NIST 800-171 Compliance Made Easy: Your Ultimate Checklist
If you’ve ever spent a weekend buried in control mappings or trying to match your policies to NIST 800-171, you know it’s a slog. Half the battle is figuring out what “adequate security” actually means in practice. The other half is keeping it all documented, repeatable, and audit-ready without losing your mind.
NIST 800-171 revision 3, released in May 2024, made things even trickier. It cut the total requirements from 110 to 97, but expanded the assessment objectives from roughly 320 to 422. The granularity and depth of evidence needed have increased. In turn, being “compliant on paper” is harder. It’s not a bad thing, just more work if you don’t have a structured plan.
If you are looking for a straight path to NIST 800-171 compliance, we’ve invested resources in preparing a comprehensive checklist you can use (with a downloadable version as well). It’s shaped by what we’ve seen work across different environments. But before everything, here’s a quick overview of NIST 800-171.
Related: The Ultimate Guide to NIST SP 800-171
NIST 800-171 compliance definition and overview
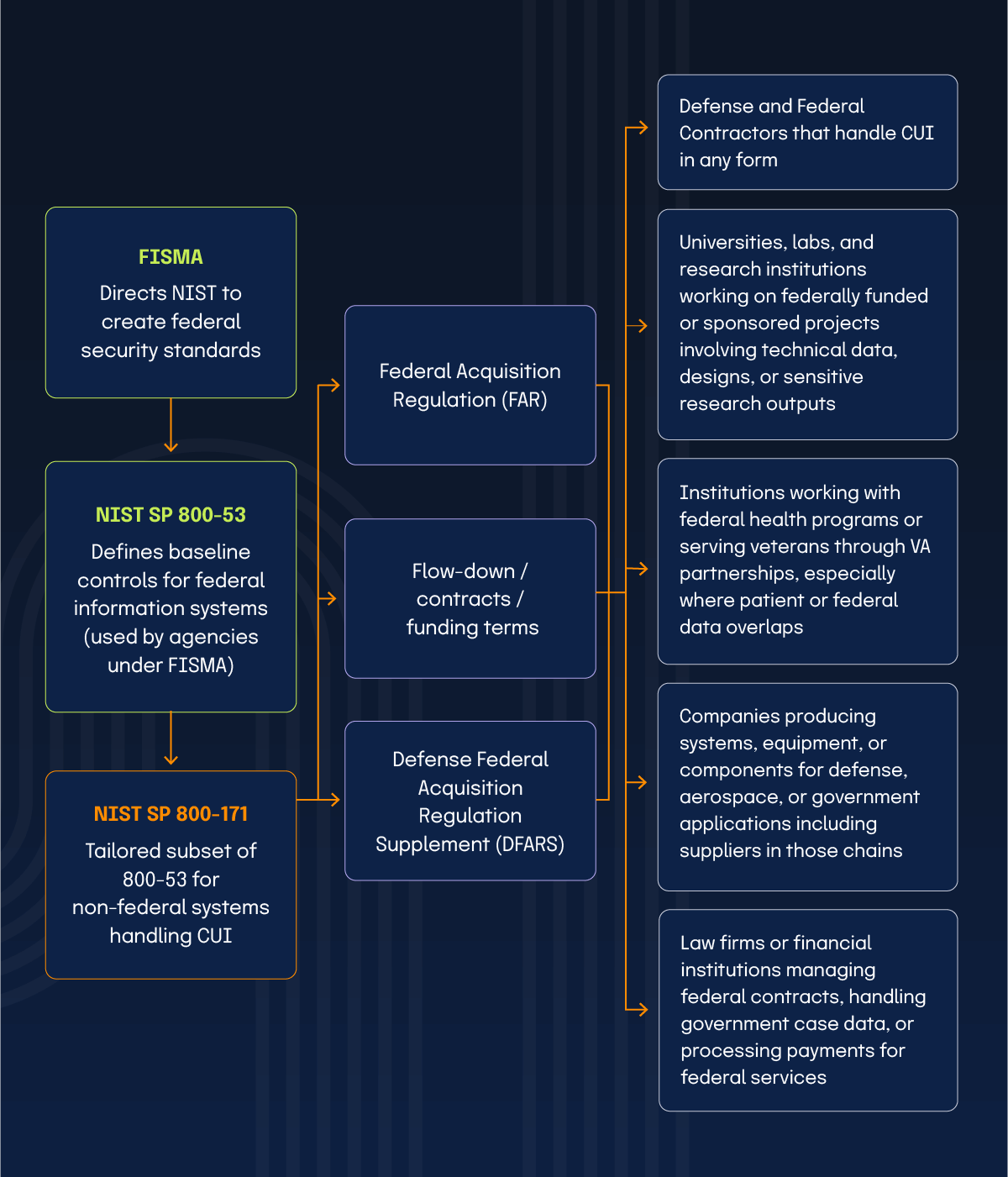
The National Institute of Standards and Technology Special Publication 800-171 (NIST 800-171) is the rulebook for anyone touching controlled unclassified information (CUI) on systems that the federal government doesn’t run. CUI, in plain terms, is the data that’s not classified but still sensitive. For example, contract data, research results, specs, anything a federal agency doesn’t want floating around the internet.If we zoom out, NIST 800-171 falls right inside the larger network of federal standards, built on NIST 800-53 and Defense Federal Acquisition Regulation Supplement (DFARS), and often crossing paths with HIPAA and GDPR when federal data comes into play.
