The Ultimate Guide to Cloud Architecture Maturity: A Practical Guide to Risk Mitigation and Compliance
Today, many organizations are expanding their cloud footprint across AWS, Azure, and Google Cloud, only to find that the breakneck speed of innovation often outpaces the ability to remain compliant. Cloud architecture maturity is more critical today than ever. With global cybercrime costs projected to rise and the complexity of multi-cloud environments increasing, managing cloud risk is no longer a “once-a-year” project—it is a challenging, ongoing, and iterative process.
Despite the advantages of cloud scale, achieving a mature, audit-ready posture can be a struggle for compliance managers. However, by leveraging Well-Architected Frameworks as an operational “north star,” organizations can bridge the gap between engineering best practices and rigorous audit requirements.
This guide explores how to move your cloud program from ad hoc configurations to a continuous compliance lifecycle.
What is cloud architecture maturity?
Cloud architecture maturity is not defined by the complexity of your technical stack, but by the repeatability and verifiability of your practices. It represents the evolution from heroic manual efforts—where a few key engineers keep the system running—to automated, policy-driven governance.
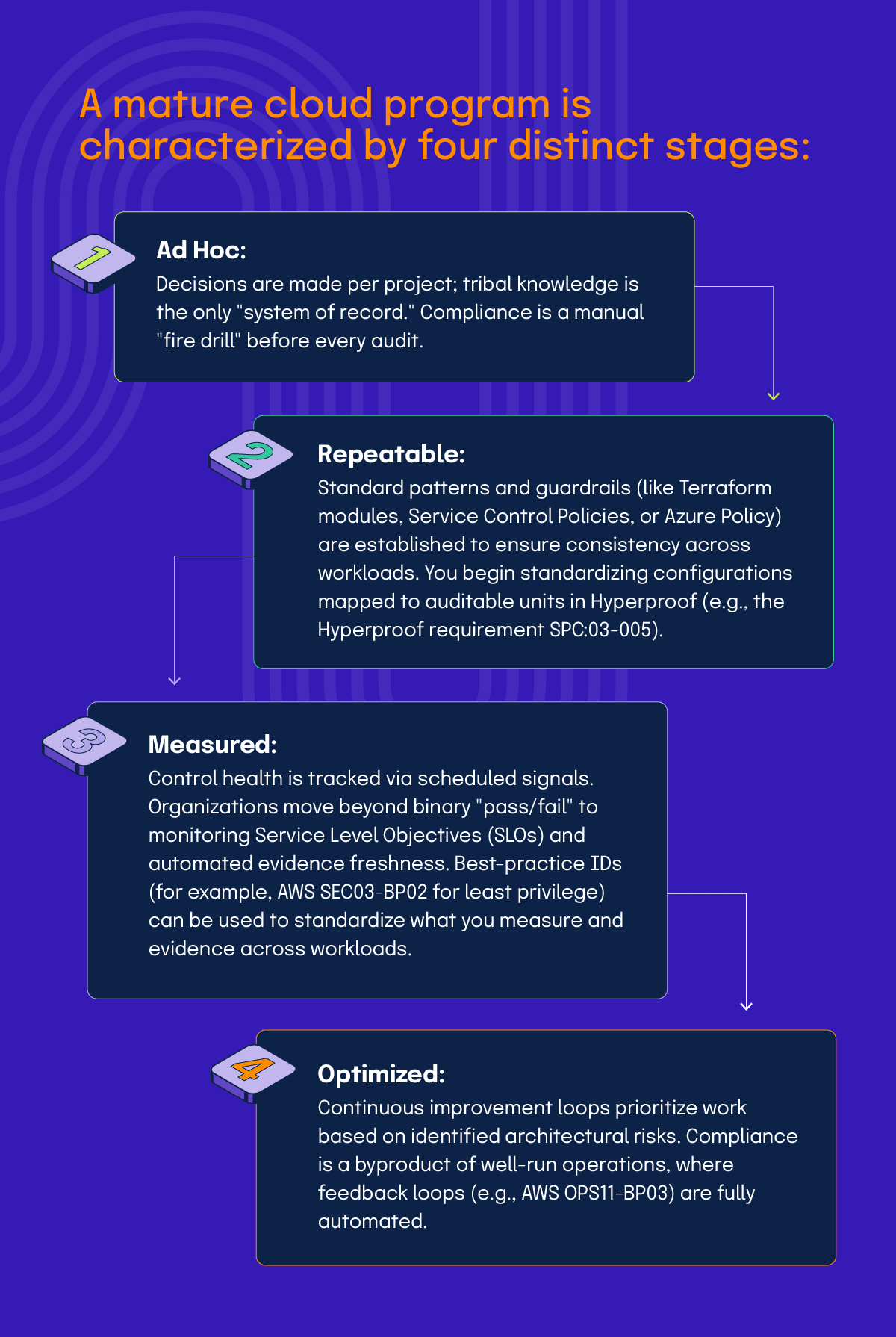
A mature cloud program is characterized by four distinct stages:
- Ad Hoc: Decisions are made per project; tribal knowledge is the only “system of record.” Compliance is a manual “fire drill” before every audit.
