How to Balance Multiple Audits Simultaneously
Modern organizations face a variety of audits simultaneously, each with distinct objectives that collectively shape their cybersecurity and GRC programs. These audits typically fall into the regulatory, certification, and customer categories, creating a multifaceted compliance environment that demands careful planning and management. Understanding the scope and purpose of each audit type helps organizations prioritize resources and align their strategies effectively.
Customer audits, driven by clients or business partners, assess whether vendors meet specific security expectations before or during contractual engagements. Often centered on SOC 2® reports, these audits verify principles such as security and confidentiality, particularly for service providers handling sensitive data. The simultaneous nature of these audits frequently strains organizational capacity because each comes with unique timelines, scopes, and reporting needs. Some overlap in security controls may offer potential efficiencies, but diverse stakeholder expectations and legal implications make a unified approach to preparation and execution critical for maintaining compliance without disrupting core business functions.
What costs do companies incur from poor audit coordination?
Failing to coordinate audits effectively creates significant financial and operational burdens for the organizations, disrupting compliance efforts and overall business stability. Inefficient audit management often results in wasted resources, escalated costs, and critical gaps in compliance that can damage the organization’s reputation and legal standing. The consequences extend beyond immediate expenses, affecting long-term organizational health and employee well-being.
Financially, poor coordination may lead to redundant work, like creating separate documentation for similar controls across frameworks such as SOC 2® and ISO 27001, inflating the costs of staff time, external consultants, and compliance tools. Failed audits or missed deadlines due to disorganized planning can also trigger penalties or necessitate expensive corrective actions. Operationally, these inefficiencies may divert attention from the primary business goals, slowing down initiatives such as product development or client service delivery, which can weaken market position and revenue potential.
The human toll is equally concerning, as inadequate audit planning contributes to staff burnout. Compliance teams that face the continuous cycles of evidence gathering and auditor interaction without sufficient support often have low morale and higher turnover. Additionally, compliance gaps from overstretched resources heighten security vulnerabilities, risking breaches and loss of client trust. A high-visibility audit failure can erode stakeholder confidence, impacting partnerships and growth.
Addressing these costs requires a cohesive audit strategy that prioritizes automation, allocates resources efficiently, and maps overlapping controls to minimize duplication, ensuring staff are supported and compliance obligations are met without sacrificing operational priorities or security standards.
How do overlapping audit requirements create complexity for organizations?
Managing multiple audit frameworks concurrently presents a significant challenge for organizations due to the distinct yet intersecting demands of each. Regulatory audits, like those mandated by the GDPR or HIPAA, require detailed documentation and carry penalties for non-compliance, while certification audits, such as ISO 27001, validate adherence to industry standards and bolster credibility. Frameworks, such as the SOC 2®, the NIST CSF, and the Payment Card Industry Data Security Standard (PCI DSS), aim to ensure data security and operational integrity, but they differ in their specific criteria, processes, and focus areas. This divergence often leads to competing priorities that challenge resource allocation and operational focus.
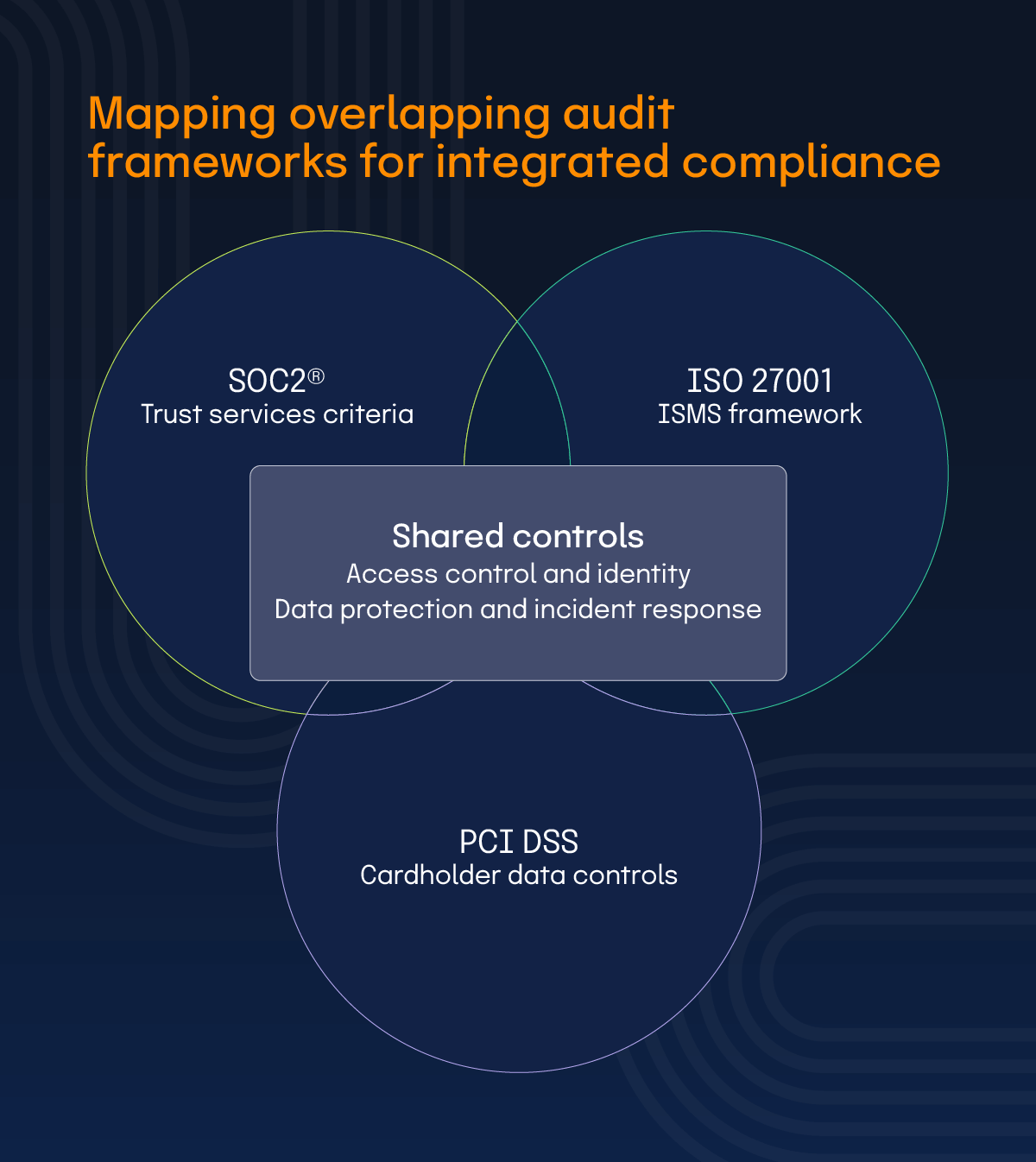
SOC 2® audits emphasize the trust services criteria, including security, availability, and confidentiality, targeting service providers to assure clients of data protection practices. ISO 27001 mandates a broader Information Security Management System (ISMS), requiring thorough risk assessments and continuous policy updates across all organizational levels. PCI DSS, on the other hand, focuses narrowly on protecting cardholder data with strict, non-negotiable controls for payment-processing entities. Preparing for an SOC 2® audit might prioritize system performance metrics, while ISO 27001 requires extensive documentation of risk management practices, and PCI DSS imposes rigid timelines tied to transactional compliance. To address these challenges, organizations must integrate compliance efforts by mapping shared controls across frameworks, streamlining audit preparation and reducing the strain on personnel and budgets while ensuring all audit obligations are addressed.
