safe Harbor Law
Basic law identification
What is the official name and citation of Iowa’s cyber safe harbor law?
The statute is titled “An Act Relating to Affirmative Defenses for Entities Using Cybersecurity Programs,” enacted as House File 553. It provides an affirmative defense to companies that run a program with administrative, technical, operational, and physical safeguards for personal and restricted information. The law took effect July 1, 2023, after the governor signed it on May 3, 2023.
Where can businesses find the full text?
The Iowa Legislature has a copy here.
How do courts apply Iowa’s safe harbor?
Iowa’s protection operates in litigation, not through an agency. A covered entity that satisfies the statute “is entitled to an affirmative defense to any tort lawsuit” related to a cyber breach, brought under Iowa law or in Iowa courts. This positioning makes the law a practical shield for defendants rather than a new enforcement regime.
Law scope and applicability
Which organizations and data are in scope under Iowa’s law?
The law applies to businesses that protect personal information and restricted information. Iowa’s definition of restricted information includes business data, broadening the scope of those who benefit from the defense and what must be protected. This reach matters for manufacturers, retailers, SaaS providers, banks, and hospitals doing business in Iowa.
What incidents are covered by the defense?
The defense is triggered by tort claims alleging a failure to adopt reasonable security measures that resulted in a data breach. The statute incentivizes programs that manage foreseeable risks, assess loss exposure, and communicate actions for affected parties, which can strengthen your position if litigation follows.
Qualification requirements
What does a qualifying cybersecurity program include in Iowa?
Your written program should include administrative, technical, operational, and physical safeguards, as well as continual risk mitigation, an annual maximum probable loss assessment, and clear, plain-language communications to affected parties if a breach is known to have occurred. These elements set a business-focused standard that boards and counsel can assess and audit.
Which frameworks qualify under Iowa’s law?
Reasonable conformity to a recognized framework qualifies. Options include:
Regulated entities can qualify by conforming to:
Want to learn more about PCI DSS’s program design? Check out this article.
How should you right-size budgets and scope?
Iowa allows right-sizing through maximum probable loss. The law states a program is “appropriate” if operating cost is no less than the most recently calculated maximum probable loss value, defined as “the greatest damage expectation” from a breach, based on “total value of possible damage multiplied by the probability” of occurrence. The statute does not expressly require spending this much to assert the defense, which is a decision point for counsel.
Sector-specific applications
How do financial services, healthcare, and critical infrastructure qualify in Iowa?
Banks and fintech firms can align to GLBA, hospitals can align to HIPAA and HITECH, and utilities or water systems can align to EPA, CISA, and NERC guidance. If the program reasonably conforms to these regimes, the business is deemed compliant for safe harbor purposes, which simplifies adoption across regulated industries.
What should small and mid-sized businesses prioritize?
SMBs face the same requirements as large enterprises, but the maximum probable loss mechanism helps calibrate spend to risk. Focus on a clear framework choice, an annual loss calculation, and evidence of operating the controls. This approach positions SMBs to claim the defense while controlling costs.
Legal protections and limitations
What protections does Iowa’s law provide?
When you meet the statute, you gain an affirmative defense to tort lawsuits arising from alleged inadequate security leading to a breach. However, the defense applies only under Iowa law or in Iowa courts, and PCI DSS alone is insufficient without pairing it with another listed framework.
Implementation and compliance
What helps you qualify in Iowa?

Pick a recognized framework that fits your regulators and customers, like NIST CSF or ISO 27001. Map controls, set metrics, and document evidence. Run an annual maximum probable loss assessment, record your assumptions, and align budget requests to the figure. Prepare breach communications that explain risk and user actions in clear language for customers, patients, or cardholders. Track framework updates and plan conformance within one year of revisions to maintain eligibility. For retail and e-commerce, pair PCI DSS with ISO or NIST to secure payment environments and maintain defense.
How can Hyperproof help businesses meet Iowa’s cyber safe harbor law requirements?
This implementation plan is designed to help your company meet the requirements of Iowa’s cyber safe harbor law.
1. Select and implement a recognized cybersecurity framework
Choose from our extensive library of compliance frameworks, like:
Regulated entities can qualify by conforming to:
If you’re using PCI DSS paired with another framework (or have other cybersecurity programs), you can use our jumpstarts to consolidate controls across frameworks, avoiding duplication while maintaining compliance.