The rulebook breaks everything into 17 control families, each one covering a different part of security, like access, configuration, system protection, monitoring, and documentation. The families are listed as follows:
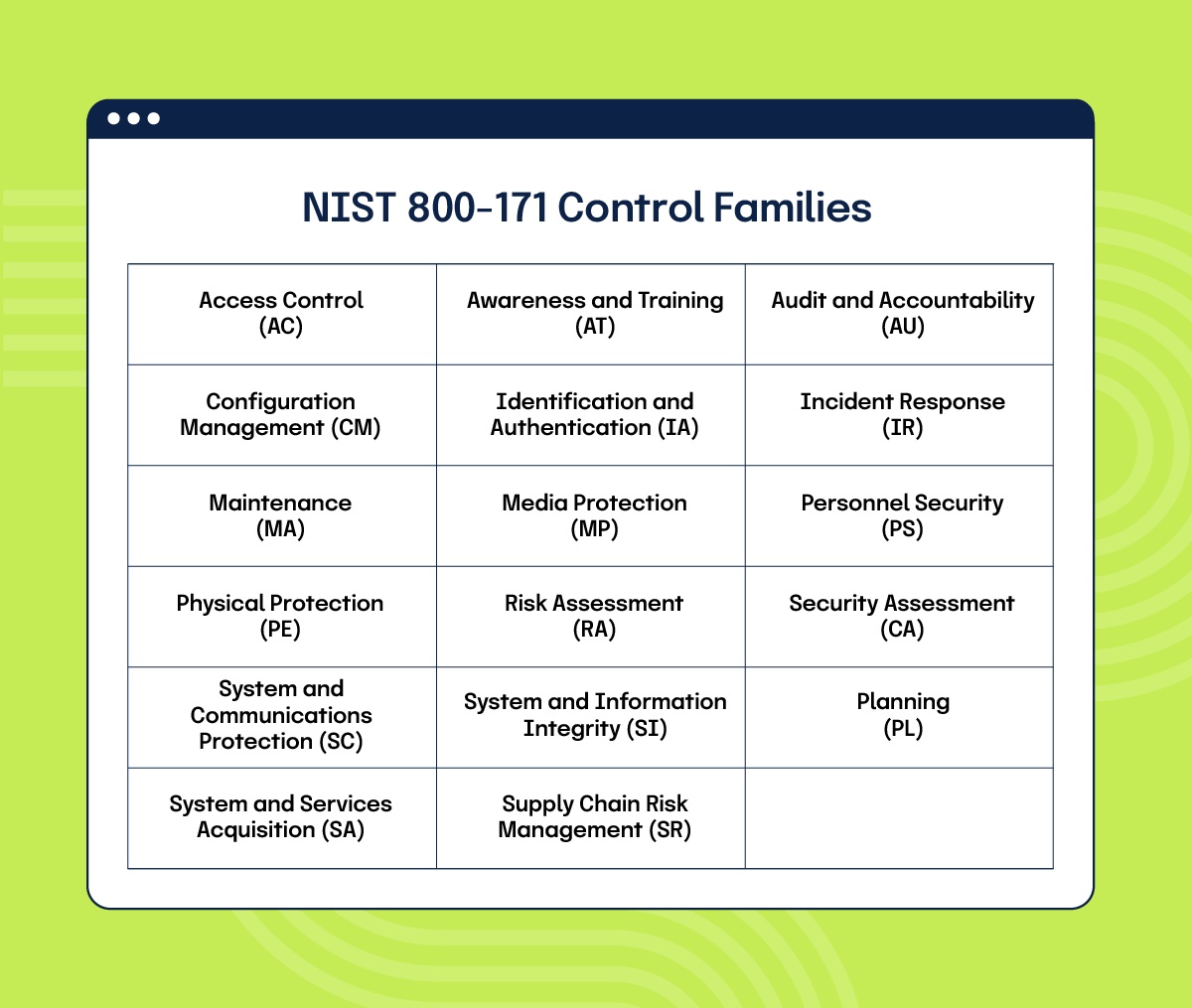
Together, these control families outline how to handle, store, and safeguard CUI across your network and your vendors. Our checklist is built around these 17 families, and it breaks down each area into clear, actionable steps you can actually measure and track.
