Mastering Data Privacy: Your Guide to Compliance Programs
Editor’s note: Given the fast-changing nature of data privacy regulations and new data privacy challenges that have surfaced as a result of the COVID-19 pandemic, this article was updated with fresh information on March 31, 2020.
Additionally, to help organizations stay compliant with disparate data privacy regulations during the coronavirus crisis, Hyperproof is offering our continuous compliance software subscription at no cost. You can learn more about this offer by heading to https://hyperproof.io/compliant-together
Why data privacy matters
But for a business to safely and successfully take advantage of the data they’re collecting, they need to have safeguards in place to ensure data is under tight lock and key and consumers aren’t subject to uninvited surveillance. In other words, if you’ve ever wondered what is data privacy and why is it an incredibly important asset, it’s the set of principles and controls that let you use data to grow the business while still respecting individuals’ rights, expectations, and legal protections.
As businesses collect growing amounts of information on their customers, those customers have begun to see the potential downsides to this data collection. Data privacy is more important today than ever before, and businesses should be highly concerned with their data privacy policies and procedures for a few different reasons.
At this time, the regulatory landscape has created new complications for businesses of all types. Data protection and privacy compliance obligations under laws such as the California Consumer Privacy Act (CCPA) and the EU’s General Data Protection Regulation (GDPR) have significantly impacted how businesses can collect, store, and handle personal information from consumers. These legislations are comprehensive and designed to provide a level of legal protection to covered consumers that were not previously available.
Additionally, the COVID-19 crisis has made data privacy issues even more salient. As organizations collect personal information about employees’ health and travel as part of their response to contain the spread of the virus, they need to take appropriate measures to protect employees’ privacy and stay compliant with applicable data privacy regulations, including EU’s General Data Protection Regulation (GDPR), the Americans With Disabilities Act (ADA), the California Consumer Privacy Act (CCPA), and the United State’s Health Insurance Portability and Accountability Act (HIPAA).
Meanwhile, businesses today are often at risk of unintentionally violating these data privacy regulations, because their security measures aren’t keeping up with the ever-evolving cyber risk landscape. Organizations are vulnerable to an increasing array of cyber attack schemes from cyber criminals, hackers and state-sponsored cyber terrorists. According to the Imperva 2019 Cyberthreat Defense Report, It’s expected that 57.6% of Government organizations, 73.5% of educational organizations, and 74.5% of retail organizations are at direct risk of suffering data breaches or compromises. In 2019, we saw organizations like Equifax, British Airways, Fortnite, Marriott Hotel Group pay settlements in the millions for data breaches.
As a business, your obligation to safeguard data has never been greater. Not only do you have to collect, store, process, and discard data in ways that are compliant with regulations, but you also need to have strong information security policies and practices that protect your clients’ data from malicious or unauthorized use.
In this guide, we’ll discuss why businesses need to pay attention to data privacy, the key data privacy regulations affecting U.S.-based businesses, and the key steps businesses need to take to adhere to these regulations and adequately protect their critical assets and their reputation.
Data privacy vs. data security
Data privacy is comprised of the policies and processes that dictate how your business collects, shares, and uses data. It is often informed by state or federal laws that apply to businesses in a certain location or industry.
On the other hand, data security protects your company’s data from being accessed or used maliciously. Data security is unique from one business to the next and will depend on the amount and types of data being collected and stored.
Both are crucial to a bulletproof data protection policy. Without both of them in place, you will have an incomplete program that leaves you vulnerable to attacks or costly mistakes.

Data privacy regulation types
Data collection regulations provide guidance for how and when businesses can collect data about consumers and, in some cases, whether people have to be notified that their data is being collected.
Data breach regulations tell businesses what they must do in the event of a data breach, such as notifying agencies and customers, tracking information about the breach, and taking steps to ensure a similar breach doesn’t happen in the future.
Data access regulations provide guidelines for 1) how internal access of information should be handled, and 2) the levels of access consumers are entitled to.
Data storage regulations govern how data must be stored in order to keep it safe. Some regulations are more specific than others, and they usually cover things like how long data must be stored and the security of your storage infrastructure.