2. Implement control health tracking
Use our Hypersyncs to eliminate manual proof gathering by connecting directly to external systems like AWS, Azure, and GitHub. Combine this with manual evidence collection when automation isn’t available. And use freshness tracking to monitor how effectively and frequently your controls are being operated.
3. Update programs within a year of framework changes
Use tasks to remind stakeholders to check for framework changes, or alternatively, subscribe to framework update notifications from standards bodies. When a new revision is posted, use Hyperproof’s program updates to conduct a gap analysis between your current framework implementation and the new version. Modify your existing controls and procedures as needed within one year.
Ohio’s Cyber Safe Harbor Law
Basic law identification
What is the official name and citation of Ohio’s cyber safe harbor law?

The law is the Ohio Data Protection Act in Ohio Revised Code §§ 1354.01–1354.05. It creates an affirmative defense for businesses that can show reasonable conformity to approved frameworks and meet program design requirements. The code also has no private right of action, which limits litigation exposure.
When did it take effect, and how does it work?
The Act took effect on November 2, 2018, after Sub. S.B. 220 was signed earlier that year. Qualifying companies can raise the defense in Ohio courts or for claims under Ohio law, reducing tort risk while keeping focus on business-fit security.
Who applies or “enforces” the safe harbor?
There is no administrative regulator for day-to-day enforcement. The safe harbor functions in litigation, where a defendant must prove its program met statutory design and framework requirements at the time of the incident.
Where can you read the full text?
You can review R.C. § 1354.01– R.C. § 1354.05 on severability in the Ohio Revised Code. These sections reflect the law’s litigation-focused design.
Law scope and applicability
Which organizations and data are in scope under Ohio’s law?
Any business, regardless of sector or size, may qualify if it maintains a conforming program. Coverage extends to financial institutions, nonprofits, higher education, retailers, and SaaS providers operating in or outside Ohio. The scope is intentionally broad to encourage adoption.
What types of data are in scope?
Two data classes matter. Personal information follows Ohio’s breach statute and ties a person’s name to sensitive identifiers when unencrypted. Restricted information reaches other identifiable data where a breach is likely to cause the material risk of identity theft or fraud.
What incidents are covered?
A qualifying breach involves unauthorized access and acquisition of computerized data that compromises covered information and creates a material risk of identity theft or fraud. The defense targets tort claims alleging failure to implement reasonable security that led to the breach.
Qualification requirements
What does a qualifying cybersecurity program include in Ohio?
Your program must be written and include administrative, technical, and physical safeguards designed to:
The scale and scope should reflect size, activities, data sensitivity, available tools, and resources.
Which frameworks qualify under Ohio’s law?
Recognized options include:
Industry-specific regulations like HIPAA, GLBA, FISMA, and HITECH can also qualify. PCI DSS must be paired with one of the listed frameworks when card data is in scope. Updates must be adopted within one year of any framework change.
Do incident response and notification rules change under the Act?
Ohio’s breach-notice rule remains in place. You must notify affected Ohio residents no later than 45 days after discovery, subject to law-enforcement delay and scoping exceptions. Federal sector rules like HIPAA and GLBA still apply. Keep a tested incident response plan to support both timely notice and defense.
Industry-specific applications
How does Ohio’s law fit financial services programs?
Banks and credit unions can align existing GLBA and PCI DSS work with a listed framework to qualify. This pairing strengthens litigation posture while leveraging current compliance investments, which is efficient for card-processing institutions and wealth managers.
What should small and midsize businesses expect?
The Act scales by design. A six-employee hardware store is not expected to mirror a regional bank’s program, yet both can reach the defense by aligning controls to risk and resources. The statute’s scaling factors help to guide spending, so you avoid over-engineering for low-sensitivity environments.
Legal protections and limitations
What protections does Ohio’s law provide?
If you reasonably conform to a recognized framework and meet design and scaling requirements, you can assert an affirmative defense to tort claims alleging inadequate security that resulted in a breach.
What limits or exclusions apply under Ohio’s law?
The defense applies to tort claims, not contract or statutory claims. It is not blanket immunity, and defendants carry the burden to prove conformity. Courts may still see expert disputes, which means cases can proceed beyond early motions. Forum and choice-of-law issues can also surface.