How can strategic planning and resource allocation improve multi-audit management?
Creating an effective audit prioritization process is essential for organizations managing multiple compliance obligations. This approach involves categorizing audits based on risk, impact, and resource requirements, often using classifications like high-touch, standard, and low-touch to guide focus and effort allocation. By systematically ranking audits, organizations can address the most critical requirements first while optimizing limited resources.

High-touch audits are those with significant risk and impact, often involving regulatory mandates like the GDPR or customer-driven assessments with major contractual implications. These may demand extensive preparation, detailed documentation, and direct senior leadership involvement because non-compliance could lead to fines or lost business.
Standard audits, like routine certification checks for ISO 27001, carry moderate risk and require consistent but less intensive resources, often managed by dedicated compliance teams with established processes. While ISO 27001 certifications are important, they generally fall into the standard tier because they do not carry the same immediate financial penalties as GDPR or similar regulatory or legal violations.
Low-touch audits, typically internal reviews or less critical customer requests, pose minimal risk and impact, allowing for streamlined efforts with basic resource allocation.
This tiered classification helps organizations assess each audit’s urgency and resource needs, ensuring high-touch audits receive priority without neglecting others. Implementing a classification framework like this requires continuous evaluation of audit scopes and organizational priorities, adjusting categorizations as risks or business needs shift. This method not only clarifies where to direct energy but also prevents resource overallocation to less impactful audits, maintaining balance across compliance activities and safeguarding operational stability. Finally, organizations should weigh potential regulatory penalties against the resource-complexity factors, allowing organizations to balance potential financial or legal exposure with staffing limits.
What strategies are involved in capacity planning and buffer creation?
Effective capacity planning and buffer strategies are vital for organizations aiming to manage audit workloads without encountering resource conflicts or staff burnout. These approaches involve building strategic time buffers and distributing workloads thoughtfully to maintain operational equilibrium and compliance success. Proactive planning helps anticipate demands and allocate resources in a way that sustains team performance over extended audit cycles. Common practices often cap individual utilization at about 80% of available hours and allocate buffers of roughly 10-15% of estimated effort.
To accommodate the complexity of high-touch audits, organizations often build strategic time buffers, adding extra time to schedules for the high-priority frameworks, to absorb unexpected delays without derailing the process. These buffers involve scheduling additional time beyond the minimum required for audit preparation and execution, providing space for quality checks, and ensuring submissions meet standards before deadlines. Effective workload distribution focuses on staggering audit tasks across teams and timeframes, preventing overlap of intensive phases for multiple audits like ISO 27001 and PCI DSS, which can overwhelm staff if concurrent.
Preventing burnout is a core benefit of these strategies. By spacing out peak efforts and maintaining buffers, organizations reduce the pressure on compliance teams, allowing recovery periods between audits and fostering sustained productivity. Capacity planning also involves forecasting resource needs based on historical audit data and upcoming obligations, ensuring staffing levels align with demand. Regularly reviewing workloads and adjusting schedules as new audits emerge keeps the balance intact. These measures collectively minimize the risk of errors from rushed work, protect employee well-being, and ensure compliance obligations are met without sacrificing the quality of preparation or overall organizational focus.