- Repeatable: Standard patterns and guardrails (like Terraform modules, Service Control Policies, or Azure Policy) are established to ensure consistency across workloads. You begin standardizing configurations mapped to auditable units in Hyperproof (e.g., the Hyperproof requirement SPC:03-005).
- Measured: Control health is tracked via scheduled signals. Organizations move beyond binary “pass/fail” to monitoring Service Level Objectives (SLOs) and automated evidence freshness. Best-practice IDs (for example, AWS SEC03-BP02 for least privilege) can be used to standardize what you measure and evidence across workloads.
- Optimized: Continuous improvement loops prioritize work based on identified architectural risks. Compliance is a byproduct of well-run operations, where feedback loops (e.g., AWS OPS11-BP03) are fully automated.
Note: This guide utilizes both native cloud provider IDs (e.g., AWS SEC03-BP02) and proprietary Hyperproof requirement IDs (e.g., Azure RE:01-007, Google SPC:03-005). While AWS IDs are public and verifiable, the Azure and Google IDs referenced here represent Hyperproof’s internal mapping of architectural best practices to auditable work units.
The role of Well-Architected Frameworks
Major cloud providers offer Well-Architected Frameworks to codify “the questions worth asking.” These are effectively the customer-facing versions of the internal architecture review processes the providers use themselves. In practice, a Well-Architected Framework becomes the “architecture operating cadence” that compliance programs anchor to: Review → Backlog → Evidence → Re-review.
Provider-specific nuances
While the intent of every Well-Architected Framework is to build secure, high-performing systems, each provider approaches their structure through a slightly different lens:
The shared responsibility model in audits
One of the most common cloud audit pitfalls is mis-scoping responsibilities. The Shared Responsibility Model dictates that the provider secures the “of” the cloud (physical data centers, network hardware, hypervisors), while you secure the “in” the cloud (data, identities, configurations).