Implementation and compliance
What practical steps will help you to qualify?
Start with data mapping for personal and restricted information. Select a framework that fits your sector, then write and operate policies across admin, technical, and physical controls. Maintain evidence of conformity, test your incident response plan, meet the 45-day notice clock, and track framework changes so you update within one year.
How can Hyperproof help businesses meet Ohio’s cyber safe harbor law requirements?
This implementation plan is designed to help your company meet the requirements of Ohio’s cyber safe harbor law.
1. Select and implement a recognized cybersecurity framework
Choose from our extensive library of compliance frameworks, such as:
2. Manage your policies effectively
Use our integrated policy management system that handles the complete policy lifecycle with version control, approval workflows, and direct linking to implementing controls.
3. Collect evidence automatically
Use our Hypersyncs to eliminate manual proof gathering by connecting directly to external systems like AWS, Azure, and GitHub. Combine this with manual evidence collection when automation isn’t available. And use freshness tracking to monitor how effectively and frequently your controls are being operated.
4. Update programs within a year of framework changes
Use tasks to remind stakeholders to check for framework changes or subscribe to framework update notifications from standards bodies. When a new revision is posted, use Hyperproof’s program updates to conduct a gap analysis between your current framework implementation and the new version. Modify your existing controls and procedures as needed within one year.
Oklahoma’s Cyber Safe Harbor Law
Basic law identification
What is the official name and citation of Oklahoma’s cyber safe harbor law?
The amendments are outlined in the Security Breach Notification Act, as amended through SB 626, which takes effect on January 1, 2026. The updates add requirements to provide written notices to regulators, clarify definitions, and establish an affirmative defense tied to documented safeguards. Plan now, because the statute applies to breaches determined or notified on or after the effective date.
Who enforces the law, and where do you face exceptions?
Enforcement may be brought by the Oklahoma Attorney General or a district attorney, using the Oklahoma Consumer Protection Act framework. For state-chartered or state-licensed financial institutions, enforcement is exclusive to the primary state regulator. This allocation is crucial for banks that already coordinate with state regulators during examinations.
Law scope and applicability
Which organizations and data are in scope under Oklahoma’s law?
Coverage is broad across industries, from retail and healthcare to oilfield services and public agencies that collect resident data. The statute expands the definition of “personal information” to include government-created unique identifiers, a unique electronic identifier or routing code with required credentials, and unique biometric data like fingerprints or retina images. If you collect this data, you are in scope.
Which events trigger notice, and what goes to the Attorney General?
Resident notice must occur without unreasonable delay after breach determination. When a breach impacts 500 or more residents, you must notify the Attorney General within 60 days after a resident notices. The threshold is 1,000 or more for credit bureaus, and AG submissions are confidential. The AG notice includes the breach date, determination date, nature of the breach, types of data affected, residents impacted, estimated monetary impact (if known), and a description of safeguards implemented.
Qualification requirements
What does a qualifying cybersecurity program include in Oklahoma?

The law defines “reasonable safeguards” as “policies and practices that ensure personal information is secure, taking into consideration an entity’s size and the type and amount of personal information.” The term includes risk assessments, technical and physical layered defenses, employee training, and an incident response plan. Document these elements and review them periodically so you can prove eligibility during an investigation.
Which frameworks qualify under Oklahoma’s law?
While SB 626 does not name frameworks, many teams build programs that align with trusted standards to meet the statute’s definition. You can use the following for governance and control baselines:
Control catalogs like NIST SP 800-53 and contractor requirements like NIST SP 800-171 help you scope safeguards, while regulations like HIPAA, PCI DSS, FISMA, and FedRAMP define industry-specific practices.
Which notice steps preserve the safe harbor?
Safe harbor depends on timely, complete notice. Companies must provide resident notice without unreasonable delay, then provide AG notice within 60 days after resident notices if thresholds are met. The notice must include a summary of “any reasonable safeguards the entity employs.” Missing these steps removes the affirmative defense.
Sector-specific applications
How does the law affect financial services, healthcare, retail, and the public sector?