NIST 800-171 compliance checklist: items by control families
To be considered compliant, you must implement all 97 security controls from NIST SP 800-171 Revision 3. Each control contains specific assessment objectives, a total of 422, that define how compliance is measured.
You cannot skip or simplify any control. Every objective must be addressed or backed by a documented compensating control.
The following structured checklist is meant to help you understand how to approach, review, and document each area in a practical way (do not treat the checklist as legal or compliance advice).
Once you have completed the checklist and documented your control status, the next step is putting it all into motion. In the following section, we’ll walk through the key steps to actually achieve and maintain NIST 800-171 compliance.
As promised earlier, here’s a downloadable version of that checklist you can use to get compliant fast.
Get the NIST 800-171 Compliance Checklist now!
Steps to achieve NIST 800-171 compliance
Most organizations understand what the NIST 800-171 controls are, but putting them into action is where things usually fall apart. The standard demands consistent documentation, ongoing monitoring, and evidence that matches what’s written in your plan.
The steps below break that work into focused phases that help you close control gaps, capture usable proof, and stay aligned with the expectations in Revision 3 without spinning in circles.

1. Define your CUI environment and boundaries
Map where CUI lives and moves. List systems, users, and vendors in scope. Decide if you’ll isolate CUI in an enclave or keep it within shared infrastructure. This boundary drives everything else.
2. Run a full gap analysis against NIST 800-171 Rev 3
Work through all 17 families and the assessment procedures. Mark implemented, partial, and missing. Note where proof will live: configs, logs, tickets, or policies. This becomes the base for your SSP and POA&M.
3. Build and maintain your SSP and POA&M
Document how each control is implemented and link it to real evidence. You can use Hyperproof’s out-of-the-box NIST SP 800-171 program template to stand up the structure fast, then generate SSP reports from the data you maintain inside the workspace. Owners, due dates, and version history stay attached to each item, so you are not chasing files later.
4. Validate encryption and cryptographic controls
Confirm that encryption protecting CUI uses validated modules. Replace anything that is unvalidated or expired. Keep module details and dates where an assessor can find them.
5. Confirm cloud providers meet a federal baseline or equivalent
If CUI touches the cloud, keep the provider’s security mappings and inherited control details in your evidence set. Make sure your boundary and shared-responsibility lines are clear.
6. Implement high-risk controls first
Tighten access, authentication, logging, and network protection before lower-risk items. Capture proof as you go so the audit trail builds itself.
7. Complete your self-assessment and post to SPRS (if DoD)
Score your implementation against 800-171. If DFARS applies, post your score and target date in SPRS. Keep the scoring notes tied to control records.
8. Prepare for CMMC Level 2 or other third-party reviews
If your contracts require it, line up the same 800-171 evidence for independent assessment. Keep your SSP, POA&M, and artifacts current to avoid rework.
9. Send requirements to vendors and partners
Push the same expectations to suppliers and service providers that touch your CUI. Track attestations and remediation tasks until they close.
10. Keep evidence fresh with Hyperproof
Turn on automated evidence collection with our integrations, assign review cycles, and use dashboards to see what is current and what is drifting. Continuous monitoring and workflow keep you ready for audits without a scramble.
Once the controls are in place, the real work is keeping them current and adapting as requirements evolve. You can make this process far more manageable with structured workflows, automation, and digital solutions that reduce manual tracking and keep everything tied to evidence. Talking of digital solutions, Hyperproof can help you in a number of ways to speed up your NIST 800-171 compliance efforts.
How can Hyperproof help with NIST 800-171 compliance?
Getting through NIST 800-171 on spreadsheets and shared drives works for a few weeks, then falls apart. Controls drift, evidence expires, and ownership gets lost. That’s why teams move their compliance operations into purpose-built systems that can track, prove, and maintain controls with less manual effort. Hyperproof was built around that exact need.
Below are the ways teams use it day to day to stay aligned with NIST 800-171 without starting from scratch.
Start fast with a pre-built NIST 800-171 program template
Instead of creating mappings and control records manually, you can start with a ready-to-use NIST 800-171 template that already includes all 17 families and 97 controls. Each control comes with linked tasks, responsible roles, and evidence placeholders.