Data privacy training regulations give guidance on who your business has to train on data privacy. Usually, this is something that every employee needs to be trained on in order to meet the regulations.
The data privacy landscape today
With the dramatic increase in the use of technology and remote work due to the COVID-19 pandemic, the past year has led to a lot of changes to the data privacy landscape. HR departments had to figure out how to strike a balance between protecting employees’ health (through collecting personal information for contact tracing) and maintaining employees’ privacy rights. CISOs across the world struggled to implement secure work-from-home policies and procedures to keep valuable data safe from cyberattacks. Many workers have shifted to using corporate virtual private networks to access secure documents—networks that cybercriminals quickly found ways to exploit. This increase in cyberattacks on remote workers led the FBI and Cybersecurity Infrastructure Security Agency (CISA) to issue multiple warnings throughout last year.
For better or worse, the effects of the virus are likely here to stay. The group of people who thought we would return to the office soon continues to shrink. About one-third of HR executives now believe 40% or more of their workforce will work remotely 12 months post-pandemic, according to a survey by The Conference Board. This means that the data privacy challenges COVID-19 has heightened won’t be alleviated any time soon.
Related: How COVID-19 is Changing Compliance Operations and How CISOs Should Respond
Changing policies
The data privacy landscape I mentioned earlier seems to paint a lot of doom and gloom, but in many ways it could actually have some good, outlasting benefits. There has been a lot of attention drawn to how our data is handled, and criticism is given when major companies haven’t met security and privacy standards. For example, Zoom was under intense scrutiny last year for its weak encryption strategy, causing the company to launch 90-day security revamp.
Politically, many Americans are looking to whether the U.S. will pass its own version of the General Data Protection Regulation (GDPR), a regulation that the European Union implemented to protect the privacy of EU citizens. This seems increasingly likely now that President Joe Biden has taken office, where his past involvement in the Obama administration included a Consumer Privacy Bill of Rights. In addition, Vice President Kamala Harris’ has also historically pushed for more data protection. During her tenure as California’s Attorney General, she introduced the California Online Privacy Protection Act (CalOPPA). This was later followed by the well-known California Consumer Privacy Act (CCPA).
In other states, proposals during the general election demonstrated that consumers are pining for more legal protection of their privacy. States like Massachusetts, where a new measure promised increased privacy protections for vehicle data, passed easily with 75% of voters. Michigan also voted to pass legislation that would require a warrant for electronic data searches, making it the 13th state to include data privacy protections within its state constitution.
New legislation—while being positive for both businesses and consumers—may be difficult for organizations to adjust to with current resources. Even prior to the pandemic, companies have been struggling to stay compliant with current laws and regulations. A Hyperproof survey of over 1,000 IT and compliance professionals found that 61% of respondents’ organizations have experienced a data breach or a privacy violation within the last three years. If this sounds like you, let us know and we’ll be more than happy to help your organization stay continuously compliant.
The most common data privacy regulations
Health Insurance Portability and Accountability Act (HIPAA) sets the standard for how patient information has to be handled by doctors’ offices, hospitals, insurance companies, and other businesses that handle personal health information. HIPAA requires that businesses that process patient data and providers (e.g., hospitals) safeguard patient information and only allow it to be disclosed in certain situations.
HIPAA provides four general rules that businesses must abide by, which are:
- Ensure the confidentiality, integrity, and availability of all e-PHI they create, receive, maintain or transmit;
- Identify and protect against reasonably anticipated threats to the security or integrity of the information;
- Protect against reasonably anticipated, impermissible uses or disclosures; and
- Ensure compliance by their workforce.
For more information about who needs to comply with HIPAA and what it takes to become HIPAA compliant, check out this guide.
The General Data Protection Regulation (GDPR) was enacted in 2018 to protect the rights of citizens in the EU when it comes to data collection and privacy. GDPR applies to companies that meet the following criteria:
- A presence in an EU country.
- No presence in the EU, but it processes the personal data of European residents.
- More than 250 employees.
- Fewer than 250 employees but its data-processing impacts the rights and freedoms of data subjects, is not occasional or includes certain types of sensitive personal data.
This means it effectively applies to almost all companies. It gives customers the right to know what data is being collected and sets requirements for how and when businesses must report breaches.