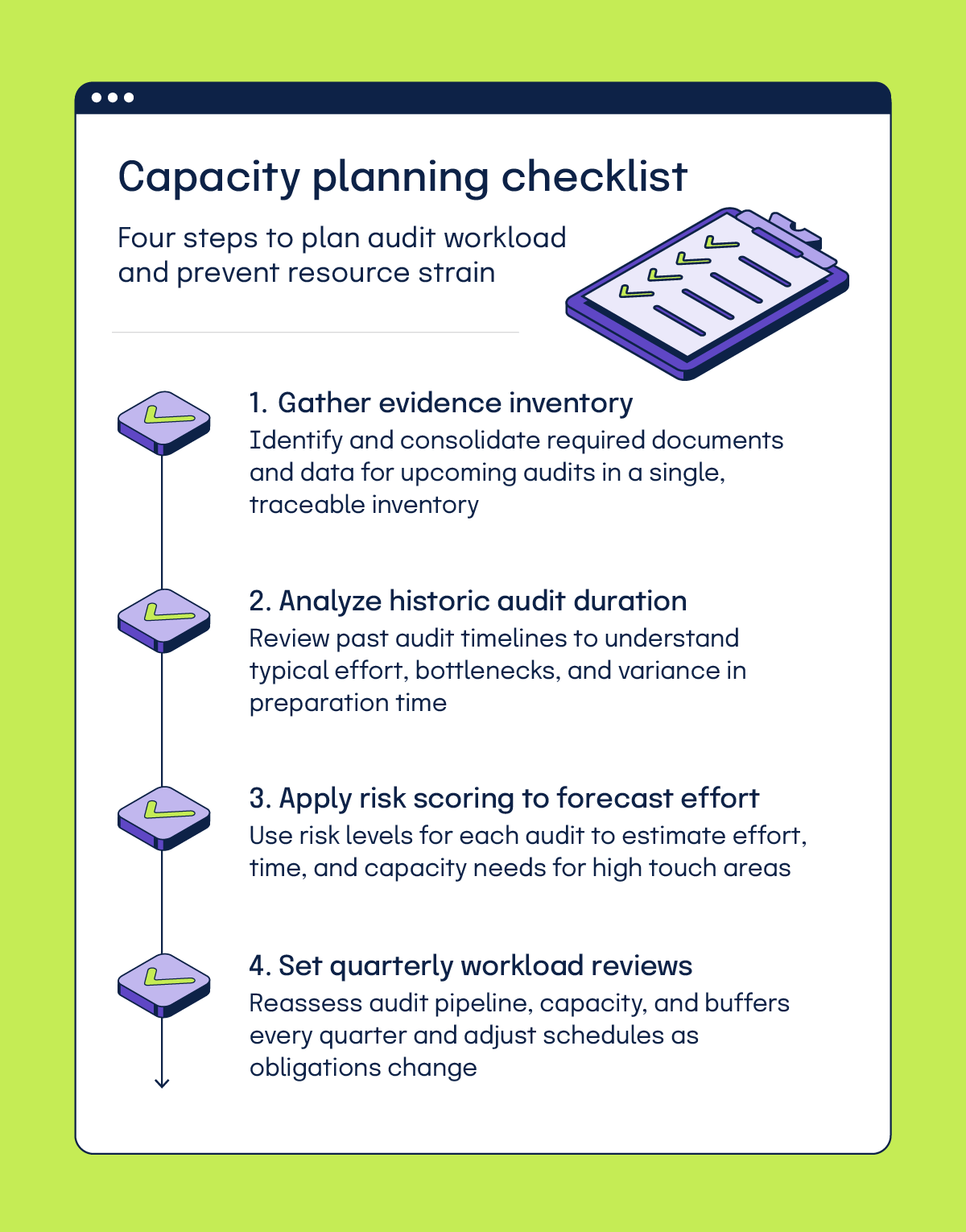
Capacity planning checklist
- Gather evidence inventory
- Analyze historic audit duration
- Apply risk-scoring to forecast effort
- Set quarterly workload reviews
How does dynamic resource management support fluctuating audit demands?
Building flexible team structures is a key strategy for managing the fluctuating demands of audits. Dynamic resource management involves creating adaptable setups with the core audit teams, rotational specialists, and reserve capacity to handle unexpected surges in workload. This approach ensures organizations can respond to audit requirements without compromising other operational needs.
Core audit teams form the backbone of compliance efforts, consisting of dedicated professionals who oversee recurring audits and maintain continuity in processes such as evidence collection and auditor coordination. These individuals possess deep knowledge of frameworks like SOC 2® and ISO 27001, enabling consistent handling of standard audit cycles. Specialists, drawn from other departments or external consultants, bring particular expertise, like technical skills for PCI DSS assessments, on an as-needed basis. Their temporary involvement addresses niche requirements without permanently inflating team size.
Reserve capacity, comprising cross-trained staff or contingency plans for outsourcing, acts as a buffer for unforeseen demands, such as sudden regulatory audits or accelerated client requests. This flexibility prevents overstretching the core teams and mitigates the risk of delays or errors during peak audit periods. Implementing dynamic resource management requires clear communication channels and predefined roles to quickly mobilize personnel when needed.
Why is centralized evidence management important for audit processes?
Creating a unified evidence repository is a cornerstone of effective audit management, which involves creating a structure that organizes evidence by control framework, evidence type, and business process, all underpinned by standardized metadata. Such a system ensures quick access to critical documentation and maintains consistency across multiple audits.
Organizing by control framework, like SOC 2® or ISO 27001, allows teams to align evidence with specific compliance requirements, simplifying retrieval during audits. Categorizing by evidence type, such as policies, logs, or screenshots, further refines the structure, making it easier to identify relevant materials for particular controls. Linking evidence to business processes ensures traceability, showing how specific practices or systems meet audit criteria, which is vital for demonstrating operational integration to auditors.