You can import your existing documentation and customize the structure to match your environment. It saves weeks of setup and keeps your control language aligned with official guidance.

Manage evidence and audits in one place
Collecting proof of compliance is often the most painful part of this framework. In Hyperproof, every control has an evidence folder where you can attach configurations, screenshots, reports, or attestations. You can assign owners, set review dates, and see when evidence expires.
During an internal or third-party audit, the reviewer can verify everything directly in the system instead of chasing files or email threads. This makes both SSP maintenance and external validation faster and more defensible.
Automate monitoring and status tracking
Compliance requires continuous attention. Hyperproof lets you schedule recurring reviews, automate reminders, and pull real-time data from connected systems like identity management, cloud infrastructure, and ticketing tools. You can see which controls are compliant, which are overdue for review, and what evidence is missing.
That visibility turns compliance from a once-a-year scramble into a routine workflow that keeps your program stable.
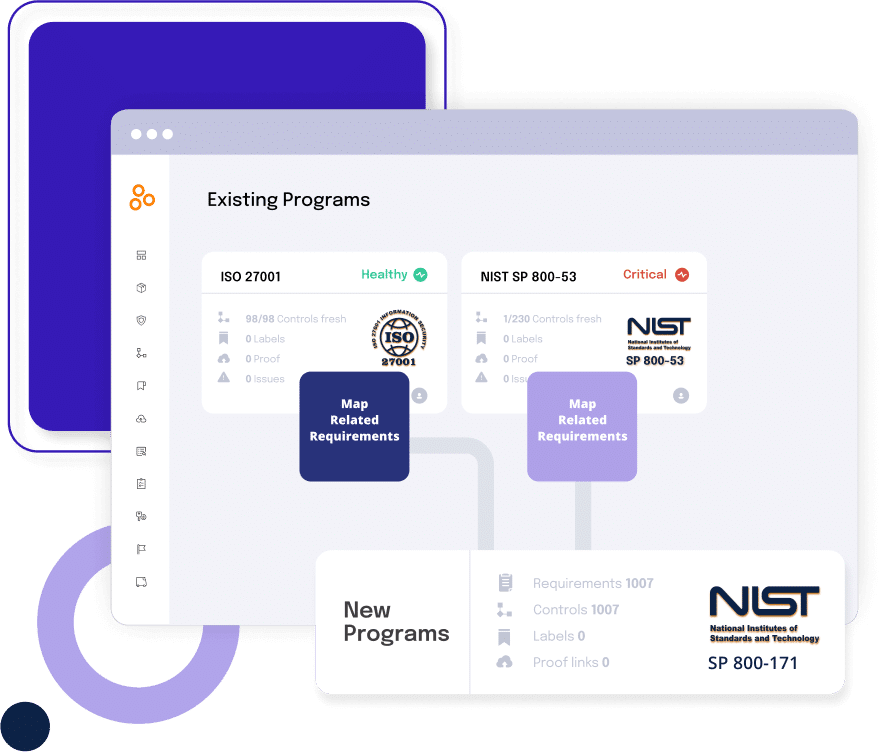
Map NIST 800-171 controls to CMMC and other frameworks
Hyperproof allows cross-mapping of controls across multiple frameworks, so you only maintain one version of each control and apply to other relevant frameworks and programs. This reduces duplicate work when you expand into CMMC Level 2, ISO 27001, or other federal requirements. You can trace a single piece of evidence to every related control and update once instead of repeating it across different frameworks.
If we were to sum it up: Hyperproof does not change what NIST 800-171 requires, but it changes how the work gets done. The platform gives teams a single place to plan, execute, and prove compliance without losing track of who owns what or where the evidence lives.
Use NIST 800-171 as your foundation for CMMC
CMMC was created to make sure that every contractor handling Controlled Unclassified Information can prove their security posture instead of just stating it. It builds directly on NIST 800-171 but adds structure around validation, scoring, and accountability. For most organizations, that means the controls don’t change much, but the expectation for proof does.
If your NIST 800-171 program already runs cleanly, you’re well-positioned. The same 97 controls feed directly into CMMC Level 2, but the bar for evidence and repeatability is higher. What matters now is showing that each control isn’t just written but practiced and reviewed. Keeping ownership clear, automating evidence refresh, and tracking corrective work consistently are what turn a NIST 800-171 implementation into a CMMC-ready operation.
To learn more about how exactly Hyperproof.io can help, book a demo with us.
See Hyperproof in Action
Related Resources
Ready to see
Hyperproof in action?