GDPR is one of the toughest data privacy regulations to comply with. It does allow for a tiered approach to fines and penalties based on the relative seriousness of the offense, but businesses shouldn’t count on leniency; in 2019, British Airways was fined $228 million and Marriott International was fined over $124 million for exposing millions of records of personal data.
For organizations operating in or serving the United Kingdom, it’s also essential to maintain compliance with the Data Protection Act and the UK implementation of GDPR. Together, these laws define how personal data must be collected, processed, and protected, and they sit alongside frameworks like CCPA, HIPAA, and GLBA in most global data privacy programs.
Payment Card Industry Data Security Standards (PCI-DSS) is somewhat unique, as it isn’t a government regulation and is imposed and enforced by an independent regulatory body, the Payment Card Industry Security Standards Council. Any business that accepts, stores, or transmits cardholder data is subject to PCI-DSS. This regulation requires businesses to have policies and processes in place to protect their customers’ information and ensure they’re properly handling and storing credit card data. This even applies to businesses that use third-party vendors to handle credit card payments. All businesses involved in eCommerce need to be well versed in these requirements and prepared to make sure their vendors are too.
The Sarbanes-Oxley Act of 2002 (SOX) was enacted in response to the Enron scandal, and it is required that publicly traded companies be in compliance. It is designed to prevent the kinds of fraud that occurred by setting requirements for retaining and storing business records and penalties for destroying, altering, or falsifying records.
This involves not only accounting to ensure that records are accurate, but also the IT function to store records correctly. SOX also requires a system for tracking changes to records and storing the right records for the right length of time.
The California Consumer Privacy Act (CCPA) applies to companies that do business in California and either 1) generate $25 million or more in annual revenue; 2) buy or sell the personal information of 50,000 or more consumers, households, or devices; or 3) earns more than half its annual revenue selling consumers’ personal data. The law allows any California resident to get a full list of the data a business has about them and entitles consumers to know who businesses have shared that data with. If a business violates the privacy guidelines in the CCPA, consumers are allowed to sue the business even if there hasn’t been a data breach.
The CCPA went into effect on January 1, 2020. Regulators can fine non-compliant businesses up to $7,500 per record affected. Enforcement will start as soon as the final regulations are in place, or by July 1, 2020 — whichever comes first. Additionally, individuals have the right to bring lawsuits against businesses for failing to protect user data (see Barnes v. Hanna Andersson, LLC).
With the disruptions the coronavirus has brought to organizations, some in the privacy space have questioned whether it’s right for California Attorney General Xavier Becerra to go forward with a July 1 enforcement. A coalition of 60 groups sent the attorney general a letter in late March calling for enforcement to be delayed. However, The California Attorney General’s office rebuffed any ideas of keeping the CCPA from taking full force and said “[they]’re committed to enforcing the law upon finalizing the rules or July 1, whichever comes first. “
For more details on what an organization needs to do to comply with the CCPA, check out this guide.
Nevada’s Senate Bill 220 went into effect in October of 2019, and it made Nevada the first state to follow in California’s footsteps and enact a data privacy law. The Bill requires that companies provide consumers either with a number they can call or an email request they can send to opt-out of having their data sold by that business. Nevada’s attorney general can impose fines of up to $5,000 for each violation, but consumers can’t bring action against non-compliant businesses under the bill.
There are some additional differences between Senate Bill 220 and the CCPA, like the fact that the Nevada Senate Bill doesn’t require a “Do Not Sell My Information” link, the differences in what information is covered, and a more limited definition of what is considered the “sale” of consumer data. However, this is still an important law for businesses to understand and become compliant with. More bills like this will likely be introduced in the coming years, and businesses need to be ready to meet them as they are voted into law.
The Gramm-Leach-Bliley Act (GLBA) was enacted in 1999 and requires companies that provide consumers with loans, financial or investment advice, insurance, or other financial products and services to explain their information-sharing and protection practices to their customers. It also requires companies to safeguard any sensitive data they collect from their customers. The GLBA requires financial institutions to have a written information security plan and have at least one employee designated to coordinate their program.
The penalties for violating the GLBA can be steep, with businesses facing fines of $100,000 for each violation and individuals facing a fine of $10,000 and up to 5 years in prison for being in violation of the Act.