Banks gain two benefits. Enforcement is exclusive to the primary state regulator, and GLBA-compliant institutions are deemed compliant with resident notice if they also file the AG report. Healthcare entities that follow HIPAA or the Oklahoma Hospital Cybersecurity Protection Act receive a similar resident-notice pathway tied to an AG filing. Retailers and e-commerce platforms using biometrics now fall within the expanded definition of personal information, and public agencies using biometric access controls must align with the new definitions.
What practical examples highlight cross-industry impact?
From retailers to oilfield service companies, no sector is exempt from breach fallout, and starting in 2026, larger incidents bring AG oversight. Expect follow-up inquiries, especially where reporting is delayed. That scrutiny can influence insurance renewals, vendor terms, and board reporting.
Legal protections and limitations
What protections does Oklahoma’s law provide?
If you use reasonable safeguards and provide required notices, you will not be subject to civil penalties, and you can assert an affirmative defense. If you do not use safeguards but do notify, civil penalties are $75,000 plus actual damages.
If you also fail to notify, penalties can reach $150,000 per breach or series of similar breaches discovered in a single investigation. Penalties are based on the magnitude of the breach, the contribution, and any failure to notify.
What limits or exclusions apply under Oklahoma’s law?
Entities that follow GLBA, the Oklahoma Hospital Cybersecurity Protection Act, or HIPAA are deemed compliant with resident notice if they also notify the Attorney General. This is a notice safe harbor, not a waiver of AG reporting.
Implementation and compliance
What should you do before January 1, 2026?
Establish an auditable program that legal, risk, and security leaders can defend. Inventory and classify personal information, including biometrics and account identifiers. Run a risk assessment, then close high-impact gaps that affect breach likelihood or impact. Implement layered controls, such as encryption and multi-factor authentication, and enforce access governance. Update and test your incident response plan, including templates for resident and AG notices. Train employees on handling personal information and refresh their knowledge on a schedule tied to their role risk.
How can Hyperproof help businesses meet Oklahoma’s cyber safe harbor law requirements?
This implementation plan is designed to help your company meet the requirements of Oklahoma’s cyber safe harbor law.
1. Select and implement a recognized cybersecurity framework
Use our library of predefined framework templates, including NIST CSF, ISO 27001, and the CIS Critical Security Controls. Use jumpstarts to map related requirements across frameworks and avoid duplicating work if you’re managing multiple standards.
2. Implement and monitor controls
Implement technical, operational, and preventative controls associated with your selected cybersecurity framework. Use our Hypersyncs to automatically collect evidence of control effectiveness and to demonstrate proof of implementation.
3. Conduct a risk assessment and close high-impact gaps
Use the Risk Register as a centralized location to identify, assess, and prioritize risks, including security breaches. Prioritize your risks based on likelihood and impact, then link gaps to specific controls in your chosen cybersecurity framework. Use Issues to track remediation progress when closing high-impact gaps.
Texas’s Cyber Safe Harbor Law
Basic law identification
What is the official name and citation of Texas’s cyber safe harbor law?

The measure is Senate Bill 2610, and it creates Chapter 542, Cybersecurity Program, in the Texas Business and Commerce Code. The code sets definitions, applicability, and the exemplary damages safe harbor for qualifying entities.
Where can businesses find the full text?
The bill is published on the Texas Legislature website here.
When was it signed, and when does it apply?
Governor Greg Abbott signed the bill on June 20, 2025, and the law applies to cases accruing on or after September 1, 2025.
Who enforces it, and what does that mean for you?
Chapter 542 does not limit the Texas Attorney General’s authority, and it does not affect class certification. The safe harbor serves as a defense against punitive damages, while other remedies remain in effect.
Law scope and applicability
Which organizations and data are in scope under Texas’ law?

Coverage is limited to entities with fewer than 250 employees that own or license computerized data containing sensitive personal information. Definitions incorporate § 521.002 for personal and sensitive data, as well as § 521.053 for breaches of system security.
What business problem does this solve?
The shield can lower litigation risk for SMBs across sectors like clinics, law firms, title agencies, retail, and managed services. Punitive damages can be substantial, and removing that exposure alters the settlement math following a breach.
Qualification requirements
What does a qualifying cybersecurity program include in Texas?
A program must include administrative, technical, and physical safeguards, conform to an industry-recognized framework, and be designed to prevent unauthorized access that could create a material risk of identity theft or fraud. Proof that the program existed and was maintained at the time of a breach is required.