Standardized metadata, including tags for dates, owners, and applicable frameworks, can enhance searchability, version control, and access management within a secure, centralized platform that protects sensitive information while enabling collaboration among compliance teams. Regular reviews of the structure help adapt it to new frameworks or organizational changes, maintaining its relevance.
Organizations using Hyperproof achieve a 50-70% reduction in audit preparation time, save up to 80 hours per month, and see a 40-60% reduction in overall audit effort.
What are effective cross-audit evidence reuse strategies?
Maximizing evidence reuse across audits is a practical way to enhance efficiency in cybersecurity and GRC programs. Developing evidence mapping matrices offers a systematic method to achieve high reuse rates by identifying overlapping requirements among related frameworks, thereby reducing redundant efforts. This approach saves time and resources while maintaining compliance integrity across multiple audit types.
An evidence mapping matrix links specific pieces of evidence, like access control logs or incident response plans, to controls in various frameworks such as SOC 2®, ISO 27001, and PCI DSS. By visually charting where one document or data set satisfies multiple audit criteria, teams can pinpoint reusable assets and avoid duplicating collection efforts. For instance, a single security policy might address confidentiality in SOC 2® and risk management in ISO 27001, serving dual purposes with minimal adjustments.
Sample evidence mapping matrix
| Number | Evidence item | Framework/control reference | How the evidence satisfies the requirement | Notes/annotation context-specific addendum |
|---|---|---|---|---|
| 1. | Incident Response Plan (IRP) – documented procedure for detection, response, communication, lessons learned | SOC 2® – Trust Services Criteria: Security (CC7.1 Monitoring & Responding) and Availability (A1) | The IRP demonstrates that the organization detects, escalates, and responds to security incidents and has procedures to maintain system availability | Include version date, review logs, summary of last incident, improvements, and note that the IRP maps to PCI and ISO controls |
| ISO 27001 – Annex A: A.16.1 (Management of information security incidents and improvements) | Provides the documented processes required for incident handling, roles/responsibilities, escalation, communication, and continuous improvement | Add alignment to Statement of Applicability (SoA), link to risk register, and note how incident learning feeds corrective actions | ||
| PCI DSS – Requirement 12.10 (Incident Response Plan) | Meets PCI DSS’s explicit requirement to maintain a documented incident response plan for potential cardholder data breaches | Note CDE applicability, responsible personnel, last tabletop test date, and any required QSA clarifications | ||
| 2. | Access control and log review policy + associated logs | SOC 2® – Security (CC6: Logical access) | The policy defines access provisioning, modification, and removal, while logs demonstrate actual enforcement and monitoring of access | Include policy version, access-review frequency, exceptions, audit observations, and mapping to multiple frameworks |
| ISO 27001 – Annex A.9 (Access control) and A.12.4 (Logging & monitoring) | Demonstrates both design (policy) and operational effectiveness (logs) of access control, authentication, authorization, and audit-trail monitoring | Add evidence-retention period, review cadence, deviations, and link to risk assessment and SoA | ||
| PCI DSS – Requirement 7 (Restrict access) & 10 (Logging, tracking) | Shows that access to cardholder data is restricted by role and that access-related events are logged, reviewed, and monitored | Note scope of access to CDE, privileged-access controls, exception approvals, and enforcement of least privilege | ||
| 3. | System backup and recovery logs/reports | SOC 2® – Availability (A1) & Security (CC3: Risk Mitigation) | Backup logs prove the recoverability of data and that operational steps exist to mitigate availability-related risks | Indicate last successful recovery test, backup retention, failed jobs, and any corrective actions |
| ISO 27001 – Annex A.8.3 (Backup) and A.17 (Business continuity) | These logs verify execution of scheduled backups, testing of restore procedures, and alignment with continuity requirements | Add restore time objectives (RTO), backup scope, and linkage to the business continuity plan and SoA | ||
PCI DSS – Requirement 9.5.1 (Media backup) & 12.3 (Risk management) | Demonstrates that backups containing cardholder-data-relevant systems are protected, retained, and recoverable | Clarify encryption of backup media, scope related to CDE, and mapping to risk management processes |
Implementing this strategy requires detailed analysis of framework overlaps and regular updates to the matrix as standards or business practices shift. It also demands clear documentation within the matrix, often necessitating annotations or context-specific addenda to meet unique reporting needs. Storing the matrix in a centralized system alongside the evidence repository aids accessibility for compliance teams. By comparison, this is achieved easily in Hyperproof with the use of the Labels feature.
By prioritizing cross-audit reuse, organizations streamline audit preparation and lessen the burden on staff tasked with gathering materials. This ensures consistency in how controls are evidenced, which can bolster auditor confidence and improve overall compliance outcomes without sacrificing quality or detail in submissions.
How does automated evidence collection implementation enhance audit efficiency?
Integrating automated evidence collection into audit processes marks a significant step forward in managing cybersecurity and GRC obligations efficiently. This approach leverages technical tools and workflow automation, through Application Programming Interfaces (APIs) and streamlined processes, to gather evidence with minimal manual intervention. Automation reduces human error and frees up compliance teams for higher-value tasks like analysis and remediation.
APIs play a critical role by connecting systems to pull data directly from security tools, such as firewalls or identity management platforms, ensuring real-time evidence like access logs or configuration settings is captured accurately. Workflow automation ties these technical collections into broader processes, scheduling regular extractions or triggering captures based on audit timelines, thus maintaining a steady flow of updated evidence without constant oversight.
You can build a practical workflow by following these steps:

- Select a GRC platform like Hyperproof that supports automation through Hypersyncs, then mapping each control to the relevant data source.