The Computer Fraud and Abuse Act (CFAA) was passed in 1986 and makes intentionally accessing a computer without authorization a criminal act. Since then, it’s been amended and its scope has expanded to cover technological changes. Anyone who accesses a computer without authorization exceeds their authorized access, intentionally damages a computer, or uses a computer to commit extortion can be prosecuted under this act.
The penalties for violating the CFAA include prison time and range from one to 10 years. The CFAA also allows for civil actions in some situations, such as if physical injury or damage that affects a computer used by an entity of the United States occurs.
Data privacy risks
Businesses encounter numerous data privacy risks when they collect, process, and store personal data or personally identifiable information (PII). Some of the most common vulnerabilities and risks are listed below. To ensure data privacy compliance, companies should create operating procedures that maintain data privacy, educate their workforce, and add access control measures around personal data. For more information on PII, see “What Counts as Personally Identifiable Information is Expanding Under the Law.”
- Collecting and Storing Too Much Personal Information – Any time a company collects and stores personal data or PII they take on the responsibility to take care of the data and abide by the privacy regulations in place. To lessen data privacy risks, a business should only collect personal data that it truly needs and only store it if it needs it for future use. When not managed, copies of personal data can diffuse through an organization, so businesses should also control the practice of copying personal data.
- Using Personal Data for an Unauthorized Purpose – When collecting personal data, companies should be transparent about what data will be collected and how it will be used. Using the data for a different, hidden purpose, whether intentional or unintentional, would represent a compliance violation.
- Vulnerable Applications and Insufficient Data Security – Applications, including Web applications, on-premise applications, and legacy applications exposed to the Web through modern APIs, storing personal data should be secured. If not secured, personal data is at risk to be stolen or breached.
- Insufficient Procedures Around Access to Personal Data – The use or access of personal data should be restricted to those with a true need for the data. Access to applications, systems, and even specific data records that contain personal data should be restricted. Data privacy will be maintained not just through the presence of access controls, but also through healthy practices and controls around maintaining passwords and access, such as when an employee leaves the company.
- Insufficient Processes for Deleting Personal Data – Some regulations, such as GDPR, require companies to have procedures to delete personal data upon request. Procedures that do not remove or anonymize all personal data leave a company exposed to compliance violations and potential fines.
- Insufficient Responses Around Personal Data Loss – Some regulations, such as GDPR, require companies to inform people when their personal data has been stolen or accessed by unauthorized people. Procedures that do not adequately inform people within a required amount of time leave a company exposed to compliance violations and potential fines.
- Lack of Transparency Regarding Data Collection and Use – Data privacy regulations often require clear explanations of what personal data is collected and how personal data is used. This information needs to be publicly available and easily obtainable and usually resides in policy documents such as a privacy policy, cookie policy, and terms of use statement. Some regulations, such as GDPR, have requirements that companies must divulge all the personal data stored about a person if that person requests that information. Failure to have such policies and failure to respond to information requests in a timely manner will cause the company to fall out of compliance with the regulation.
- Sharing of Data with Third Parties – When collecting personal data, a company should specify how that data will be used, including with whom that data will be shared. If personal data is collected and shared with a third party, such as an advertising/marketing partner or subcontractor, without the owner’s knowledge and consent, that would constitute a compliance violation.
- Insecure Data Transfers – Personal data should be secured at all times, including when it is being transported from one system to another. This is typically accomplished through secure data communication standards such as SSL.
- Adapting Data Privacy Policies as Business Demands Change – To ensure compliance, businesses ought to revisit their data privacy policies and operating procedures whenever they make new business decisions, such as selling through a new channel, bringing on new third parties, launching a new product, or opening new offices in new states or countries. In addition, businesses also need to think through the privacy implications when they roll out new operating procedures in times of disruption. One example is around bringing employees safely back into physical workplaces in the midst of the COVID-19 pandemic. A company should be aware that they are collecting personal data when they take body temperature readings to ensure an employee doesn’t have COVID-19 or ask employees about their personal activities as part of a contact tracing program. For more information on key privacy considerations around transitioning employees back into physical workspaces, check out this on-demand webinar
Implementing a data privacy compliance program
To abide by data privacy regulations consistently, you need to have a data privacy policy and a robust privacy compliance program. A clear data compliance policy is the foundation for data protection compliance and long-term data security and privacy compliance, because it defines how personal data is collected, used, shared, retained, and deleted. A modern program should cover both data protection and privacy compliance requirements across all jurisdictions where you operate. Below are the steps to creating and implementing a data privacy compliance program.