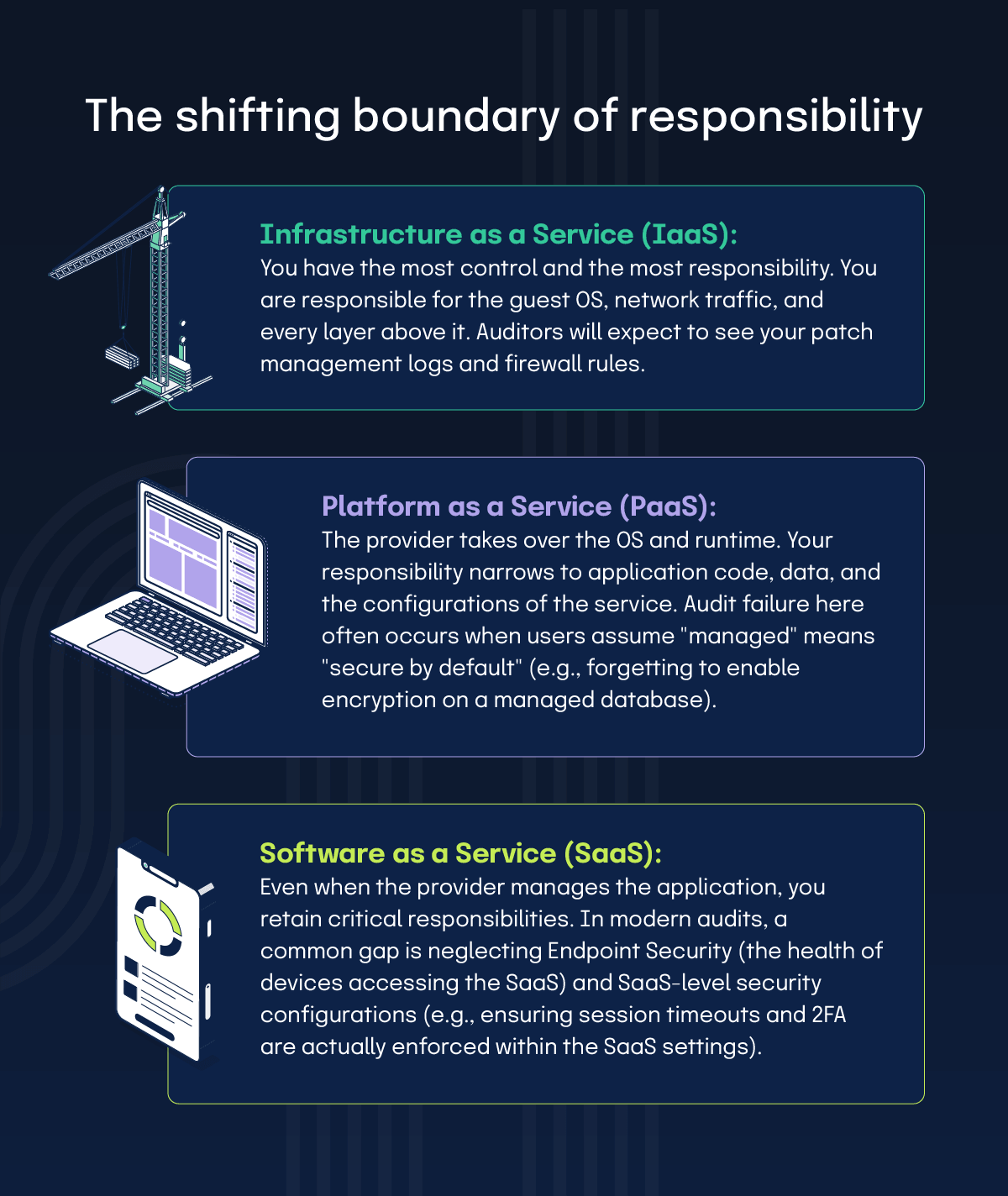
The shifting boundary of responsibility
The configuration gap
The most dangerous area in any cloud audit is the Configuration Layer. This is where the provider gives you the capability to be secure, but if you don’t use it, you inherit the risk. This commonly creates a gap—where a cloud provider’s SOC 2Ⓡ report covers the infrastructure, but your lack of configuration evidence creates a hole in your own compliance posture.
Mapping architecture to SOC 2Ⓡ, ISO 27001, and CSA CCM
Well-Architected guidance tells you how to design and operate, while frameworks like ISO 27001 or SOC 2Ⓡ tell you what outcomes you must evidence.
The Cloud Control Hub: CSA CCM
For organizations looking for a cloud-focused control framework for cross-framework alignment, the Cloud Security Alliance (CSA) Cloud Controls Matrix (CCM) is a widely used standard. CCM v4.1 spans 17 domains and 207 controls, with cross-framework mappings for standards such as ISO/IEC 27001/27002:2022, NIST CSF 2.0, PCI DSS v4.0, and CIS v8.