- Configure the necessary APIs or snapshot mechanisms,
- Set up a schedule to collect evidence on a regular cadence
- Run validation and testing cycles to confirm completeness and accuracy before audit submission
Implementation requires careful planning to align automation with audit needs. Organizations should identify which controls benefit most from automated collection, map data sources to specific requirements, and ensure tools integrate seamlessly with existing infrastructure. Security remains paramount; automated systems must protect sensitive data through encryption and access restrictions to prevent unauthorized exposure. Regular testing of these mechanisms ensures reliability, while fallback manual processes cover potential technical failures. By adopting automated evidence collection, organizations enhance the speed and accuracy of audit preparation, cut down on repetitive tasks that strain resources, and build a more sustainable compliance program capable of scaling with growing regulatory demands.
How can audits be streamlined with standardization and workflow optimization?
Setting up comprehensive template libraries and response frameworks can further streamline audit processes. By creating a centralized, reusable set of templates — covering control narratives, evidence requests, and finding responses — organizations gain pre-structured formats with standardized sections that promote consistency and completeness. These include:
Storing all templates in an accessible system supports regular updates to reflect newer standards, which may reduce the need to recreate documents for each audit, lower preparation errors, and help align responses with the expected formats, thereby supporting credibility with auditors.
How can audit response playbooks improve audit outcomes?
Developing situation-specific audit response playbooks is an effective way to prepare for the diverse demands of compliance in cybersecurity and GRC programs. These playbooks provide teams with detailed guidance for different audit types — like regulatory, customer-driven, or certification audits — covering pre-audit, execution, and closure phases. Customized, organization-specific instructions ensure teams approach each audit with clarity and confidence, reducing the risk of oversight during critical stages.
Playbooks lay out a clear roadmap for each audit stage:
Developing these playbooks involves analyzing past audits to spot recurring patterns and creating content for the specific frameworks or auditor expectations. Regular reviews and updates incorporate lessons learned and new regulatory requirements, keeping the playbooks relevant and useful.
Need an audit response playbook to get started? We’ve got you covered.

What considerations are key for crisis management and contingency planning during audits?
Handling unexpected challenges during audits is a vital part of maintaining compliance. Crisis management and contingency planning focus on preparing for common issues like key personnel unavailability, missing evidence, and scope expansions, ensuring organizations can adapt without derailing the audit process. Proactive strategies mitigate risks and preserve audit integrity under pressure.
Key personnel unavailability due to illness, turnover, or conflicting priorities can stall progress, especially when specific expertise is needed for frameworks like ISO 27001 or SOC 2®.
Contingency plans address this by identifying backup roles, cross-training staff, and maintaining detailed documentation so others can step in seamlessly.
Missing evidence poses another frequent hurdle, often arising from miscommunication or incomplete records. Plans to counter this include establishing rapid response protocols to source alternative documentation or escalate issues to senior staff for resolution, alongside preventive measures such as regular evidence audits. Typically, this starts with logging the missing evidence, then proposing alternative sources (for example, a system-generated report), assigning a remediation deadline, and, if the gap remains, escalating the issue to senior management. Hyperproof helps reduce the possibility of missing evidence through Hypersyncs and control health evaluations, which can proactively identify if a control is missing evidence.
Scope expansions, where auditors broaden their focus mid-process, can strain resources and timelines. Contingency strategies involve setting aside buffer time and resources in the planning stages, as well as defining clear communication channels with auditors to negotiate manageable adjustments. This can also be handled proactively during the contracting phase with auditors.
Effective crisis management requires creating detailed response plans, conducting drills to test them, and ensuring all team members understand their roles during disruptions. By preparing for such challenges, organizations maintain control over audits, reduce stress on teams, and uphold compliance standards even when faced with unforeseen challenges, ensuring outcomes remain aligned with expectations.
What factors should guide GRC platform selection and implementation?
Selecting and implementing a GRC platform like Hyperproof can dramatically improve audit management for cybersecurity and compliance teams. Hyperproof offers a comprehensive solution with multi-framework support, allowing organizations to manage controls for standards such as SOC 2®, ISO 27001, and others within a single interface. Hyperproof’s automated workflows streamline repetitive tasks, reducing manual effort and ensuring processes align with compliance timelines.
One of Hyperproof’s key strengths is its ability to connect controls and evidence directly to audit requests, simplifying the preparation process. Teams can map specific documentation or data to corresponding requirements, ensuring nothing is overlooked during submissions. Additionally, Hyperproof enables assigning evidence requests to team members with clear accountability, so individuals know their responsibilities and deadlines, fostering collaboration across departments. This feature minimizes delays and keeps everyone on the same page.
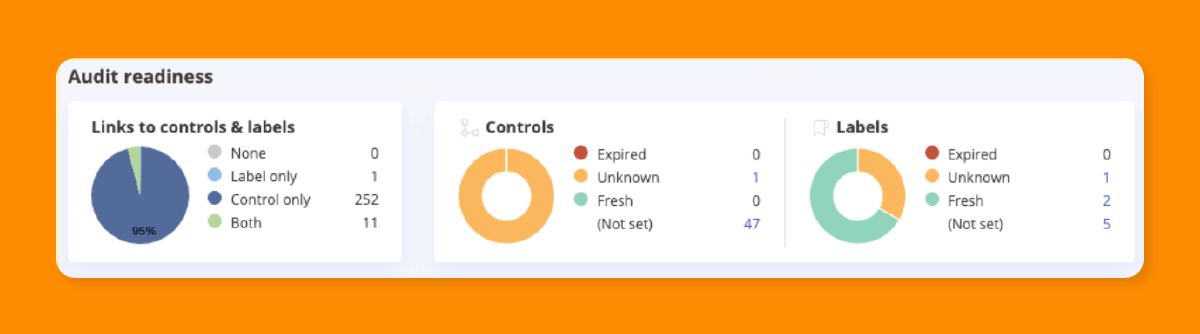
Another significant benefit is Hyperproof’s capacity to track progress and audit-readiness in real-time. Compliance managers can monitor completion rates, identify gaps, and address issues before they escalate, ensuring a smoother audit experience. By integrating a tool like Hyperproof, organizations gain efficiency, improve visibility into compliance status, and reduce the risk of errors, creating a scalable foundation for managing complex audit demands. This approach not only saves time but also enhances the accuracy and reliability of compliance efforts across multiple frameworks.