1. Determine which data privacy regulations apply to your business
If you don’t have internal data privacy experts, you’ll want to consult with external legal experts as well as consulting firms to help you determine which data privacy regulations apply to your business, and how to feasibly comply with the regulations.
As technology changes or new ones emerge (e.g. facial recognition algorithms), legislators and regulatory bodies will update regulations to enhance the protection of consumers. Your organization should make a concerted effort to stay abreast of regulatory changes in the data privacy realm. You can do so by joining industry associations such as the International Association of Privacy Professionals, the world’s largest and most comprehensive global information privacy community.
2. Establish a data privacy policy
The first thing your business needs to understand as you begin building your data privacy policies and procedures is what exactly your data privacy policy needs to address. Start by clearly understanding who you’re marketing and selling to. Ask questions like:
- Who is the user of the product?
- What information about the users will you be collecting?
- What is your business trying to do with the information you collect?
- What is the sensitivity level of the information?
You’ll want to start with a data inventory that includes all of the consumer data that you collect so you have a central record of what you have collected and where it is being stored.
You also need to understand and indicate in your data inventory, the sensitivity of the information you’re collecting. Do you have highly sensitive information, like personal health information or social security numbers?
Finally, how will your revenue model utilize the consumer data you are collecting? How are you looking to sell data or monetize data? What do the privacy laws you’re subject to allow or not allow? How will those laws affect your ability to sell consumer data, and what do you have to offer consumers in terms of opting in or out of the sale of their data?
As more data privacy laws are passed and go into effect, your business will have more data privacy obligations to your consumers, so it’s crucial that you have a thorough data privacy policy guiding your operations.
3. Implement data privacy and cybersecurity frameworks and auditing procedures
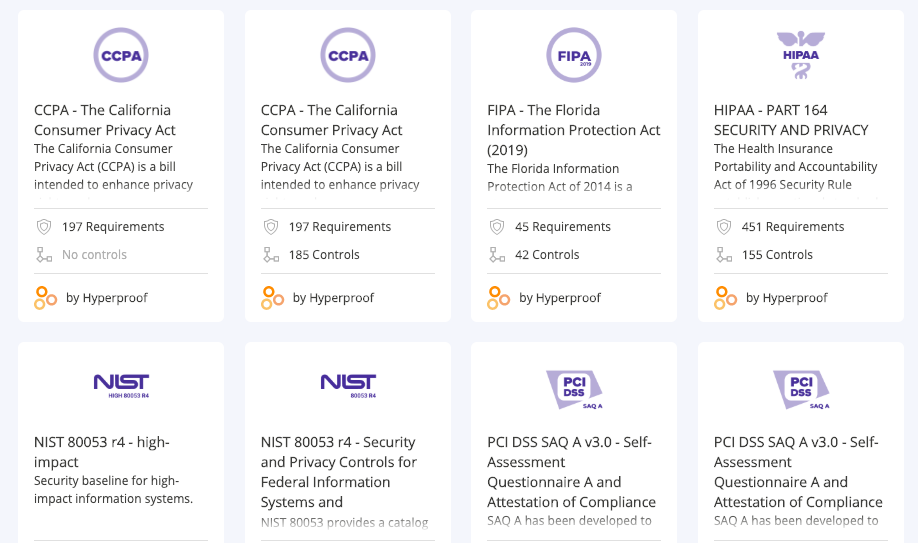
You shouldn’t be doing any guesswork when it comes to data security and data privacy. At this time, there are a number of well-regarded and well-adopted cybersecurity and data protection and privacy compliance standards on the market. A data privacy compliance framework gives you a repeatable way to map regulations (like GDPR or CCPA) to controls, evidence, and audit-ready processes—so privacy isn’t handled differently by every team. These compliance standards and auditing procedures (e.g., SOC 2, NIST 800-53, ISO 27001) provide detailed catalogs of privacy and security controls that businesses could put in place to secure their customers’ data and ensure data confidentiality.