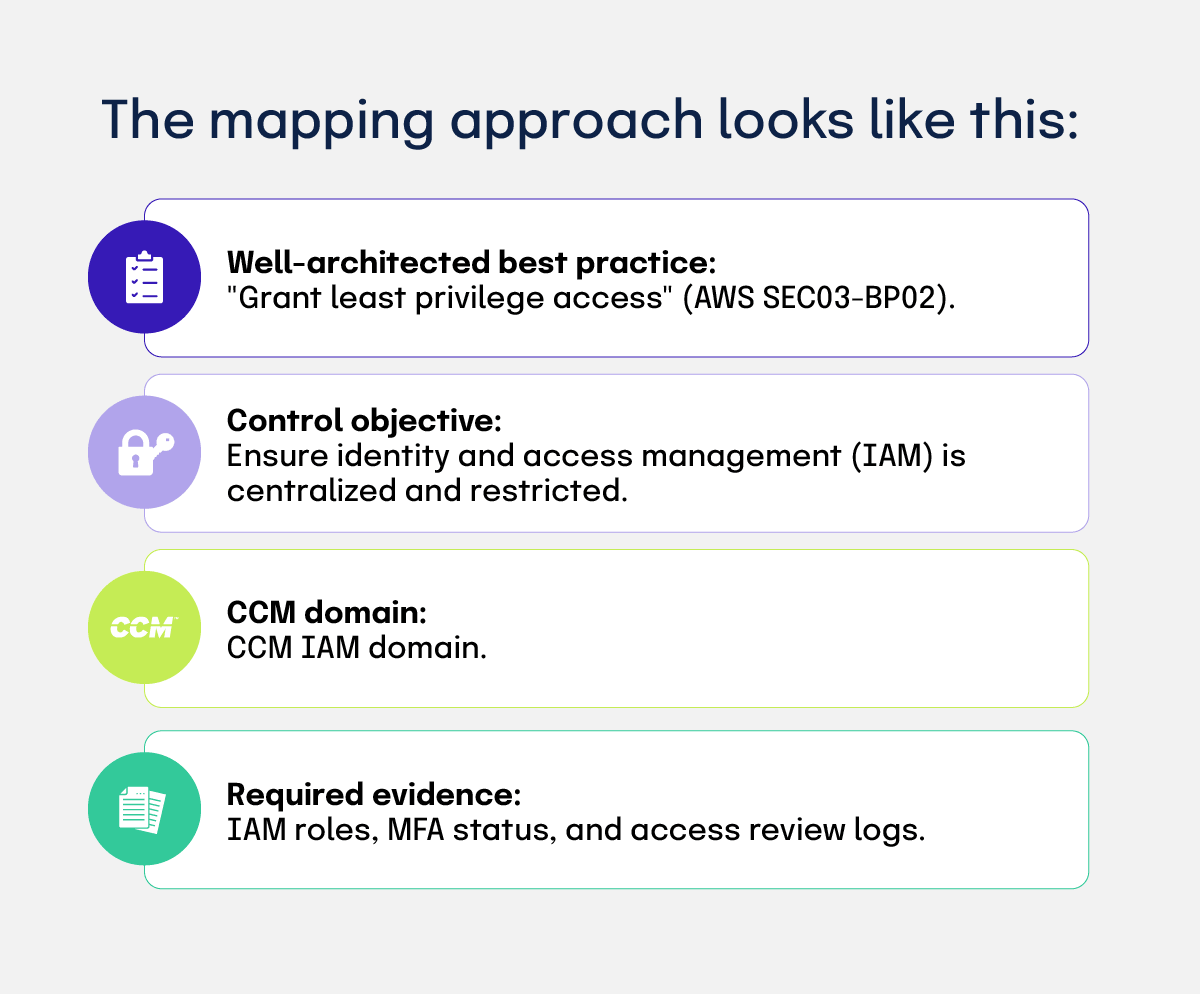
The mapping approach looks like this:
By mapping Well-Architected pillars into CCM domains, you can implement a technical check once and reuse that evidence across multiple compliance programs.
How Hyperproof operationalizes cloud maturity
Hyperproof transforms Well-Architected guidance from a static document into an auditable, living operating system. It provides the line of sight from architecture maturity to risk reduction.