How does working with your auditor in a shared audit space help the audit process?
Working with auditors in a shared digital environment like Hyperproof offers substantial advantages for cybersecurity and GRC programs. Hyperproof eliminates the need to respond to a Document Request List (DRL) through traditional methods such as emailing or uploading evidence, which often leads to version-control issues and unnecessary communication delays. Instead, Hyperproof provides a centralized space where evidence can be directly shared and reviewed, streamlining interactions.
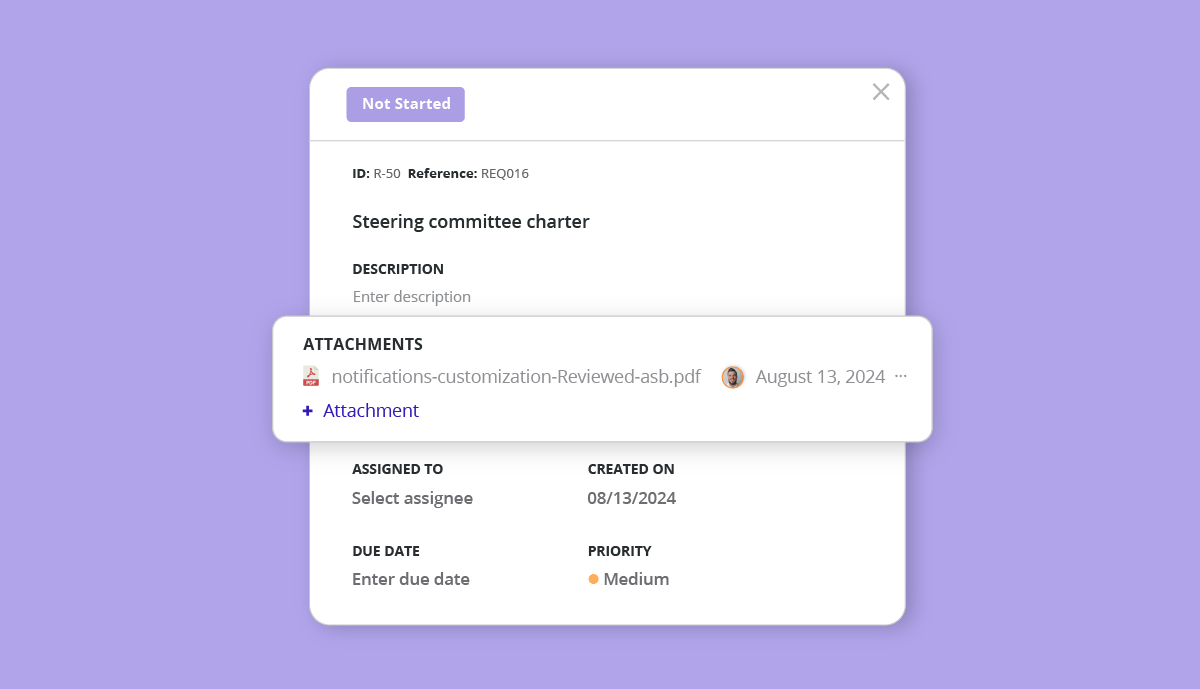
This setup cuts down on administrative overhead and helps maintain focus on substantive compliance matters rather than logistical hurdles. Hyperproof further enhances transparency by allowing organizations and auditors to better track the status of the audit. Teams can see which requests are pending, in progress, or completed, providing clarity on where attention is needed.
Creating a shared audit space requires setting clear access permissions to protect sensitive information while ensuring auditors have what they need. Training both internal teams and external auditors on the platform’s features can also help maximize its benefits. This collaborative approach fosters trust, as auditors can verify evidence promptly and organizations can address queries efficiently.
By using Hyperproof for auditor interactions, companies improve response times, minimize misunderstandings, and create a more organized audit process, ultimately strengthening compliance outcomes and professional relationships with audit partners.
What integration strategies connect GRC platforms with existing systems?
Connecting Hyperproof with existing enterprise systems is a vital step for seamless evidence collection in cybersecurity and GRC initiatives. Integrating with Information Technology Service Management (ITSM), Security Information and Event Management (SIEM), and other critical tools ensures automated data flows, reducing manual input and enhancing the accuracy of compliance documentation. This strategy supports efficient audit preparation by pulling relevant information directly from operational systems.
ITSM platforms, like Jira, often house incident tickets and change management records that serve as evidence for controls in frameworks like SOC 2® or ISO 27001. Linking Hyperproof to ITSM systems allows automatic extraction of these records, ensuring they are current and aligned with audit needs. Similarly, SIEM solutions like Splunk aggregate security logs and alerts crucial for demonstrating threat detection and response capabilities. Integrating these with Hyperproof enables continuous evidence updates without manual uploads, saving time and reducing errors.