For example, SOC 2, an auditing procedure developed by the American Institute of CPAs (AICPA) defines criteria for managing customer data based on five “trust service” principles” — security, availability, processing integrity, confidentiality, and privacy. If your organization collects, transmits, uses, or stores personal information, you may benefit from going through a SOC 2 audit for privacy and data security, to gain confidence that your customers’ personal information is protected and to provide assurance to potential customers that it has controls in place to protect customers’ personal information.
ISO/IEC 27701 is another privacy framework worth considering because it was specifically developed to help organizations conform to the GDPR. If your business is required to be GDPR compliant, ISO/IEC 27701 provides an extensive list of guidelines that will help you as your company begins working towards GDPR compliance.
ISO 27001 is an additional family of standards your organization may choose to comply with because ISO 27001 provides a comprehensive list of steps businesses can take to shore up security and ensure that their security processes can prevent unauthorized access to user data.
To ensure that your data protection practices are robust enough to keep your information assets safe, you’ll want to become familiar with these compliance frameworks, evaluate how your internal controls stack up against the best practices put forth within these IT compliance standards, identify the gaps, and implement new policies and procedures to close the gaps in your environment.
Again, if you’re implementing a cybersecurity or data privacy standard for the first time, you’ll want to get help from qualified consultants, software vendors with expertise in this realm, and auditors.
3. Conduct internal audits on a regular basis
For businesses complying with multiple cybersecurity and data privacy regulations, having an internal auditing practice in place is crucial. Putting a dedicated professional in charge of auditing your compliance processes and giving them access to the right tools is the best way to spot possible issues and prevent disasters like a major data breach from happening.
Related: Understanding and Executing Compliance Audits
4. Keep detailed records of your compliance activities
One of the best ways to protect your company from the legal consequences (e.g., fines and penalties) of non-compliance is to keep detailed records of your compliance activities. For teams managing multiple regulations, data privacy compliance software helps centralize evidence, automate reminders, and keep control testing on schedule without chasing updates across spreadsheets. To illustrate this point, let’s take a look at the CCPA. The CCPA makes a clear distinction between willful non-compliance vs. unintentional non-compliance. Those who are found to be willfully negligent will pay a higher penalty: $7500 per violation per user vs. $2500 per violation in unintentional non-compliance cases. Being able to quickly demonstrate compliance can save your business a significant sum of money if your business were found to be in violation and investigated by the California Attorney General.
Even with a strong compliance program in place, the risk of a data breach or other violations is always present. Having a detailed record of your compliance efforts ready at your fingertips will help you demonstrate that you take that risk seriously and are actively working to mitigate it.
Related: Evidence Collection: Why It’s a Key Pillar of an Effective Compliance Program
Data privacy and your business
Data privacy is critical to the survival of modern businesses, and organizational leaders should embed it into all processes or policies that touch consumer data within your company. No matter what size your business is, how mature your compliance program is, or how many people are on your compliance team, most businesses have room for improvement when it comes to data privacy and the way they handle data protection and privacy compliance over time.
Take some time, sooner rather than later, to evaluate your company’s data privacy policies and practices to make sure you’re utilizing all the resources at your disposal to protect your clients’ data, your business’ bottom line, and your customers’ trust in your company.
Hyperproof’s continuous compliance software was available at no cost during the COVID-19 crisis
To help organizations stay compliant with disparate data privacy regulations during this challenging time, Hyperproof is offering our continuous compliance software subscription at no cost. This offer includes Hyperproof’s core platform and two compliance templates focused on privacy mandates passed in the United States and European Union: The California Consumer Privacy Act (CCPA) and The General Data Protection Regulation (GDPR). Hyperproof is making these programs available due to the increasing amount of personally identifiable information that needs to be exchanged at record speeds in order to protect our communities.
Contact Hyperproof here to receive a no-cost subscription during the coronavirus crisis.
See Hyperproof in Action
Related Resources
Ready to see
Hyperproof in action?