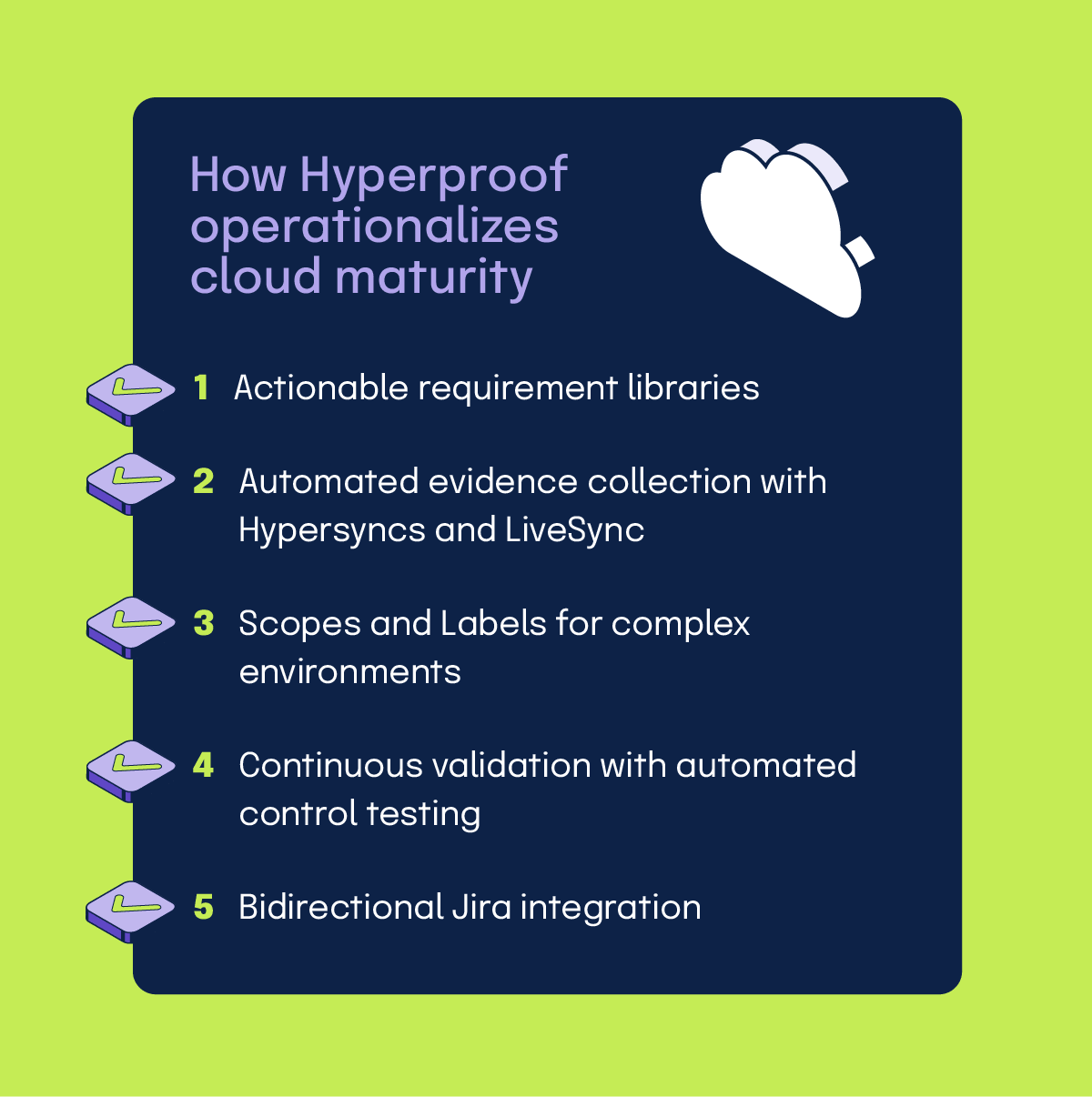
1. Actionable requirement libraries
Hyperproof breaks down high-level pillars into granular, platform-specific requirements drawn directly from AWS, Google, and Azure technical and help documentation. Instead of vague advice, Hyperproof provides thousands of auditable work units—such as AWS SEC02-BP01 (Strong sign-in mechanisms), Hyperproof requirement RE:03-001 (Failure Mode Analysis), or Hyperproof requirement RL:07-004 (Simulating realistic failures).