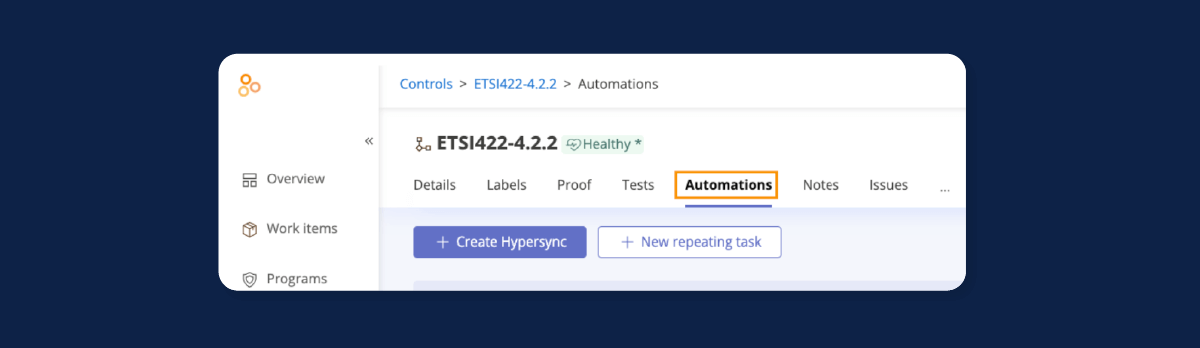
Successful integration requires mapping data fields between systems to ensure compatibility, setting up secure APIs for data transfer, and establishing schedules for regular synchronization to keep evidence fresh. Organizations must also prioritize security during integration, using encryption and access controls to safeguard sensitive information. Testing connections before full deployment helps identify and resolve potential issues. By using Hyperproof with existing tools, companies create a cohesive ecosystem for compliance data, improve audit readiness, and allow teams to focus on analysis rather than collection, thereby strengthening overall compliance management with minimal disruption to current operations.
How does performance monitoring and continuous improvement affect audit management?
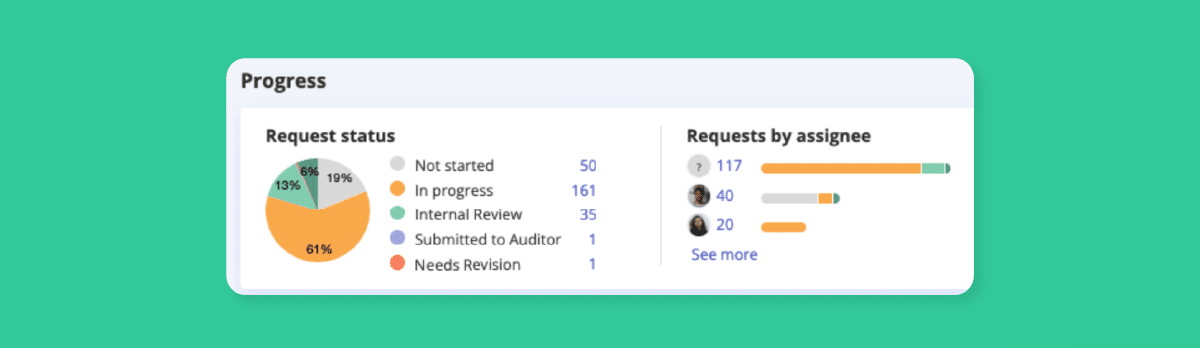
Monitoring performance in audit management is essential for optimizing processes in the GRC programs. This is typically achieved by defining key performance indicators (KPIs) to provide measurable insights into how well an organization prepares for and executes audits. Tracking metrics such as preparation-time reduction and evidence-delivery speed scores helps identify areas of success and opportunities for enhancement.
Preparation-time reduction measures the duration of pre-audit activities like control mapping and evidence gathering for standards such as SOC 2® or ISO 27001. A decrease in this metric indicates improved efficiency through tools or streamlined workflows.
Evidence-delivery speed tracks how quickly teams provide requested documentation to auditors, reflecting the effectiveness of internal coordination and system integrations.
Establishing these KPIs requires defining clear benchmarks based on past audit data and industry standards, then regularly reviewing them through dashboards or reports. By focusing on these metrics, organizations can pinpoint bottlenecks such as slow evidence retrieval and implement targeted fixes like automation or training. Consistently measuring performance ensures audits become more predictable and less resource-intensive, strengthening compliance programs and building confidence in meeting the demands of modern audits.
What steps should be part of post-audit review processes?