Which frameworks qualify under Texas’ law?
Recognized options include:
Texas uses a size-based tiering model. Fewer than 20 employees follow simplified measures, 20–99 employees implement CIS Controls IG1, and 100–249 employees align with broader frameworks, like the NIST CSF or ISO/IEC 27000.
What documentation strengthens your defense if your company is sued?
Maintain written policies, training records, risk assessments, audits, and incident logs. The safe harbor hinges on your ability to demonstrate that you implemented and maintained the program at the time of the breach.
Industry-specific applications
How does the law align with HIPAA, GLBA, and PCI DSS?
If your organization is already subject to federal or industry requirements, your current compliance can satisfy the framework element. Examples include HIPAA for healthcare, GLBA for certain financial services, and PCI DSS for payment card environments, provided the program meets the statute’s design criteria.
How should professional services, clinics, and title agencies think about tiering?
Small teams often hold large volumes of personal data, which raises risk beyond headcount. Examples include a 10-employee law firm with thousands of client files, a dental practice with patient histories, and a title or insurance agency processing mortgage or policy documents. Right-sizing controls to data risk matters.
Legal protections and limitations
What protection does Texas’s safe harbor provide?
In a breach-related action, a harmed person may not recover exemplary damages if the covered business proves it implemented and maintained a compliant program at the time of the breach.
What limits still apply, and what does not change?
The shield applies only to punitive damages, not compensatory damages. It applies to entities with fewer than 250 employees handling sensitive personal information. The Attorney General’s authority and class certification remain unaffected.
Implementation and compliance
What are the most efficient steps to qualify in Texas?
How can Hyperproof help businesses meet Texas’s cyber safe harbor law requirements?
This implementation plan is designed to help your company meet the requirements of Texas’s cyber safe harbor law.
1. Select and implement a recognized cybersecurity framework
Use our library of predefined framework templates, including NIST CSF, CIS Controls, FISMA for federal environments, FedRAMP for cloud providers, and CIS Controls IG1 for companies with 20–99 employees.
2. Implement and monitor controls
Implement technical, operational, and preventative controls associated with your selected cybersecurity framework. Use our Hypersyncs to automatically collect evidence of control effectiveness and to demonstrate proof of implementation. Prioritize closing any control gaps if you’ve already deployed a recognized cybersecurity framework.
3. Track your risks
Use our Risk Register to identify, assess, and prioritize risks across systems, vendors, and processes. Create entries in the risk register based on security breaches, regulatory changes, and other risks that would impact your business.
Utah’s Cyber Safe Harbor Law
Basic law identification
What is the official name and citation of Utah’s cyber safe harbor law?
Utah’s Cybersecurity Affirmative Defense Act is defined in Utah Code Title 78B, Chapter 4, Part 7, covering § 78B-4-701 through § 78B-4-706, originally enacted as H.B. 80. It establishes three affirmative defenses tied to a written cybersecurity program that existed at the time of the breach. You will find the defenses for reasonable controls, appropriate response, and appropriate notification in § 78B-4-702.
Where can businesses find the full text?
The statute text is published here:
What effective date and legal provisions matter most?
The Act went into effect on May 5, 2021, and it functions as a defense within litigation, not as a new cause of action. It also includes a choice-of-law rule so agreements designating Utah law apply this part to the fullest extent possible, even if a case is filed elsewhere.
Law scope and applicability
Which organizations and data are in scope under Utah’s law?

The statute applies to a broad “person,” including corporations, partnerships, associations, and financial institutions. Coverage follows Utah’s definitions for personal information and breach of system security by incorporating § 13-44-102, aligning the defense with Utah’s breach law. This makes scoping straightforward for legal teams.
Where does the defense apply across jurisdictions?
The defense applies to claims under Utah law or in Utah courts. A contractual Utah choice-of-law clause extends application to the fullest extent possible, even if a case is brought in another state. This helps multi-state operators and SaaS providers.
Qualification requirements
What does a qualifying cybersecurity program include in Utah?
Your written program must provide administrative, technical, and physical safeguards designed to protect confidentiality, integrity, and security, to anticipate threats, and to prevent breaches. It must fit your size, activities, data sensitivity, tool availability, and resources. Designate a coordinator, train staff, run risk assessments, and adjust controls as conditions change.