2. Automated evidence collection with Hypersyncs and LiveSync
Manual screenshots are the primary enemy of maturity.
3. Scopes and Labels for complex environments
Hyperproof supports Scopes to partition work by environment (e.g., Prod vs. Staging). This prevents “prod-ready” evidence from masking gaps in other accounts. Labels allow you to collect proof once (like centralized logging configurations) and link it to every requirement it satisfies, drastically reducing duplicate work.
4. Continuous validation with automated control testing
Hyperproof supports automated control tests against proof collected by Hypersyncs. When a control test fails, you can automatically generate (repeating) remediation tasks tied to the failure, so owners have a tracked workflow rather than relying on screenshots or ad-hoc follow-up. These tests update the Control Health status to At risk or Critical.
5. Bidirectional Jira integration
Compliance work must flow where engineering work happens. The Jira integration is bidirectional for Jira issues ↔ Hyperproof tasks (Jira→Hyperproof sync runs every ~5 minutes; Hyperproof→Jira syncs immediately). Proof attached in Jira can be pulled into Hyperproof, but not the reverse.
Your cloud maturity roadmap
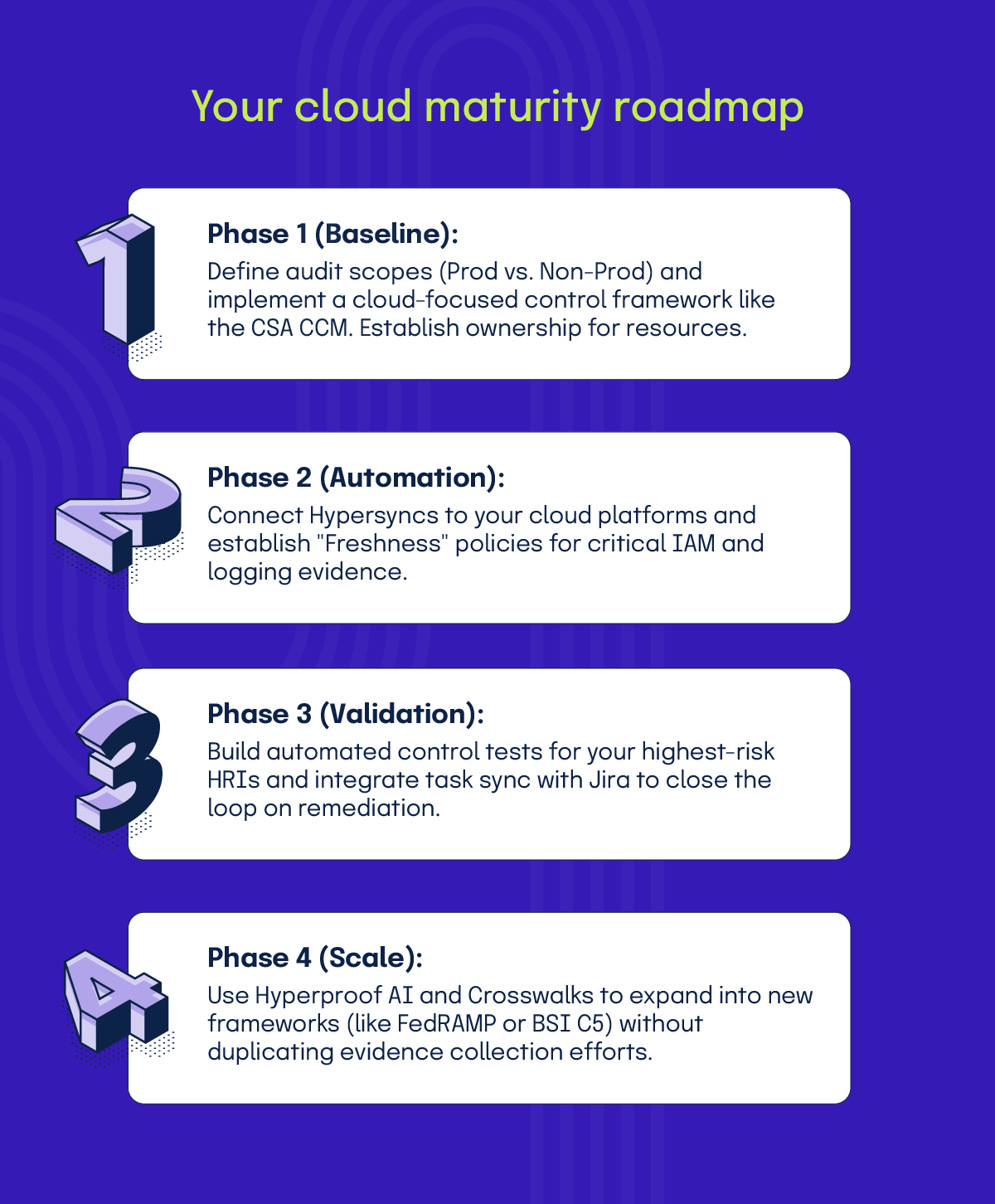
Achieving architecture maturity is a journey, not a sprint. We recommend a phased approach:
Cloud Compliance: Frequently Asked Questions
Does a Well-Architected Review count as a SOC 2Ⓡ audit?
No. A review using a Well-Architected Framework is a self-assessment or consultant-led review of risk. A SOC 2Ⓡ audit is an independent attestation. However, the output of a review tool is excellent governance evidence to show auditors that you have a formal process for identifying, prioritizing, and remediating architectural risks.
Can I use a Well-Architected Review as “audit evidence” for specific controls?
It is best treated as risk management or control governance evidence (e.g., “we have a formal review process, we identify risks, and we track remediation”). It is not proof that a specific control (like MFA) operated effectively at a point in time. For that, you need technical “operation evidence” such as logs and configs, which Hyperproof collects via Hypersyncs.
What is the difference between “Freshness” and “Control Health”?
How do ISO 27017 and ISO 27018 fit into the Well-Architected story?