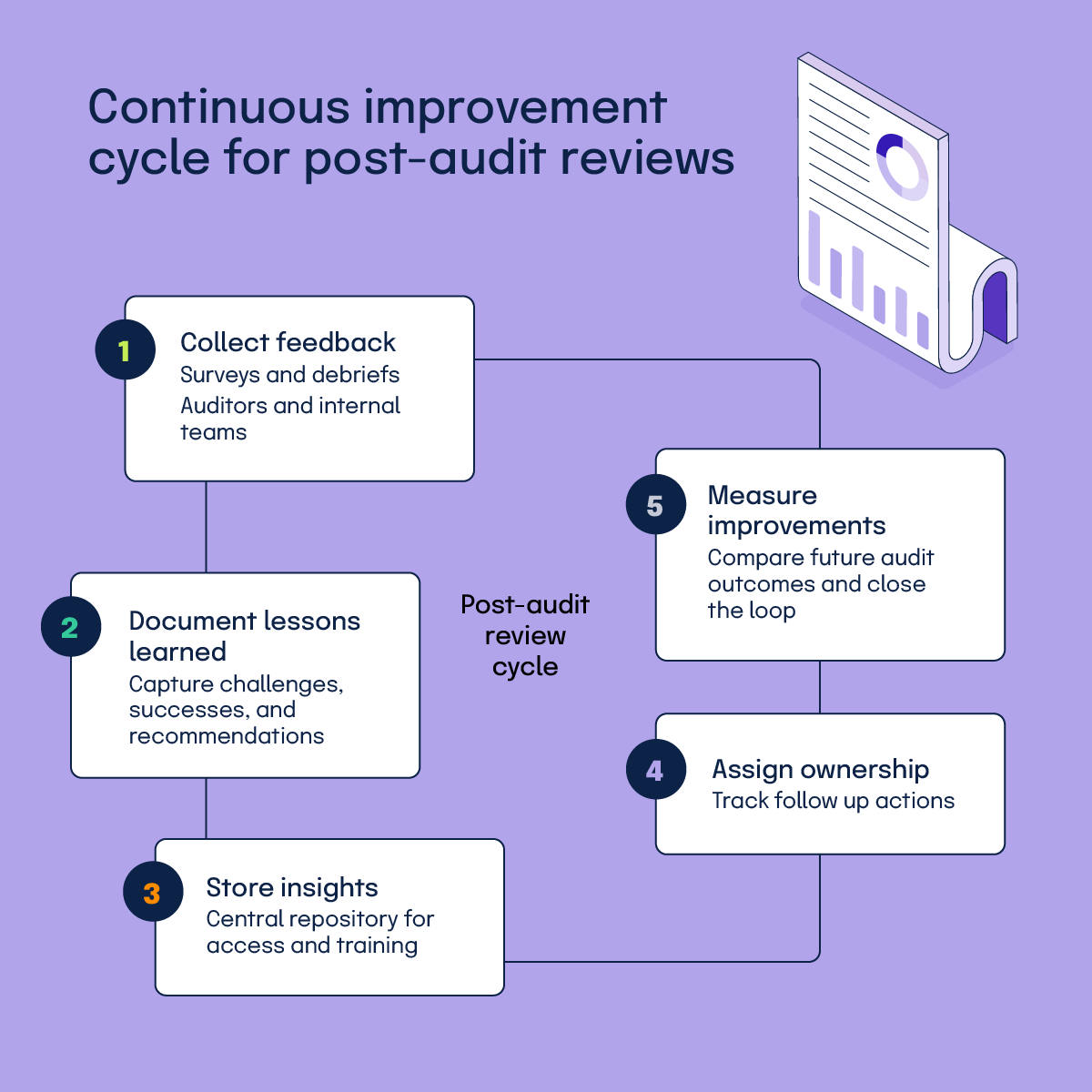
Implementing a systematic post-audit review process is a cornerstone of continuous improvement in cybersecurity and GRC programs. These reviews focus on collecting feedback and documenting lessons learned to refine future audit cycles. By formalizing this approach, organizations can address gaps, enhance efficiency, and ensure the compliance with frameworks such as SOC 2® or ISO 27001 remains a repeatable, well-structured process.
Immediately after an audit concludes, teams should gather feedback from internal stakeholders and auditors through structured surveys or debrief meetings. This feedback captures insights on what worked well, like timely evidence submission, and what caused friction, like unclear control narratives. Documenting lessons learned involves creating a detailed report that outlines specific challenges, successful strategies, and actionable recommendations for improvement. For instance, if missing evidence delayed responses, the report might suggest pre-audit validation checks.
Storing these insights in a centralized repository and assigning ownership for follow-up actions helps ensure they remain accessible for future reference, training, and accountability, allowing teams to track whether changes yield better outcomes over time.
How can ROI measurement and optimization be applied to audit initiatives?
Quantifying the return on investment (ROI) for audit-management initiatives is vital for justifying the resources allocated to cybersecurity and GRC programs. Measuring benefits such as the reduction in preparation time and the decrease in evidence-collection cycles provides a clear picture of the value gained from tools, processes, or training. This approach enables organizations to optimize their compliance efforts while aligning with standards such as SOC 2 or ISO 27001.
The reduction in preparation time reflects how much faster teams can ready themselves for audits through automation or streamlined workflows. For example, if the average preparation window fell from 30 days to 18 days and the blended hourly rate is $75, the time saved equals 12 days x 8 hours x $75 = $7,200 per audit.
Calculating the benefit involves comparing time spent before and after implementing new methods, then estimating cost savings based on labor hours. Similarly, the decrease in evidence-collection cycles measures how many fewer rounds of requests or revisions occur during an audit. Fewer cycles often result from better organization or system integrations, directly translating to less auditor downtime and lower operational costs.
To optimize the ROI, organizations should regularly assess the metrics against the initial investment costs, such as software subscriptions or staff-training expenses. Adjustments might include refining tool usage or targeting specific bottlenecks identified in the data. Documenting both tangible savings and intangible gains, such as improved customer trust, provides a fuller view of the impact.
Key takeaways
Effectively managing multiple audits hinges on strategic planning, clear prioritization, and the smart use of technology. By mapping overlapping controls, organizations can cut the duplicate work and free up valuable resources. Building capacity buffers and dynamic teams prevents burnout while ensuring critical audits receive the attention they deserve.
Centralized evidence repositories and automated collection streamline the preparation, reduce errors, and accelerate response times. Continuous performance monitoring and post-audit reviews turn each engagement into a learning opportunity, driving ongoing improvement. When these practices are combined, organizations not only lower costs and risk but also strengthen their overall security posture and compliance confidence.
See Hyperproof in Action
Related Resources
Ready to see
Hyperproof in action?