Which frameworks qualify under Utah’s law?
Your program can reasonably conform to one or more options, including:
Industry regulations can also qualify when applicable, like HIPAA or FISMA, and PCI DSS for card data. If a framework is updated, companies must align within one year, and similarly align to amended regulations in a reasonable time.
What response and notification practices must exist to claim the defense?
To claim the response or notification defenses, you must have had documented breach-response and notification protocols at the time of the incident, and you must have followed them. The statute focuses on having and following your program.
Sector-specific applications
How should financial services, healthcare, and retail map existing controls?
Financial institutions are included in the statute’s definition of person. For regulated data, reasonable compliance with the governing regime can satisfy Utah’s recognized-framework requirement, like GLBA for banks and HIPAA for healthcare. Retailers handling card data can rely on PCI DSS for that environment. Map your existing controls to Utah’s program elements, then document the fit.
What is a practical path for small and medium businesses?
The law is designed to scale, with a comparably low barrier to compliance. Programs need to reasonably conform to approved frameworks and feature document risk assessments. SMBs can use IG1 from the CIS Critical Security Controls® to get started easily and quickly.
How does this help other industries like tech startups and manufacturers?
Tech startups can adopt NIST CSF to guide planning, while implementing NIST SP 800-171 or IG2 / IG3 of the CIS Critical Security Controls® as they scale. Manufacturers can alternatively choose ISO 27001, keeping Utah’s scaling factors in view.
Legal protections and limitations
What protections does Utah’s law provide?
A qualifying program provides an affirmative defense to claims that a company failed to implement reasonable controls, failed to respond appropriately, or failed to notify appropriately. This is a defense to liability, not a penalty discount, and it can benefit out-of-state disputes through Utah choice-of-law.
What limits or exclusions apply under Utah’s law?
You cannot claim the defense if you had actual notice of a threat, did not act in a reasonable time to take known remedial steps, and that issue caused the breach. The statute clarifies that a risk assessment alone is not actual notice. Document threat intake, actions, and timelines to avoid disputes on notice.
Implementation and compliance
What are the fastest steps to qualify?
Adopt a written program that protects personal information, anticipates threats, and prevents breaches. Select one or more recognized frameworks that match your regulators and contracts, then right-size controls to your business. Stand up incident-response and notification playbooks, train teams, and run a risk assessment you can show in court. Procedures and policies should ideally link directly to the relevant controls from NIST SP 800-171, NIST SP 800-53, FedRAMP, CIS Critical Security Controls®, ISO 27001, HIPAA, FISMA, and PCI DSS.
How should you handle updates and ongoing proof?
Track framework and regulatory changes, then align with the statute’s timing expectations. Keep evidence current, including coordinator designation, training records, assessment results, and change logs. Treat change management as part of your control design, not an afterthought.
How can Hyperproof help businesses meet Utah’s cyber safe harbor law requirements?
This implementation plan is designed to help your company meet the requirements of Utah’s cyber safe harbor law.
1. Select a recognized cybersecurity framework
Choose from our extensive library of compliance frameworks, including recognized frameworks like:
2. Develop a written cybersecurity program
Store and manage your organization’s cybersecurity policies in our integrated policy management system. This helps with managing the policy lifecycle, including approvals, ensuring you always have a copy of the most current and approved policy document ready.
3. Implement controls
Select and implement controls across people, process, and technology. Use our control objects to describe how your organization complies with your selected cybersecurity framework or frameworks.
4. Scale controls based on business size and risk
Use our Risk Register to identify, assess, and prioritize the risks that are specific to your company and your industry. Link these risks to your controls, and use our program health monitoring to set up a real-time view of your controls in reducing risks.
5. Document audits, policies, and risk assessments
Maintain evidence of ongoing compliance by collecting and storing evidence in Hyperproof. This can include using Hypersyncs for continuous evidence collection, and the use of automated control testing to validate that controls are working. This helps to reduce the burden of preparing for external audits.
6. Update programs within a year of framework changes
Use tasks to remind stakeholders to check for framework changes or subscribe to framework update notifications from standards bodies. When a new revision is posted, use Hyperproof’s program updates to conduct a gap analysis between your current framework implementation and the new version. Modify your existing controls and procedures as needed within one year.
Download the PDF