These standards “thicken” the Security pillar. ISO/IEC 27017:2015 adds cloud-specific security control guidance, while ISO/IEC 27018:2025 focuses on protecting PII in public clouds. They help translate “general security” into “cloud-appropriate security.”
What is CAIQ and when should I use it instead of the CSA CCM?
The CAIQ (Consensus Assessments Initiative Questionnaire) is the assessment version of the CCM. CAIQ v4.1 includes 283 questions aligned with the latest controls. Use the CCM when you are building your internal control framework, and use the CAIQ when you need a repeatable format for assessing vendors.
How do I explain “cloud architecture maturity” to executives?
Define it as moving from ad hoc heroics to repeatable, evidenced, and continuously validated practices. A mature program produces clear ownership, measurable risk reduction, and “always-current” audit evidence, which mirrors the improvement lifecycle found in a Well-Architected Framework (identify risk → prioritize → implement → track).
What is the highest-leverage “control evidence” in cloud environments?
Auditors consistently prioritize Identity & Access evidence (least privilege, MFA, access reviews), logging & monitoring, change management, and incident response testing. These support multiple frameworks simultaneously (SOC 2Ⓡ, ISO 27001, CSA CCM).
How do I operationalize “continuous compliance” so it’s real and not just marketing?
Treat cloud controls like software: automate evidence collection via Hypersyncs, continuously test configurations with automated testing, and use a remediation workflow (like Hyperproof’s Jira integration) when checks fail. Continuous validation is the missing piece of the compliance puzzle.
Operationalizing Well-Architected Frameworks through Hyperproof
Maturing your cloud architecture is about more than just checking a box for an auditor—it is about building a resilient, efficient, and secure business foundation. By aligning your cloud operations with Well-Architected Frameworks and operationalizing those practices through Hyperproof, you move from “audit readiness as a fire drill” to audit readiness as a byproduct of excellence.
Hyperproof makes cloud maturity easy.
Case study: Continuous compliance at scale
See how Appian streamlines GRC and saves $100K per audit with Hyperproof

See Hyperproof in Action
Related Resources
Ready to see
Hyperproof in action?